Anubis Ransomware Introduces Wiper Mode That Destroys Data Even After Payment
A ransomware-as-a-service operation called Anubis is challenging a core assumption of ransomware response: that paying the ransom guarantees data recovery. The group has introduced an optional wiper mode that permanently destroys files, making decryption impossible regardless of payment.
First observed in late 2024, Anubis emerged on Russian-language cybercrime forums including RAMP and XSS. Code analysis links it to an earlier build known as Sphinx, indicating a direct rebrand rather than a new development effort.
Beyond Traditional Ransomware
What distinguishes Anubis from most ransomware families is its flexibility. The operation treats encryption, data theft, access resale, and data destruction as interchangeable tools rather than sequential steps.
Affiliates can choose between:
- Standard file encryption with ransom demands
- Data-only extortion without deploying ransomware
- Selling compromised network access to other threat actors
- Activating wiper mode to permanently destroy data
This model gives affiliates unprecedented control over how they monetize intrusions based on victim profile and operational risk.
Wiper Mode Changes the Calculus
When wiper mode is activated, files are overwritten rather than encrypted. Recovery becomes impossible even if the victim pays. This capability positions Anubis closer to destructive malware than traditional ransomware and significantly escalates risk for victims.
The inclusion of a wiper option may serve multiple purposes—punishing non-payment, creating urgency during negotiations, or enabling politically motivated destruction disguised as criminal activity.
Technical Operations
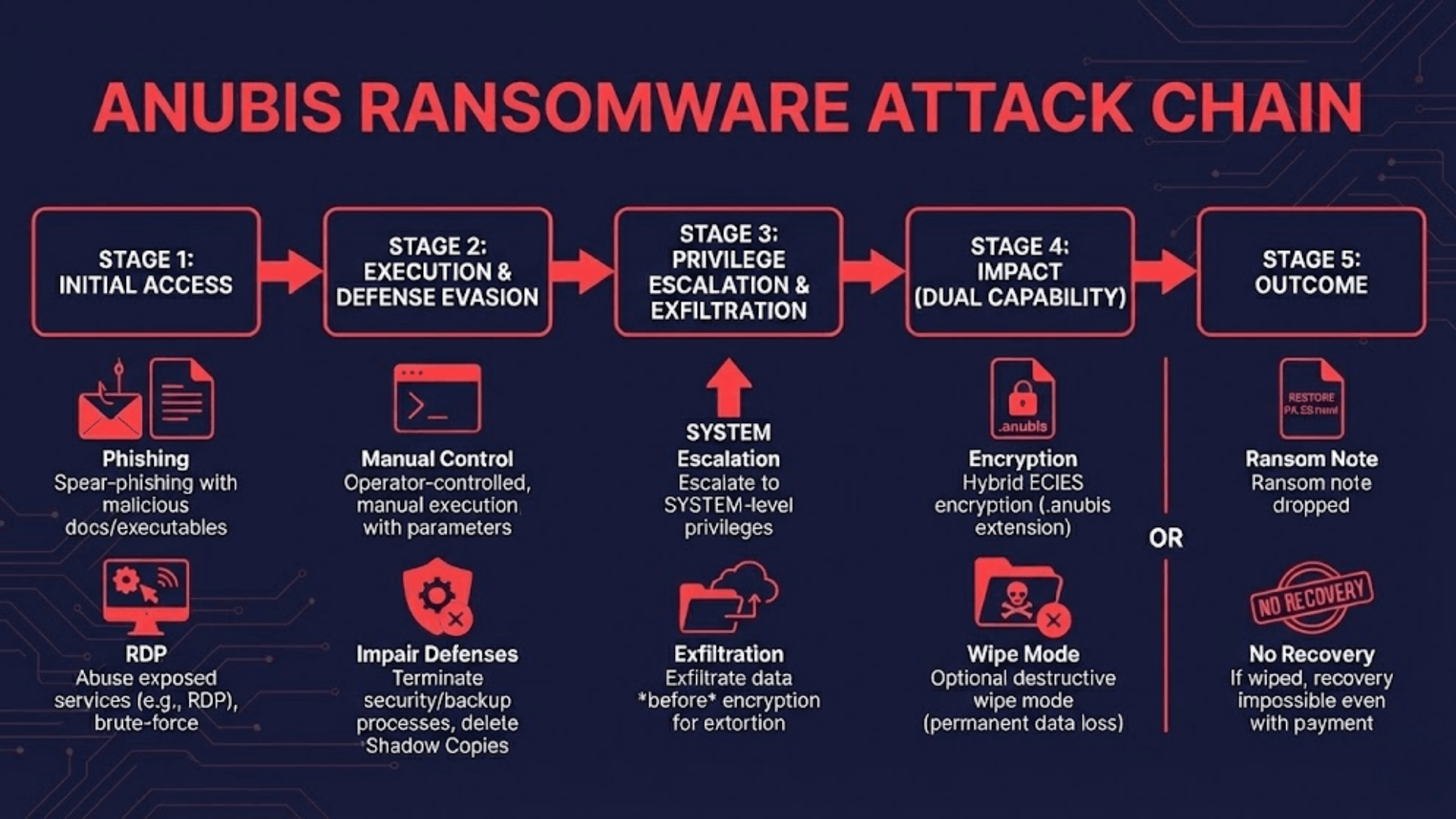
Anubis follows a manual, operator-controlled execution model. Affiliates deploy payloads only after achieving sufficient access, privileges, and data visibility inside target environments.
