CRITICAL: Patch n8n Now — Unauthenticated RCE Affects 100K Servers
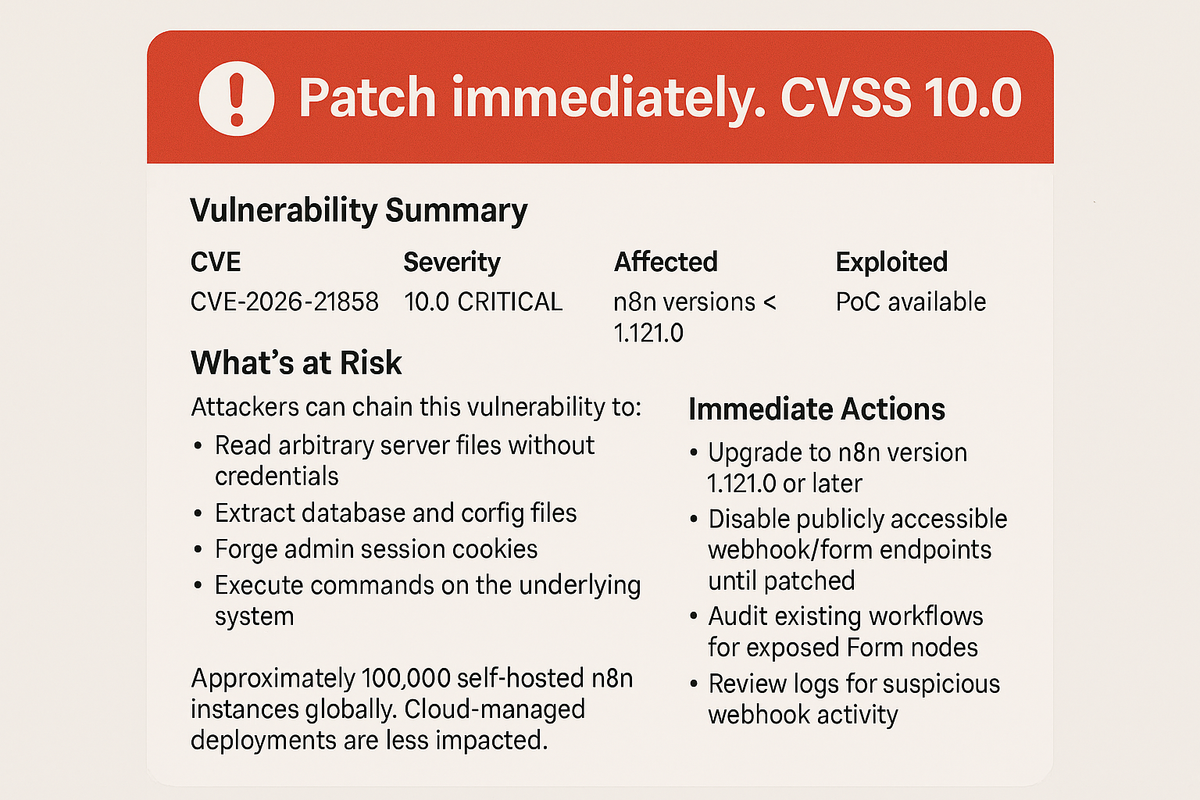
Patch immediately. CVSS 10.0.
A maximum-severity flaw in n8n allows unauthenticated attackers to fully compromise servers and access all connected systems including API keys, databases, and cloud services.
Vulnerability Summary
| CVE | CVE-2026-21858 |
| Severity | 10.0 CRITICAL |
| Affected | n8n versions < 1.121.0 |
| Exploited | PoC available |
| Patch | Upgrade to 1.121.0+ |
What's at Risk
Attackers can chain this vulnerability to:
- Read arbitrary server files without credentials
- Extract database and config files
- Forge admin session cookies
- Execute commands on the underlying system
With n8n's access to connected services (Google Drive, Salesforce, CI/CD pipelines, payment processors), a single compromise can cascade across your entire infrastructure.
Immediate Actions
- Upgrade to n8n version 1.121.0 or later
- Disable publicly accessible webhook/form endpoints until patched
- Audit existing workflows for exposed Form nodes
- Review logs for suspicious webhook activity
Who's Affected
Approximately 100,000 self-hosted n8n instances globally. Cloud-managed deployments are less impacted.
Tags: Critical, CVE-2026-21858, n8n, RCE, Patch Now



