Affirm Data Breach Allegedly Exposes 26.7 Million User Records on Dark Web
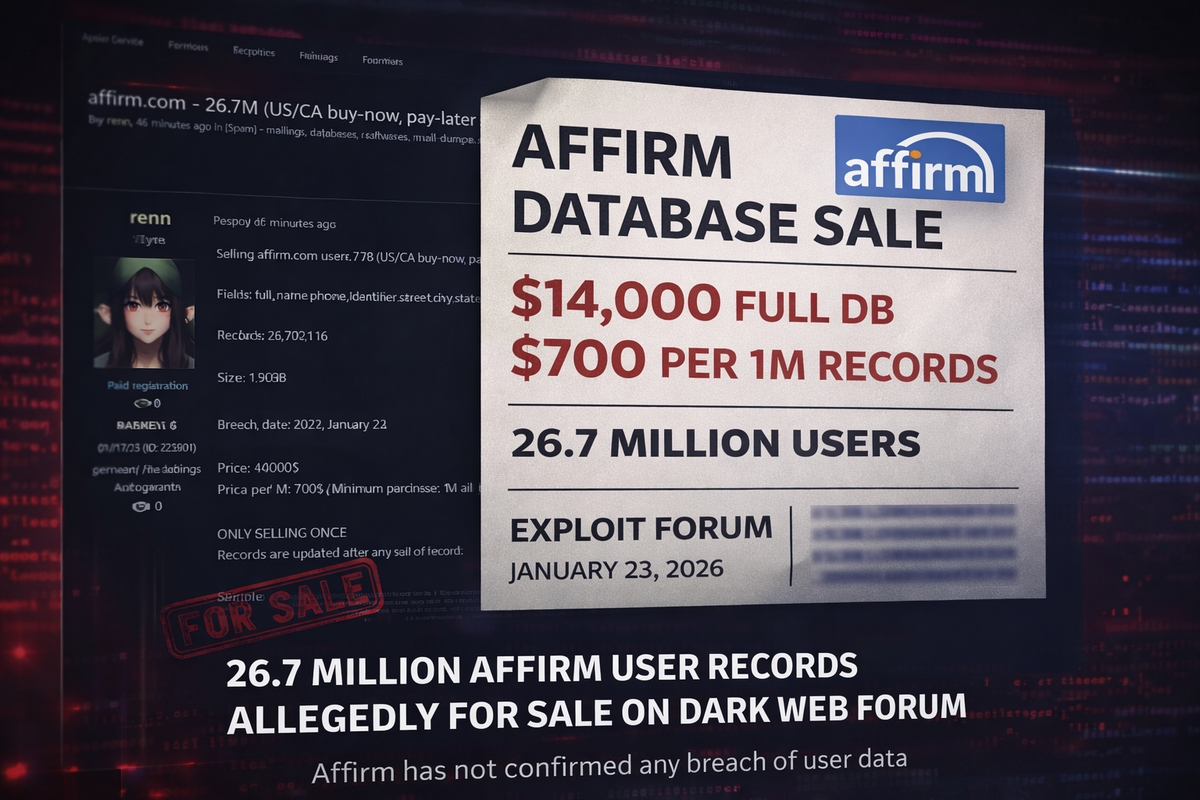
A threat actor is allegedly selling a database containing 26.7 million user records from Affirm, the popular buy-now-pay-later financial services platform operating in the United States and Canada.
The listing appeared on the Exploit cybercrime forum on January 23, 2026, posted by a threat actor using the handle "renn." The seller claims the 1.9GB database was obtained the same day and is offering the complete dataset for $14,000 or $700 per million records with a minimum purchase of one million lines.
