CISA Silently Updated Ransomware Intelligence on 59 Vulnerabilities in 2025 Without Notifying Defenders
CISA has been silently updating its Known Exploited Vulnerabilities (KEV) catalog when it confirms that vulnerabilities are being exploited by ransomware groups — without notifying defenders when those changes occur.
Glenn Thorpe, senior director of security research and detection engineering at GreyNoise, documented the gap by downloading daily KEV snapshots for all of 2025. He found that CISA flipped 59 vulnerabilities from "Unknown" to "Known" under the "Known To Be Used in Ransomware Campaigns?" field throughout the year — each time without an alert, advisory, or announcement.
"That's a material change in your risk posture," Thorpe wrote. "Your prioritization calculus should shift. But there's no alert, no announcement. Just a field change in a JSON file."
What the Data Shows
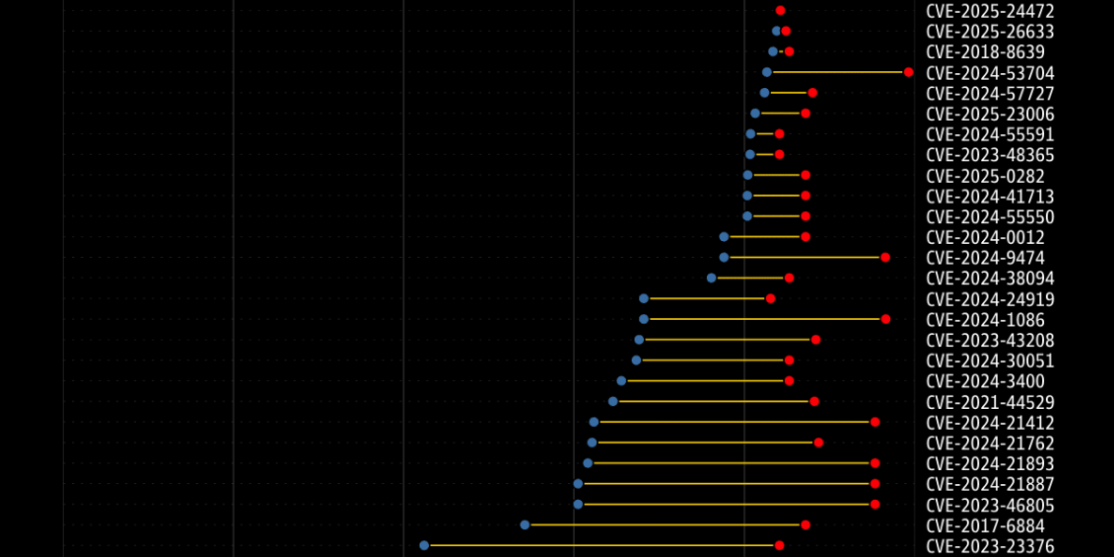
Thorpe's analysis of the 59 flipped CVEs reveals clear patterns in what ransomware operators are targeting.
By vendor: Microsoft led with 16 CVEs (27%), affecting SharePoint, Print Spooler, Group Policy, and Mark-of-the-Web bypasses. Ivanti followed with 6, Fortinet with 5 (FortiOS SSL-VPN heap overflows prominent), and Palo Alto Networks and Zimbra with 3 each.
By target: 34% involved edge and network devices. 19 of the 59 specifically target network security appliances — firewalls, VPN concentrators, and email servers that organizations deploy to protect themselves. Fortinet, Ivanti, Palo Alto, and Check Point products all appeared.
By timing: 41% of the flips occurred in a single month — May 2025. The fastest time from KEV addition to ransomware confirmation was just one day. The longest lag was 1,353 days.
By type: Authentication bypass was the most common vulnerability type at 14%, followed by remote code execution. 39% of the flipped CVEs were from before 2023, including legacy Adobe Reader vulnerabilities that suddenly became ransomware-relevant.
Why This Matters
The KEV catalog exists to help defenders prioritize patching. When CISA confirms that a vulnerability is being used in ransomware campaigns, that's actionable intelligence that should trigger immediate reprioritization. But without notification, defenders who aren't manually diffing the KEV JSON file daily are missing critical context.
As Thorpe put it: "Ransomware operators are economic actors. They invest in exploit development for platforms with high deployment and high-value access. Firewalls, VPN concentrators, and email servers fit that profile perfectly."
The pace is also accelerating. Ransomware operators are integrating fresh exploits into their playbooks faster than defenders are patching — and CISA's silent updates mean the defenders who most need this intelligence aren't getting it in time.
CISA's Response
CISA Executive Assistant Director for Cybersecurity Nick Andersen acknowledged the feedback, stating that the agency continues to "streamline processes and enrich vulnerability data" through the KEV catalog, the CVE Program, and Vulnrichment. He described community feedback as "essential" to enhancing the catalog.
Recommendation
Thorpe has created an RSS feed that tracks KEV ransomware field changes, updated hourly. Defenders relying on the KEV catalog for patch prioritization should subscribe to this feed rather than depending on CISA advisories that may never come.
Organizations should also review their current exposure against edge device and network appliance CVEs — particularly Fortinet, Ivanti, Palo Alto, and Microsoft products — given the heavy ransomware targeting of perimeter infrastructure documented in this analysis.



