CISA, NSA Warn of Chinese BRICKSTORM Malware Targeting Government and IT Sectors

CISA, the NSA, and the Canadian Centre for Cyber Security have issued a joint malware analysis report warning that Chinese state-sponsored actors are using BRICKSTORM, a sophisticated backdoor designed for long-term persistence in VMware vSphere and Windows environments.
The advisory, first published in December 2025 and updated with additional samples, provides indicators of compromise (IOCs) and detection signatures based on analysis of 11 BRICKSTORM samples obtained from victim organizations.
Targets and Impact
Victim organizations are primarily in the Government Services and Facilities and Information Technology sectors. In one incident where CISA conducted an incident response engagement, PRC actors maintained persistent access from April 2024 through at least September 2025—over 17 months of undetected presence.
"These state-sponsored actors are not just infiltrating networks—they are embedding themselves to enable long-term access, disruption, and potential sabotage," said CISA Acting Director Madhu Gottumukkala.
CrowdStrike, which tracks the threat actor as Warp Panda, reported seeing "multiple intrusions targeting VMware vCenter environments at U.S.-based entities" throughout 2025, with one compromise dating back to 2023.
Technical Capabilities
BRICKSTORM is a custom Go or Rust-based backdoor with advanced evasion and persistence capabilities:
- Multi-layer encryption using HTTPS, WebSockets, and nested TLS
- DNS-over-HTTPS (DoH) to conceal C2 communications
- SOCKS proxy functionality for lateral movement and tunneling
- Self-monitoring that automatically reinstalls or restarts the malware if disrupted
- File system manipulation including browse, upload, download, create, and delete operations
The malware masquerades as legitimate VMware processes (e.g., vmware-sphere, vnetd, vami) and modifies system init files to ensure execution at boot.
Attack Chain
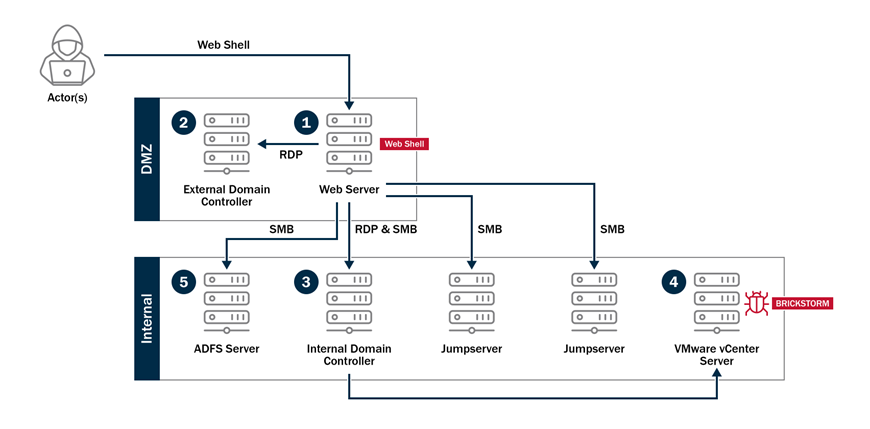
In the confirmed incident, attackers:
- Accessed a web server inside the organization's DMZ
- Moved laterally to an internal VMware vCenter server
- Implanted BRICKSTORM malware
- Compromised two domain controllers and an ADFS server
- Exported cryptographic keys from the ADFS server
- Used access to steal cloned VM snapshots for credential extraction
- Created hidden rogue VMs for ongoing operations
The actors obtained legitimate credentials by performing system backups and capturing Active Directory database information.
Attribution
BRICKSTORM has been linked to UNC5221, the same threat cluster behind the exploitation of Ivanti Connect Secure zero-days (CVE-2023-46805 and CVE-2024-21887) in early 2024. Google Mandiant and CrowdStrike have also observed the malware targeting legal services, SaaS providers, and technology sectors.
Recommendations
CISA urges organizations to:
- Scan systems for BRICKSTORM using the provided YARA and Sigma detection rules
- Inventory all network edge devices
- Monitor edge devices for suspicious network connectivity
- Ensure proper network segmentation between DMZ and internal systems
- Review service account usage and enforce least privilege
- Block unauthorized DoH providers to prevent covert C2 resolution
Organizations that detect BRICKSTORM or related activity should report incidents to CISA at contact@cisa.dhs.gov or (888) 282-0870.
IOCs and detection signatures are available in STIX format from CISA's advisory page.



