CISA Adds Actively Exploited Ivanti EPMM Vulnerability to KEV Catalog (CVE-2026-1281)
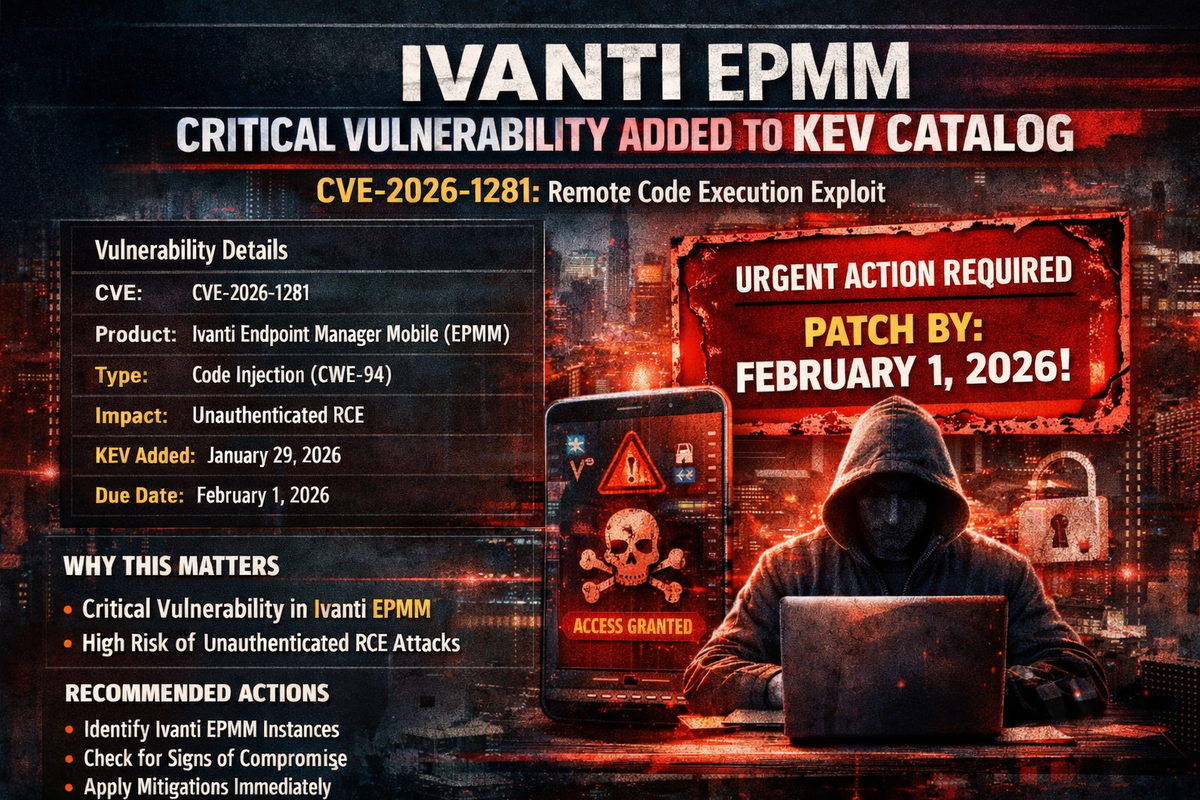
CISA has added a critical Ivanti Endpoint Manager Mobile (EPMM) vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
Tracked as CVE-2026-1281, the code injection vulnerability allows attackers to achieve unauthenticated remote code execution on affected systems.
Urgent Deadline
Federal agencies are required to apply mitigations by February 1, 2026—just three days from the January 29 catalog addition. Organizations outside the federal government should treat this timeline with equal urgency.
