Venezuelan Nationals Convicted in ATM Jackpotting Scheme Using Ploutus Malware
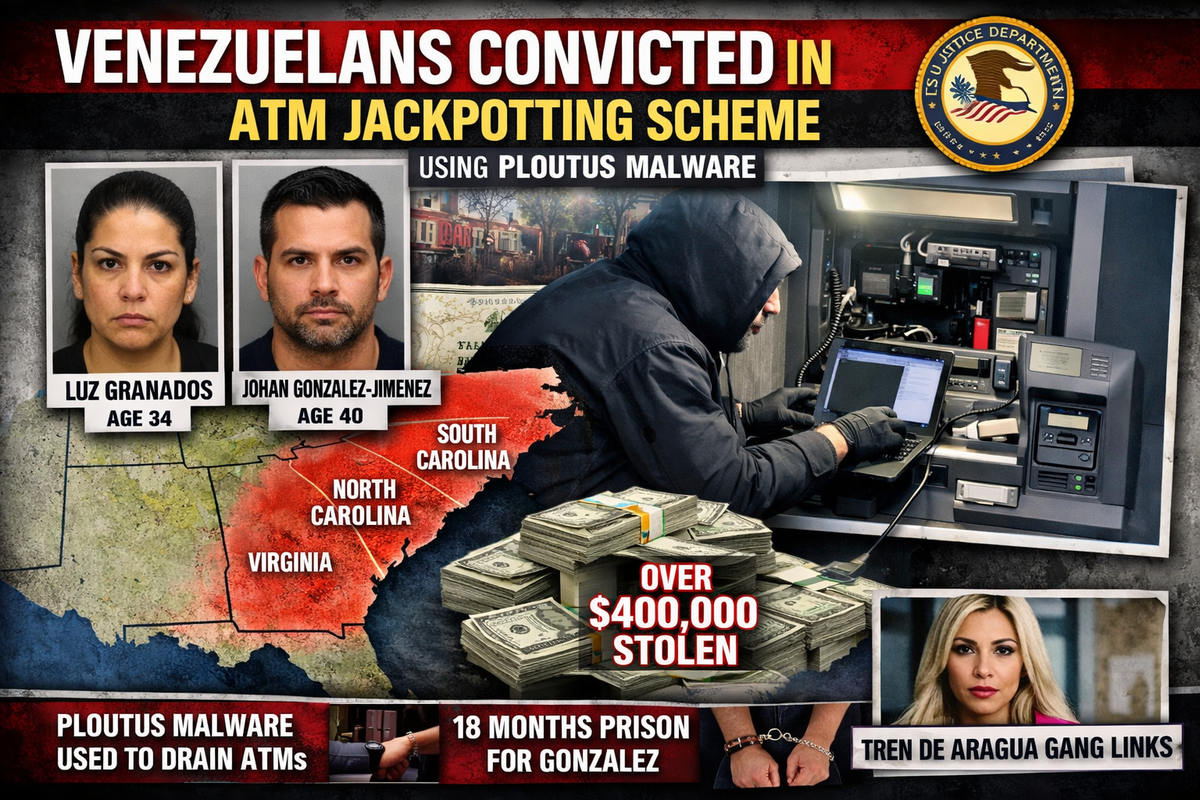
Two Venezuelan nationals have been convicted for their roles in an ATM jackpotting scheme that used Ploutus malware to empty cash machines across the southeastern United States.
Luz Granados, 34, and Johan Gonzalez-Jimenez, 40, pleaded guilty to conspiracy and computer crimes for targeting older ATM models in South Carolina, Georgia, North Carolina, and Virginia. All stolen funds came directly from the banks rather than individual customer accounts.
Attack Methodology
The attackers approached ATMs at night, removed the outer casing, and connected laptops to install malware that bypassed security protocols. Once deployed, the malware forced the machines to dispense cash until completely emptied.
According to the Justice Department, the defendants deployed Ploutus malware variants through multiple methods—removing the ATM's hard drive and installing it directly, using external devices like thumb drives, or replacing the hard drive with one already infected. The malware also deleted evidence to conceal attacks from bank employees.
Sentencing and Deportation
U.S. District Judge Mary Geiger Lewis sentenced Gonzalez-Jimenez to 18 months in federal prison and ordered him to pay $285,100 in restitution before deportation. Granados received time served and was ordered to pay $126,340, and remains in custody awaiting deportation.
Five other Venezuelan nationals were also sentenced or pleaded guilty last month for involvement in ATM jackpotting thefts across multiple states and face immediate deportation.
Broader Conspiracy
Evidence from the South Carolina investigation was shared with Nebraska authorities, leading to a federal grand jury indicting 54 individuals in a related ATM jackpotting conspiracy allegedly responsible for stealing millions from ATMs nationwide.
The Nebraska indictments include Jimena Romina Araya Navarro, an alleged leader of the Tren de Aragua Venezuelan gang, who was sanctioned by the Treasury Department's Office of Foreign Assets Control in December.