Initial access typically occurs through spear-phishing emails (T1566), exposed RDP services (T1133), compromised credentials (T1078), or trojanized software installers. The ransomware requires explicit command-line parameters to function (T1059), confirming it is designed for hands-on affiliate control rather than autonomous spread.
Once executed, Anubis attempts privilege escalation (T1548.002) and uses access token manipulation (T1134) to reach SYSTEM-level permissions. The malware then:
- Terminates security tools, backup software, and database processes (T1562.001)
- Deletes Volume Shadow Copies and disables Windows recovery options (T1490)
- Removes system artifacts to hinder forensic analysis (T1070)
- Encrypts files using hybrid ECIES cryptography, appending the .anubis extension (T1486)
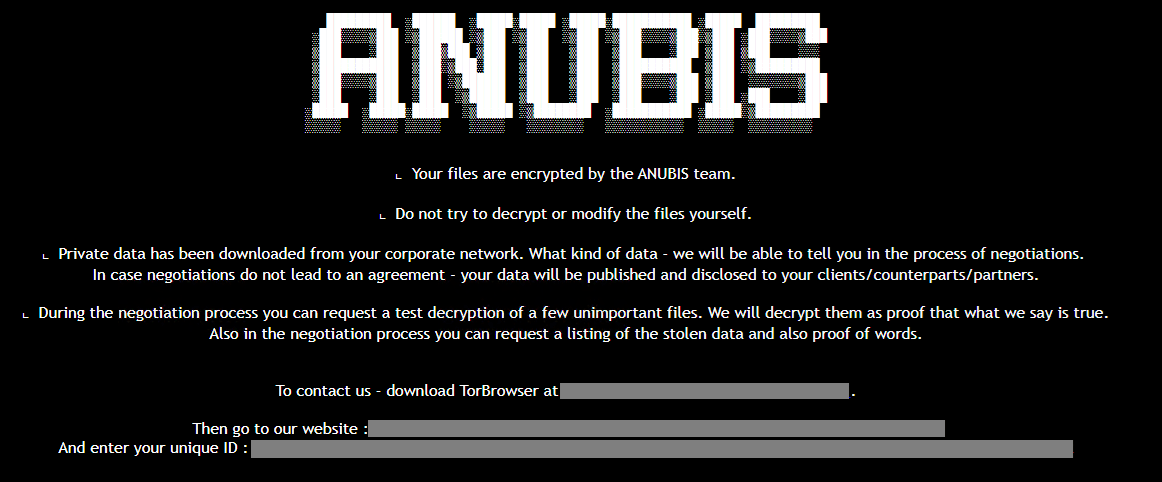
- Drops HTML ransom notes titled "RESTORE FILES.html" with Tor-based contact instructions
Data exfiltration (T1048, T1567) occurs before encryption using separate tools or legitimate transfer utilities. Stolen data is later leveraged through Anubis-operated Tor leak sites.
Targeting Patterns
Anubis consistently excludes former Soviet states, a behavior common among Russian-aligned RaaS operations. Activity has been observed across healthcare, engineering, and construction sectors in North America, Europe, and parts of Asia-Pacific—environments holding high-value or regulated data.
Affiliate Economics
The standard revenue split heavily favors affiliates, with approximately 80% of ransom proceeds going to operators handling the intrusion. Additional monetization channels include a data extortion program for standalone blackmail and an access broker channel for selling network access without deploying ransomware.
Indicators of Compromise
- File extension:
.anubis - Ransom note:
RESTORE FILES.html - Binary type: Statically compiled Go payloads with in-memory decryption
- Infrastructure: Tor-based leak sites and negotiation portals
- Forum presence: RAMP, XSS
Defensive Recommendations
Organizations should prepare for scenarios where recovery may not be possible:
- Maintain immutable or offline backups that cannot be deleted even with administrative privileges
- Monitor for pre-encryption indicators including mass service termination, shadow copy deletion, and unusual outbound transfers
- Enforce MFA on all remote access and administrative accounts
- Prioritize patching for internet-facing services, especially RDP and VPN infrastructure
- Prioritize early containment—waiting until encryption begins may be too late