Vulnerability Details
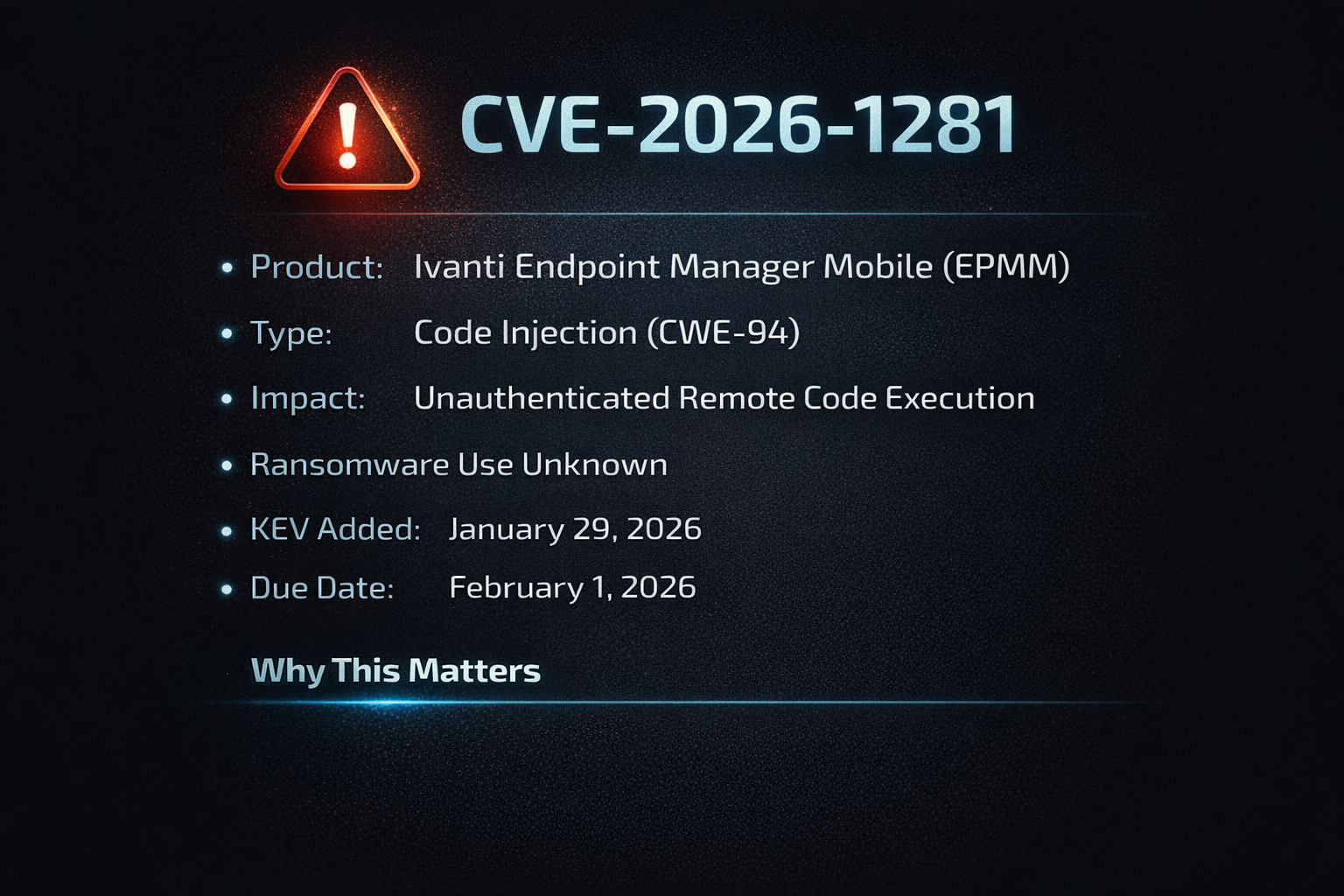
Why This Matters
Ivanti products have been repeatedly targeted by threat actors, including nation-state groups. EPMM (formerly MobileIron Core) is widely deployed for enterprise mobile device management, making it a high-value target for attackers seeking initial access to corporate networks.
Recommended Actions
- Identify all Ivanti EPMM instances in your environment
- Check for signs of compromise on internet-accessible Ivanti products
- Apply vendor mitigations immediately
- If mitigations are unavailable, consider discontinuing use until patched



