Critical Apache bRPC Vulnerability Allows Remote Command Injection (CVE-2025-60021)
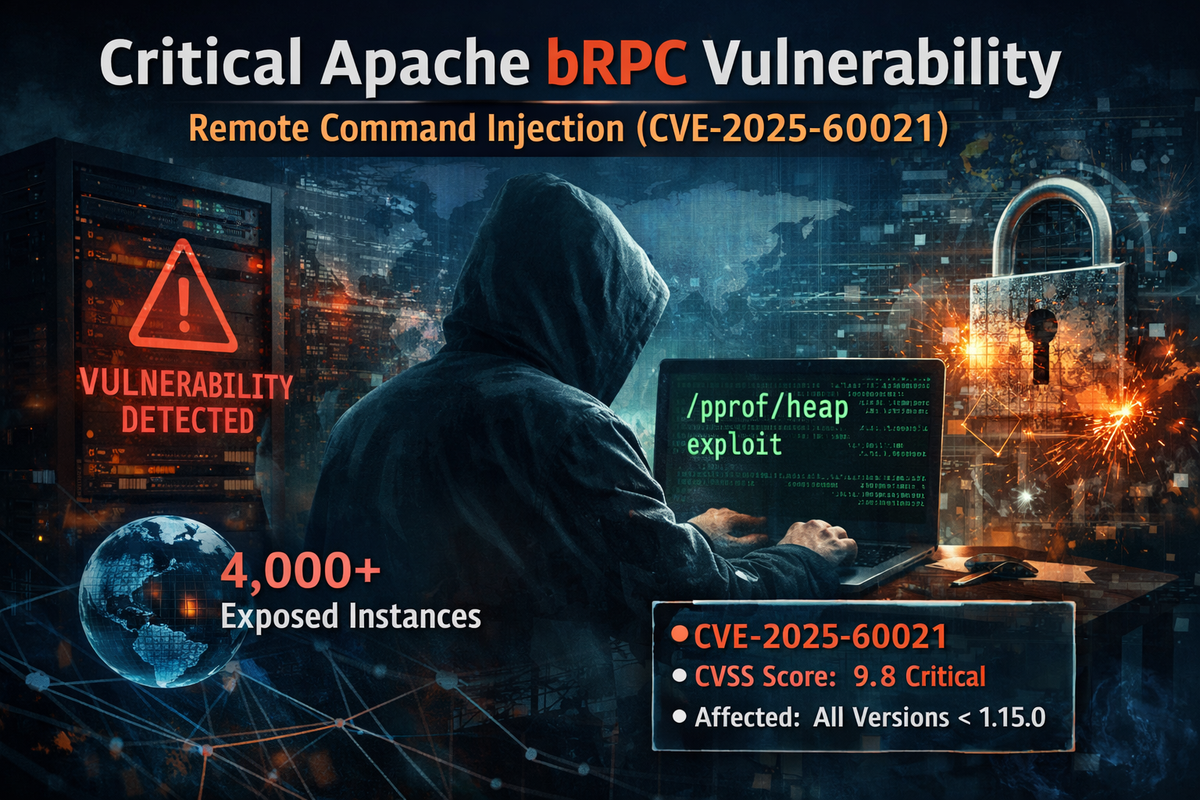
A critical remote command injection vulnerability has been discovered in Apache bRPC, with over 4,000 exposed instances identified online.
Vulnerability Details
| CVE ID | CVSS Score | Type | Affected Versions |
|---|---|---|---|
| CVE-2025-60021 | 9.8 (Critical) | Remote Command Injection | All versions prior to 1.15.0 |
The flaw exists in the heap profiler's extra_options parameter. Attackers can exploit the /pprof/heap service to execute arbitrary commands on vulnerable systems without authentication.
Exposure
ZoomEye scans indicate approximately 4,000+ internet-facing bRPC instances, creating significant attack surface for exploitation.
Remediation
Organizations running Apache bRPC should upgrade to version 1.15.0 or later immediately.
As a temporary mitigation, restrict access to the /pprof/heap endpoint and ensure bRPC services are not exposed to the internet.



