Critical Appsmith Vulnerability Enables Account Takeover Through Origin Header Manipulation (CVE-2026-22794)

A critical authentication vulnerability in Appsmith allows attackers to take over user accounts by manipulating the HTTP Origin header during the password reset process, with over 1,600 vulnerable instances currently exposed on the internet, according to research published by Resecurity.
The vulnerability, tracked as CVE-2026-22794, carries a CVSS score of 9.6 and affects Appsmith versions 1.92 and below. The flaw occurs because Appsmith uses a client-controlled header to construct password reset links, exposing sensitive authentication tokens to attackers.
Simple Attack Chain Leads to Full Compromise
The exploitation is straightforward. An attacker requests a password reset for a victim's email address while providing a malicious Origin header pointing to an attacker-controlled domain. The victim receives a legitimate-looking email from Appsmith, but the embedded reset link points to the attacker's server.
When the victim clicks the link, the password reset token is sent directly to the attacker's infrastructure. The attacker can then use the stolen token to reset the victim's password and gain full control of the account, including administrative accounts with elevated privileges.
The vulnerability exists because Appsmith blindly trusts the Origin HTTP request header and uses it to construct security-sensitive URLs. The server directly assigns the Origin value as the base URL for password reset email links without validation, allowlisting, or hostname verification.
Over 1,600 Instances Exposed Online
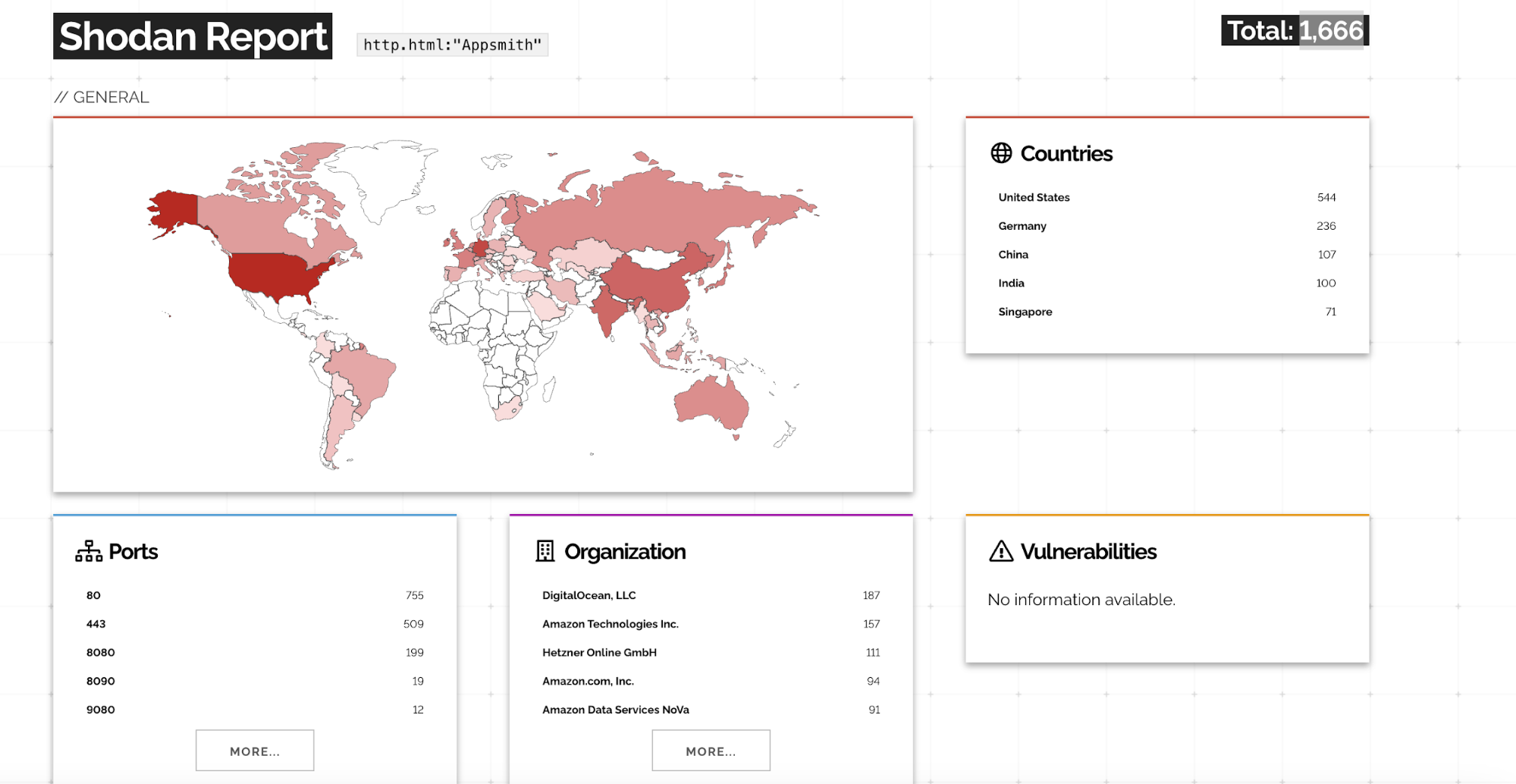
Shodan intelligence reveals 1,666 publicly accessible Appsmith instances exposed on the internet. Analysis indicates a significant number of these instances are running Appsmith 1.x versions affected by CVE-2026-22794.
Resecurity documented vulnerable instances across multiple versions, with version 1.18.0 showing 73 exposed instances, version 1.24.0 showing 59 instances, and numerous other vulnerable versions ranging from 1.10.2 to 1.29.4 publicly accessible. All Appsmith 2.x versions are patched and not vulnerable.
High-Value Target for Attackers
Appsmith is an open-source low-code platform used by organizations to build internal tools, administrative dashboards, customer portals, IT automation systems, and custom AI applications. The platform integrates with SQL and NoSQL databases, REST and GraphQL APIs, and various cloud services.
