China-Aligned APT Groups Deploy PeckBirdy JScript Framework for Fileless Attacks on Government Targets

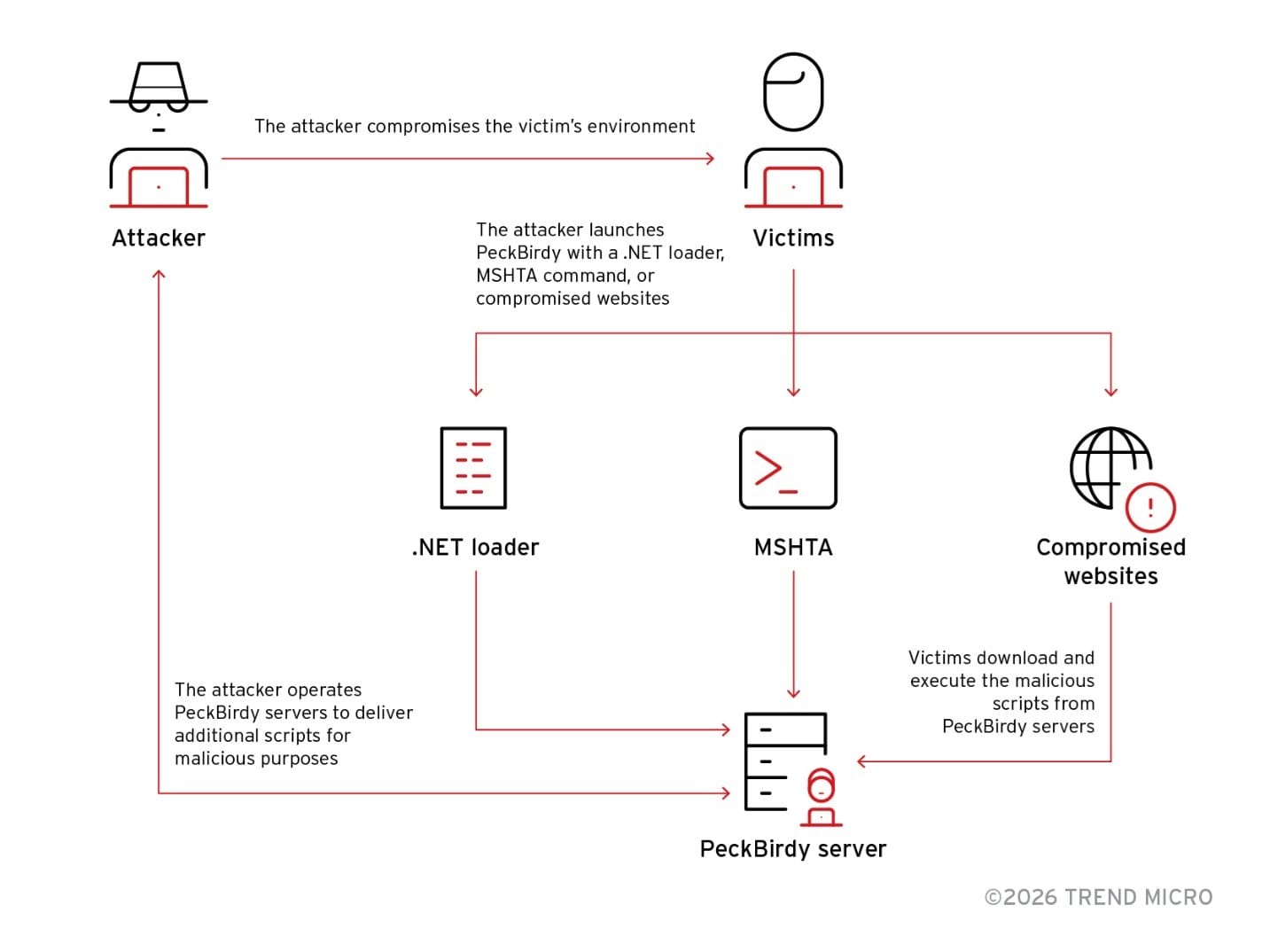
China-aligned advanced persistent threat groups have been using a previously undocumented JScript-based command-and-control framework called PeckBirdy to conduct fileless attacks against Asian government entities, educational institutions, and Chinese gambling operations since 2023, according to research published by Trend Micro.
PeckBirdy is built entirely in JScript and leverages the Windows Script Host to execute commands without dropping files that antivirus software might detect. By injecting code dynamically at runtime, the framework leaves almost no physical footprint on compromised systems.
Fileless Execution Evades Detection
The framework's design prioritizes stealth over capability. Trend Micro researchers noted that detecting malicious JavaScript frameworks remains a significant challenge due to their use of dynamically generated, runtime-injected code and the absence of persistent file artifacts.
PeckBirdy enables flexible deployment across multiple environments, allowing attackers to execute commands on compromised systems while maintaining minimal forensic evidence. The lightweight nature of the script-based framework makes it particularly difficult for traditional security tools to identify and block.
Modular Backdoors Extend Capabilities
PeckBirdy rarely operates alone. Researchers identified two modular backdoors deployed alongside the framework: HOLODONUT and MKDOOR. These modules extend PeckBirdy's attack capabilities beyond its core functionality, allowing attackers to maintain persistent access and exfiltrate sensitive data from compromised networks.
The modular architecture enables threat actors to customize their toolset based on target environments and operational requirements while keeping the core C2 framework lightweight and evasive.
Two Campaigns Identified
Trend Micro's investigation linked PeckBirdy to at least two specific campaigns targeting organizations in Asia.
The first campaign, tracked as SHADOW-VOID-044, utilized stolen code-signing certificates and standard Cobalt Strike payloads to breach targets. The attackers exploited CVE-2020-16040 and hosted malicious infrastructure across multiple domains to maintain resilience against takedowns.
The second campaign, SHADOW-EARTH-045, struck a Philippine educational institution in July 2024. Attackers executed an MSHTA command, a classic fileless technique, to connect to github[.]githubassets[.]net and launch PeckBirdy on a compromised IIS server. The use of GitHub-hosted infrastructure demonstrates the threat actors' efforts to blend malicious traffic with legitimate services.
Links to Known China-Aligned Groups
Researchers found tentative connections between these attacks and known China-aligned threat groups including Earth Lusca and Earth Baxia, though definitive attribution remains complex.
An IP address used in the Philippine attack, 47[.]238[.]184[.]9, had previously been linked to Earth Baxia operations. Earth Lusca has been active since at least 2021, targeting government organizations, educational institutions, and technology companies across Asia with espionage-focused campaigns.
The overlapping infrastructure and tactics suggest potential tool sharing or operational coordination among China-aligned APT groups, though the exact relationships between these threat actors remain unclear.
Recommendations
Organizations should monitor for suspicious Windows Script Host activity and MSHTA command execution, which are common indicators of fileless attack techniques. Security teams should implement behavioral detection capabilities that can identify malicious script execution patterns rather than relying solely on file-based signatures.
Network monitoring for connections to unexpected GitHub endpoints and other legitimate services that may be abused for C2 communication can help identify PeckBirdy and similar frameworks. Organizations in the government, education, and gambling sectors in Asia should be particularly vigilant given the observed targeting patterns.



