Cisco Unified Communications Zero-Day Exploited in the Wild for Root Access (CVE-2026-20045)
Cisco has disclosed a critical zero-day vulnerability in its Unified Communications products that is being actively exploited in the wild, allowing unauthenticated attackers to execute arbitrary commands and gain root access on affected systems.
The vulnerability, tracked as CVE-2026-20045, affects the web-based management interface of multiple Cisco UC products. Cisco's Product Security Incident Response Team (PSIRT) has confirmed active exploitation attempts and is urging immediate patching.
Technical Details
The flaw stems from improper validation of user-supplied input in HTTP requests to the management interface. Attackers can send crafted HTTP requests that bypass authentication, execute commands at the user level, and then escalate privileges to root.
Cisco rated the vulnerability as Critical via its Security Impact Rating (SIR), overriding the CVSS score due to the root-level access implications. No workarounds are available—exploitation requires only network access to the management interface, which is commonly exposed in enterprise VoIP deployments via firewalls or VPNs.
Affected Products
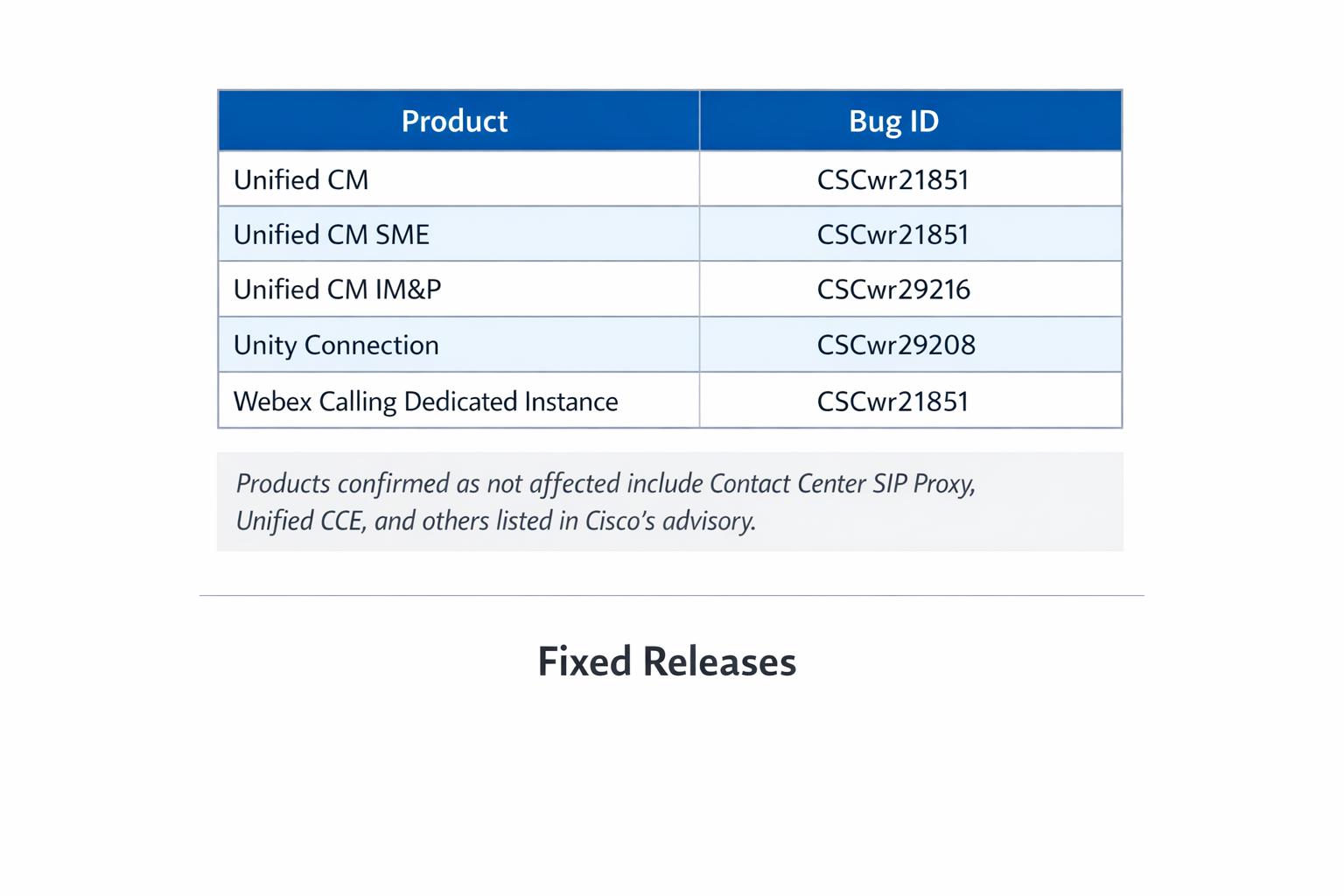
Products confirmed as not affected include Contact Center SIP Proxy, Unified CCE, and others listed in Cisco's advisory.
Fixed Releases
Unified CM, IM&P, SME, Webex Calling:
| Release | Fix |
|---|---|
| 12.5 | Migrate to fixed release |
| 14 | 14SU5 or 14SU4a patch |
| 15 | 15SU4 (March 2026) or 15SU2/3 patches |
Unity Connection:
| Release | Fix |
|---|---|
| 12.5 | Migrate to fixed release |
| 14 | 14SU5 or 14SU4 patch |
| 15 | 15SU4 (March 2026) or 15SU3 patch |
Exploitation Activity
Cisco PSIRT has detected real-world exploitation targeting unpatched systems. Attackers are likely leveraging automated scanners to identify exposed management interfaces. CISA is expected to add this vulnerability to its Known Exploited Vulnerabilities (KEV) catalog imminently.
Recommendations
- Apply patches immediately
- Restrict management interface access to trusted IPs via firewall rules
- Monitor logs for anomalous HTTP requests to the management interface
- Prioritize patching for systems exposed to the internet or accessible via VPN
The vulnerability was reported by an external researcher who Cisco credited in the advisory.