Because Appsmith commonly manages sensitive internal data, hosts privileged user accounts, and runs inside trusted networks, the authentication vulnerability is particularly dangerous. Successful exploitation can provide attackers unauthorized access to connected databases including PostgreSQL, MySQL, and MongoDB, internal APIs and business systems, user records and credentials, and AI-enabled workflows that interact with LLMs and proprietary data.
If the compromised account has administrative privileges, attackers can manage users and roles, modify or delete applications, access all connected data sources, and alter authentication settings, turning a single account compromise into a platform-wide breach.
Technical Root Cause
The vulnerable code in the /forgotPassword endpoint directly assigns the client-provided Origin header to the base URL used for generating email links. The endpoint always returns HTTP 200 OK regardless of outcome, allowing attackers to silently trigger password reset emails without detection.
Resecurity emphasized that this breaks a fundamental security rule: never trust client-controlled headers for security-critical logic. The Origin header is not authenticated, not validated, and not restricted, yet Appsmith used it as a trusted base URL for generating authentication-related email links.
Patch Available
The vulnerability is fixed in Appsmith version 1.93. The Appsmith team implemented proper validation of the Origin header, enforcement of a trusted base URL through the APPSMITH_BASE_URL configuration, and rejection of untrusted origins during email link generation.
Recommendations
Organizations running Appsmith should upgrade immediately to version 1.93 or later. Administrators should configure APPSMITH_BASE_URL to the official Appsmith domain to prevent dynamic or user-controlled URL generation.
If immediate upgrade is not possible, organizations can implement defense-in-depth measures including stripping or overriding the Origin header using a reverse proxy or web application firewall, monitoring password reset requests for anomalies, and enabling multi-factor authentication where available.
A Nuclei detection template is available for identifying vulnerable instances at the rxerium-templates GitHub repository.