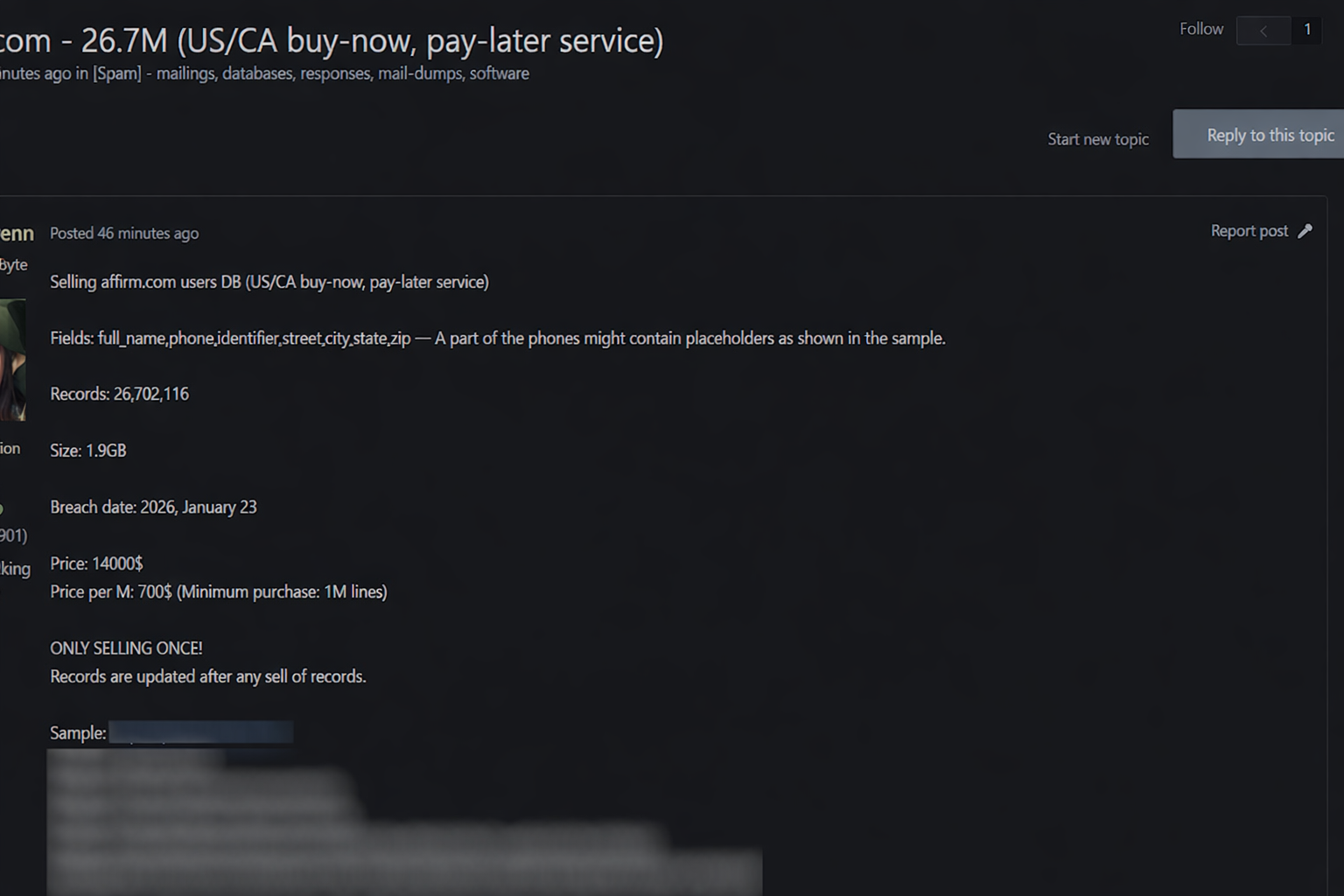
Sale Details
According to the forum post, the database contains over 26.7 million records. The threat actor notes that some phone numbers in the dataset may contain placeholder values. The listing emphasizes the data will only be sold once, with records updated after any sale.
Affirm provides installment payment services to consumers making purchases at major retailers and e-commerce platforms. The company went public in 2021 and serves millions of customers across North America.
Unverified Claims
The authenticity of the alleged breach has not been independently verified. Affirm has not publicly confirmed any security incident. Organizations monitoring dark web forums have flagged the listing, but the claims remain unsubstantiated until further evidence emerges.
Affirm users concerned about potential exposure should monitor their accounts for suspicious activity and consider enabling additional security measures where available.
This story will be updated if Affirm releases a statement or additional details emerge.



