Chinese APT Lotus Blossom Hijacked Notepad++ Updates for Six Months, Deploying New Chrysalis Backdoor
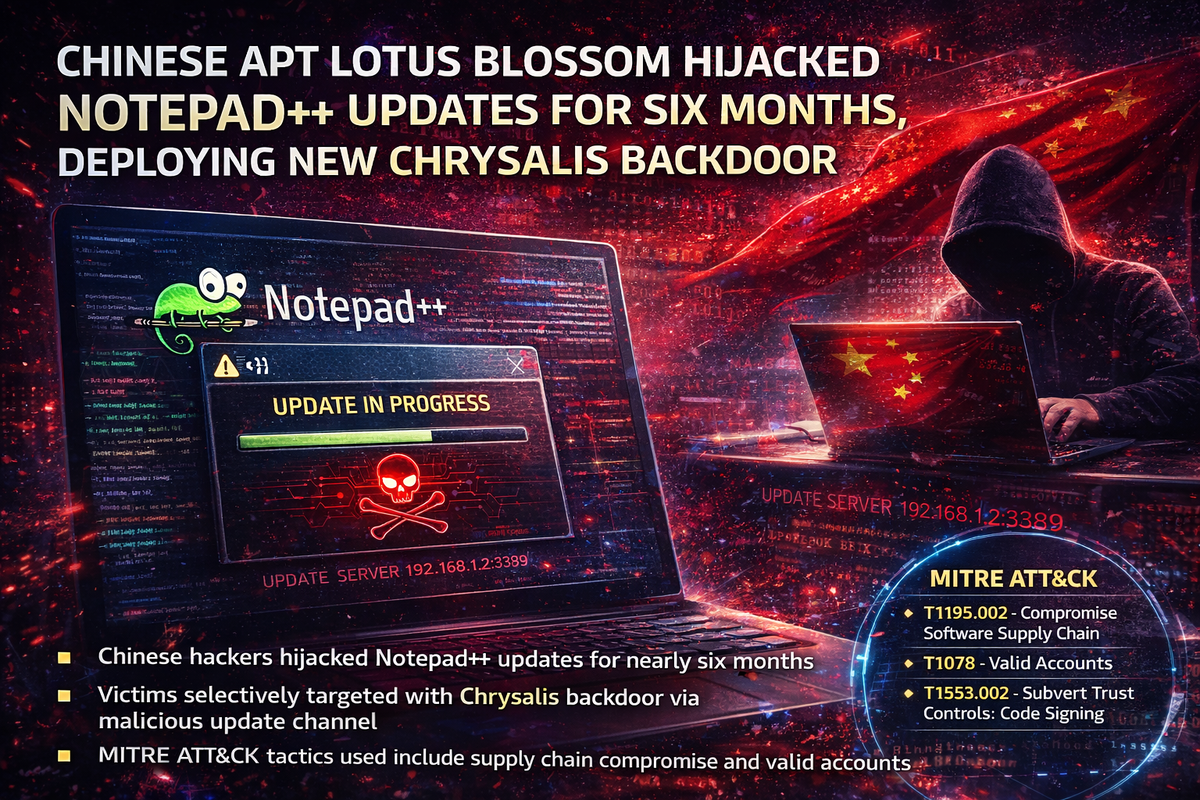
Chinese state-sponsored threat actors compromised the update infrastructure for Notepad++, the popular open-source text editor with tens of millions of Windows users, and maintained access for nearly six months while selectively targeting victims with malicious updates.
The Notepad++ development team confirmed the breach today, stating that attackers intercepted update requests from specific users and redirected them to attacker-controlled servers serving tampered update manifests. The campaign exploited insufficient verification controls in older versions of the WinGUp update tool.
Rapid7 researchers attribute the operation to Lotus Blossom (also tracked as Raspberry Typhoon, Bilbug, and Spring Dragon), a Chinese APT group known for targeting government and military organizations across Southeast Asia. The researchers discovered a previously undocumented backdoor they've named Chrysalis being deployed through the compromised update channel.
Attack Timeline
The compromise began in June 2025 when threat actors gained access to a hosting provider server running the Notepad++ update application. Rather than pushing malware to all users, the attackers implemented selective targeting — redirecting only specific update requests to their infrastructure while allowing legitimate traffic to proceed normally.
In early September, the attackers temporarily lost access when the hosting provider updated the server kernel and firmware. However, they regained their foothold using previously obtained internal service credentials that had not been rotated.
The intrusion continued until December 2, 2025, when the hosting provider finally detected the breach and terminated access — a total dwell time of approximately five and a half months.
Chrysalis Backdoor
Rapid7's technical analysis reveals Chrysalis as a sophisticated, full-featured backdoor designed for long-term persistence. The researchers note the malware's extensive capability set suggests it's intended as a permanent implant rather than a first-stage loader.
The confirmed execution chain shows notepad++.exe launching GUP.exe (the update tool), which then spawned a suspicious update.exe process. Researchers note they found no definitive artifacts confirming the exact exploitation mechanism.
Security researcher Kevin Beaumont reported awareness of at least three organizations affected by the update hijacks, with hands-on keyboard activity observed on compromised networks following initial access.
Remediation
Notepad++ version 8.8.9, released in December, addressed the verification weakness by implementing installer certificate and signature verification along with cryptographic signing of the update XML manifest. Version 8.9.2, expected in approximately one month, will enforce mandatory certificate verification.
The development team has migrated to a new hosting provider and rotated all potentially compromised credentials.
Recommended actions:
- Update to Notepad++ 8.8.9 or later immediately
- Rotate SSH, FTP/SFTP, and MySQL credentials on systems where Notepad++ was installed
- Review Rapid7's technical analysis for Chrysalis behavioral indicators
- Monitor for post-exploitation activity on systems that ran vulnerable versions during the campaign window (June–December 2025)
No IOCs have been released — the developer stated that requests to the former hosting provider for indicators were unsuccessful.
MITRE ATT&CK
T1195.002 — Compromise Software Supply Chain Hijacking update infrastructure to deliver malicious payloads
T1078 — Valid Accounts Reusing stolen credentials to regain access after partial eviction
T1553.002 — Subvert Trust Controls: Code Signing Exploiting insufficient update verification



