Critical Deno Vulnerabilities Enable Server Secrets Exposure and Windows Command Injection
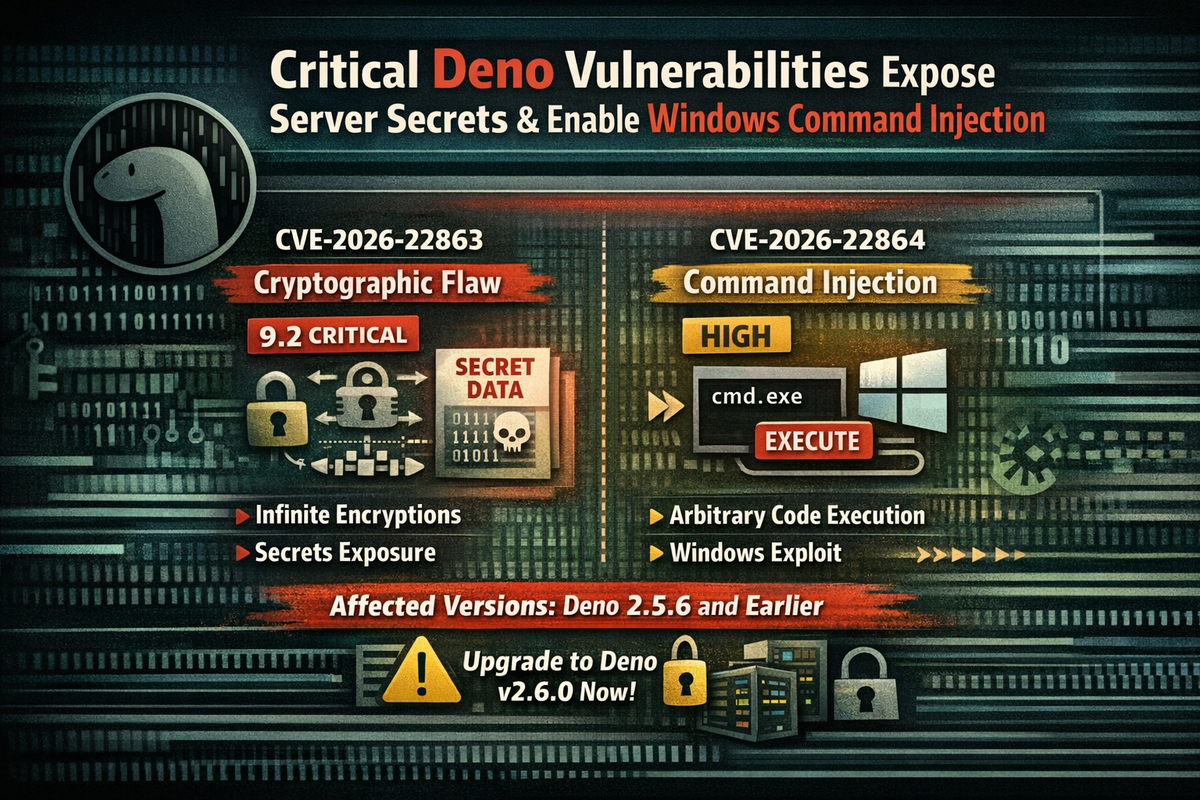
Two significant security vulnerabilities have been discovered in Deno, the modern JavaScript and TypeScript runtime known for its "secure by default" architecture.
The flaws could expose sensitive server secrets and allow command injection on Windows systems.
Vulnerabilities
| CVE ID | CVSS Score | Type | Impact |
|---|---|---|---|
| CVE-2026-22863 | 9.2 (Critical) | Missing Cryptographic Step | Secrets exposure |
| CVE-2026-22864 | High | Command Injection | Arbitrary code execution on Windows |
CVE-2026-22863 - Cryptographic Flaw
The more severe vulnerability resides in Deno's node:crypto compatibility layer - a module that allows Deno to run code originally written for Node.js.
The flaw involves the cipher not being properly finalized, which allows attackers to perform infinite encryptions. This can lead to brute force attacks or more refined attacks aimed at learning server secrets.
Affected versions: Deno 2.5.6 and earlier
CVE-2026-22864 - Windows Command Injection
The second vulnerability is an incomplete fix for command injection prevention on Windows. The flaw allows case-insensitive extension bypass, potentially enabling arbitrary command execution on vulnerable Windows systems.
Remediation
All users should upgrade to Deno v2.6.0 or newer immediately.
Why This Matters
Deno markets itself as "secure by default" - a runtime designed to address Node.js security shortcomings. These vulnerabilities undermine that promise, particularly for:
- Applications using the Node.js compatibility layer
- Production deployments on Windows
- Services handling sensitive cryptographic operations
Organizations running Deno in production should prioritize this update.



