Cloudflare WAF Zero-Day Allowed Attackers to Bypass Security Controls via ACME Challenge Path

A critical zero-day vulnerability in Cloudflare's Web Application Firewall (WAF) allowed attackers to bypass security controls and directly access protected origin servers.
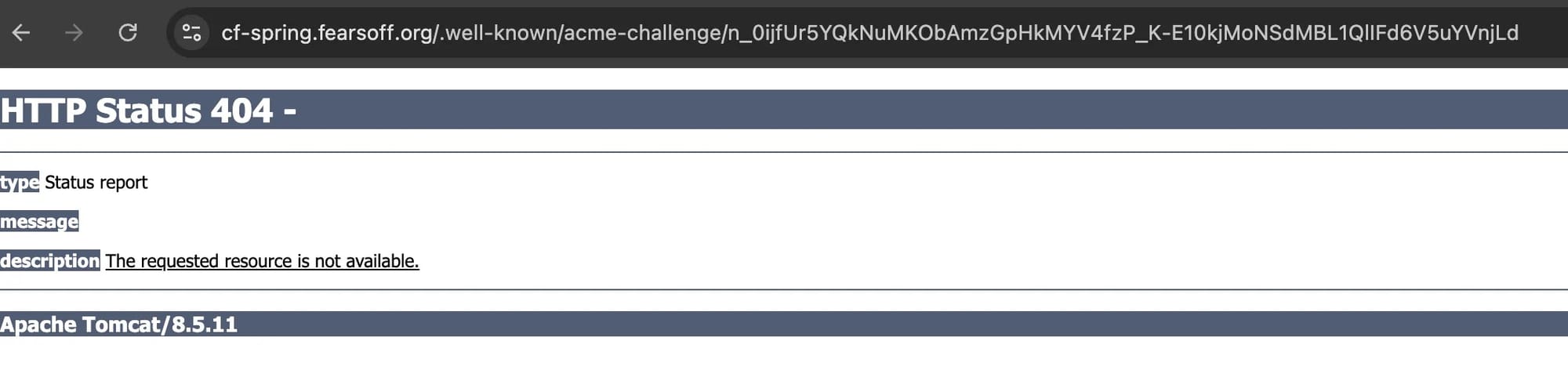
Security researchers at FearsOff discovered that requests targeting the /.well-known/acme-challenge/ directory could reach origin servers even when WAF rules explicitly blocked all other traffic.
How It Worked
The ACME (Automatic Certificate Management Environment) protocol automates SSL/TLS certificate validation. The HTTP-01 method requires websites to serve a token at /.well-known/acme-challenge/{token} for certificate authorities to verify domain ownership.
When Cloudflare processed ACME challenge requests for its managed certificates, the system disabled WAF features to prevent interference with validation. However, a critical flaw emerged: if the requested token didn't match a Cloudflare-managed certificate order, the request bypassed WAF evaluation entirely and proceeded directly to the customer's origin server.
This logic error transformed a narrow certificate validation exception into a broad security bypass affecting all hosts behind Cloudflare protection.
Attack Vectors Demonstrated
Researchers confirmed multiple exploitation paths:
| Framework | Attack | Impact |
|---|---|---|
| Spring/Tomcat | Servlet path traversal via ..;/ | Exposed actuator endpoints, database credentials, API tokens, cloud keys |
| Next.js | Direct origin access | Leaked operational data from server-side rendering |
| PHP | Local file inclusion | File system access via malicious path parameters |
Account-level WAF rules configured to block requests based on custom headers were completely ignored for ACME path traffic.
Disclosure Timeline
| Date | Event |
|---|---|
| October 9, 2025 | FearsOff reports via HackerOne |
| October 13, 2025 | Cloudflare begins validation |
| October 14, 2025 | HackerOne triages issue |
| October 27, 2025 | Permanent fix deployed |
Remediation
Cloudflare modified the code to disable security features only when requests match valid ACME HTTP-01 challenge tokens for the specific hostname.
No customer action is required. Cloudflare confirmed no evidence of malicious exploitation was found.
Post-fix testing confirmed WAF rules now apply uniformly across all paths, including the previously vulnerable ACME challenge route.



