CISA Adds Four Vulnerabilities to KEV Catalog Including Critical SmarterMail Authentication Bypass
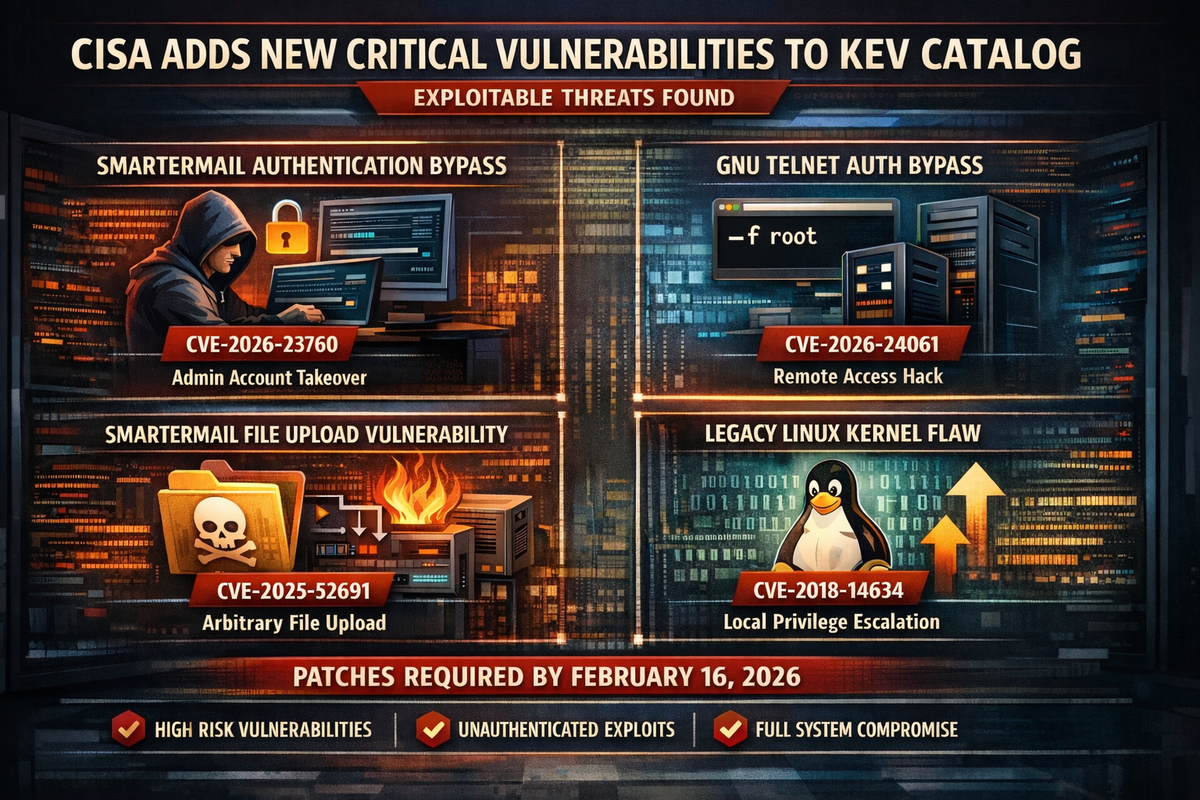
CISA has added four vulnerabilities to its Known Exploited Vulnerabilities catalog, including two critical flaws in SmarterTools SmarterMail that could allow unauthenticated attackers to achieve full administrative compromise of mail servers. Federal agencies must apply mitigations by February 16, 2026.

Critical SmarterMail Authentication Bypass
The most severe addition is CVE-2026-23760, an authentication bypass vulnerability in SmarterMail's password reset API. The force-reset-password endpoint permits anonymous requests and fails to verify the existing password or reset token when resetting system administrator accounts.
This allows an unauthenticated attacker to supply a target administrator username and new password to reset the account, resulting in complete administrative takeover of the SmarterMail instance. The vulnerability is classified as CWE-288: Authentication Bypass Using an Alternate Path or Channel.
SmarterMail Arbitrary File Upload
The second SmarterMail vulnerability, CVE-2025-52691, enables unrestricted upload of dangerous file types. An unauthenticated attacker can upload arbitrary files to any location on the mail server, potentially enabling remote code execution. The flaw is classified as CWE-434.
Organizations running SmarterMail should apply patches immediately as both vulnerabilities can be exploited without authentication and provide significant access to compromised systems.
GNU InetUtils Telnet Authentication Bypass
CVE-2026-24061 affects GNU InetUtils telnetd, containing an argument injection vulnerability that enables remote authentication bypass. Attackers can bypass authentication by supplying a "-f root" value for the USER environment variable, classified as CWE-88: Argument Injection.
This vulnerability affects an open-source component used across multiple products. Organizations should check with specific vendors for patching status and consider disabling telnetd where not required.
Legacy Linux Kernel Vulnerability
CISA also added CVE-2018-14634, an integer overflow vulnerability in the Linux kernel's create_elf_tables() function dating from 2018. The flaw allows an unprivileged local user with access to SUID or otherwise privileged binaries to escalate privileges on the system.
The addition of this older vulnerability indicates active exploitation has been observed in the wild. Organizations should verify their Linux systems are patched against this CWE-190 integer overflow vulnerability.
Remediation Timeline
All four vulnerabilities have a remediation due date of February 16, 2026. Federal agencies are required to apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of affected products if mitigations are unavailable.
None of the vulnerabilities have confirmed links to ransomware campaigns at this time.



