3.1 Million Armenian Citizens' Data Allegedly for Sale on Dark Web

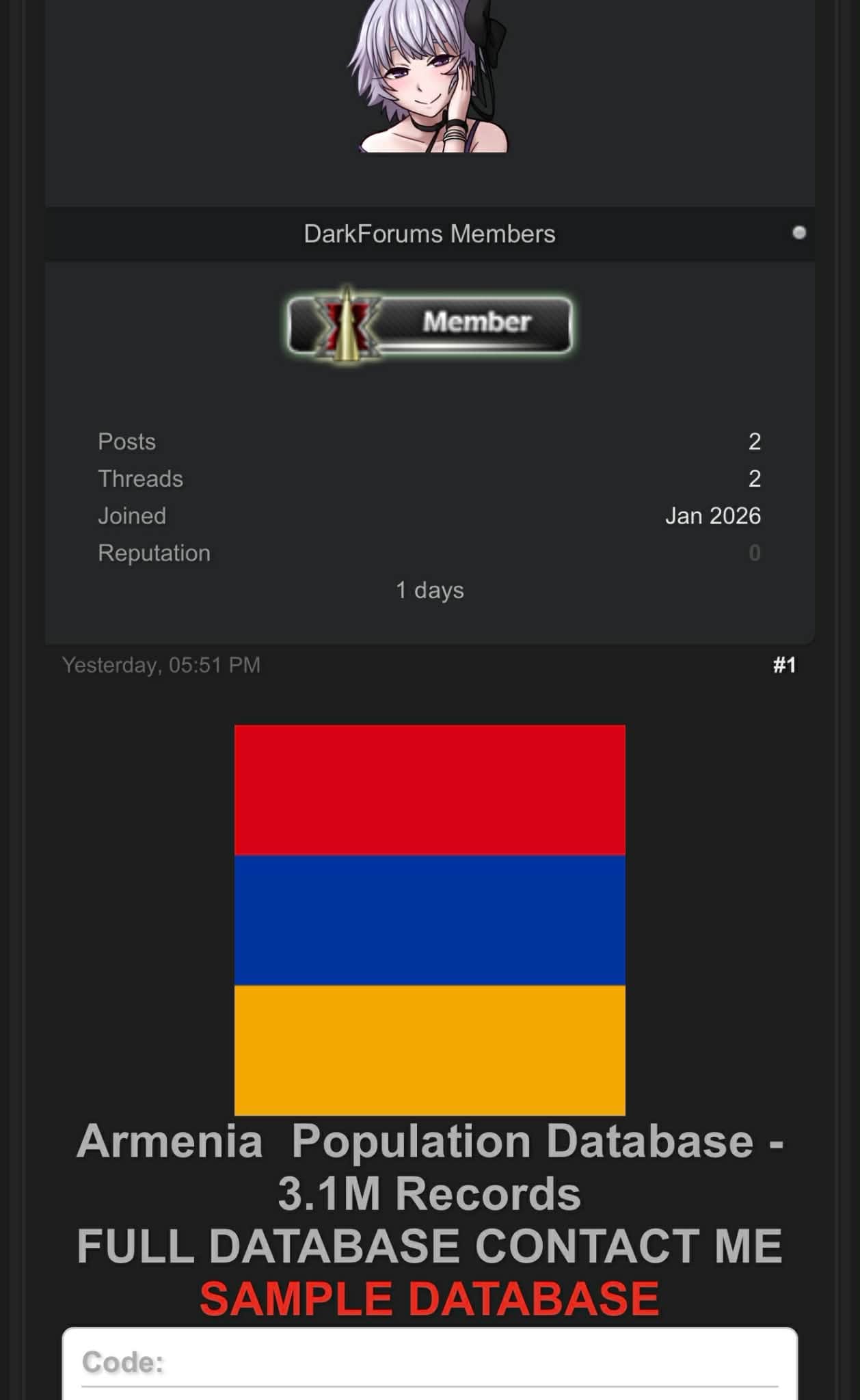
A threat actor using the alias "datsell_alld" claims to be selling a database containing approximately 3.1 million records of Armenian citizens on a dark web forum.
With Armenia's population estimated at just over 3 million, the claimed size suggests this could represent a near-complete national dataset.
What's Allegedly Exposed
The dataset reportedly includes:
- Social Security Numbers (SSN)
- Passport numbers
- Full names (first, last, and patronymic)
- Dates of birth
- Document issuance or registration dates
- Full residential addresses
Sample data has allegedly been provided to potential buyers to demonstrate authenticity.
Why This Matters
If legitimate, this breach would be one of the most significant data exposures in Armenia's history. Core identity data like SSNs and passport numbers cannot be easily changed, creating long-term risks including:
- Identity theft and financial fraud
- Document forgery and passport abuse
- Targeted phishing and social engineering campaigns
The listing was posted by a relatively new forum account, which may indicate either a newly established actor or an attempt to minimize traceability.
Official Response
Armenian authorities have not publicly commented on the alleged breach. The original source of the data - whether government systems, a third-party contractor, or aggregated legacy databases - remains unknown.



