Critical AWS CodeBuild Flaw Exposed AWS Console to Supply Chain Attack

Critical AWS CodeBuild Flaw Exposed AWS Console to Supply Chain Attack
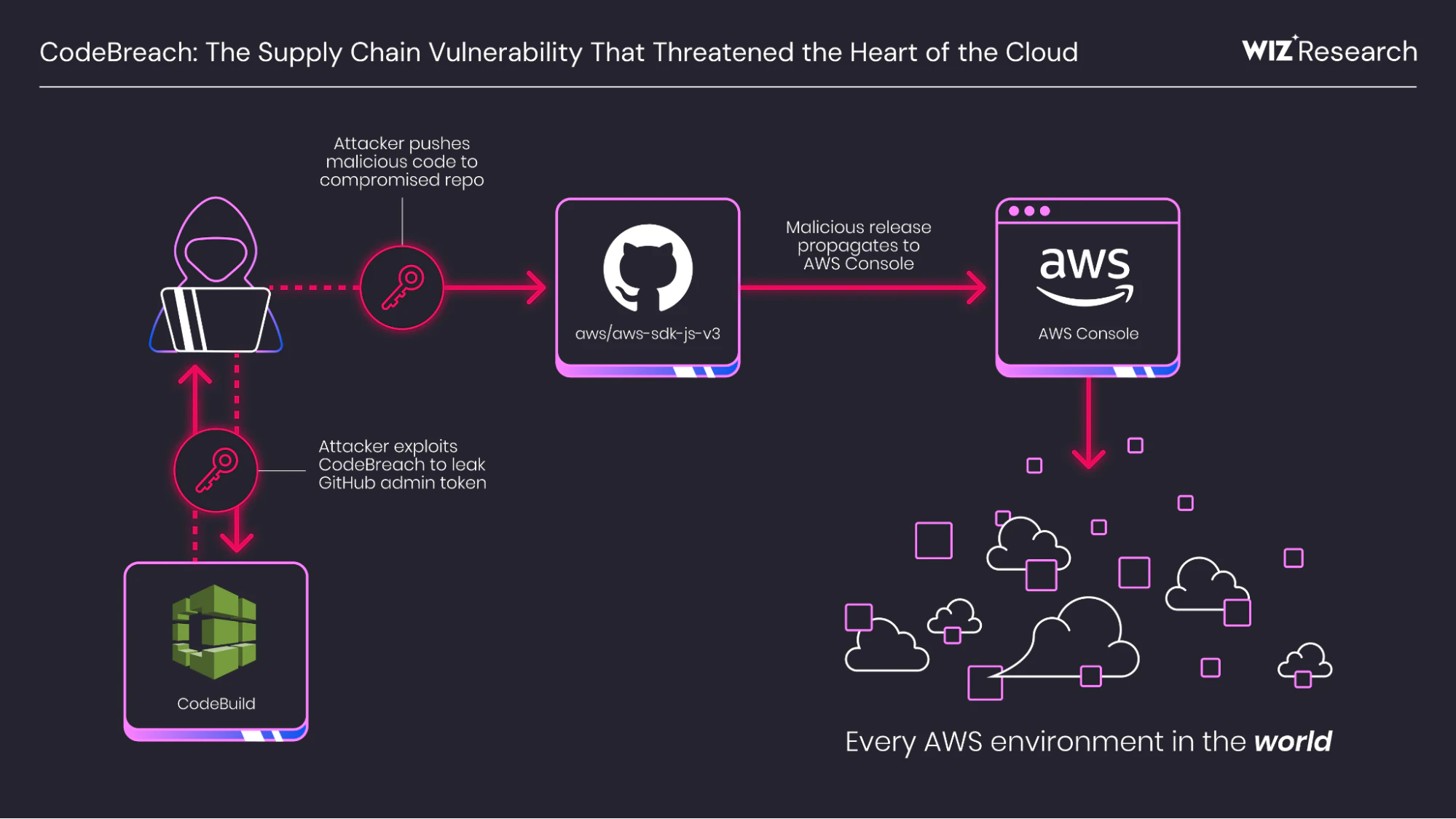
A critical misconfiguration in AWS CodeBuild could have allowed attackers to compromise key AWS-owned GitHub repositories, including the JavaScript SDK that powers the AWS Console itself.
Security researchers at Wiz Research discovered the vulnerability, dubbed "CodeBreach," which threatened platform-wide compromise across countless AWS environments.
How the Attack Worked
The flaw stemmed from unanchored regular expression patterns in CodeBuild webhook filters. The ACTOR_ID parameter, designed to restrict builds to trusted GitHub user IDs, lacked proper ^ and $ anchors.
Without these anchors, the filter matched any user ID containing an approved substring. Attackers could bypass this via "eclipse" events - where newly created GitHub IDs naturally incorporate older maintainer IDs as substrings.
GitHub assigns approximately 200,000 new user IDs daily, making such overlaps frequent for the 6-7 digit IDs used by AWS repository maintainers.
Repositories at Risk
Four AWS repositories were vulnerable:
- aws/aws-sdk-js-v3
- aws/aws-lc
- corretto/amazon-corretto-crypto-provider
- awslabs/open-data-registry
Proof of Concept
Wiz demonstrated the attack against aws/aws-sdk-js-v3 by submitting a pull request containing hidden payload code. The code extracted a GitHub Personal Access Token (PAT) from the aws-sdk-js-automation account.
The stolen PAT granted repo and admin:repo_hook scopes, enabling:
- Collaborator invites for admin escalation
- Direct pushes to the main branch
Compromising the JavaScript SDK could have infected its weekly NPM releases, affecting 66% of scanned cloud environments. The AWS Console itself bundles recent SDK versions with user credentials, amplifying the potential impact.
AWS Response
AWS fixed the regex flaw within 48 hours of disclosure. Additional remediation included:
- Revoking affected tokens
- Hardening memory protections
- Auditing all public builds
- Confirming no exploitation occurred via logs
No customer data was impacted. AWS has since introduced Pull Request Comment Approval and CodeBuild-hosted runners to block untrusted builds.
Recommendations
Organizations using AWS CodeBuild should:
- Anchor all webhook regex patterns with
^and$ - Use fine-grained PATs with minimal scopes
- Enable PR approval gates for builds
- Disable automatic PR builds from untrusted sources
Wiz disclosed the vulnerability on August 25, 2025. Public disclosure followed on January 15, 2026.



