Critical SandboxJS Vulnerability Allows Complete Sandbox Escape and Remote Code Execution (CVE-2026-23830)
A critical vulnerability in SandboxJS, a widely used library for safely executing untrusted JavaScript code, allows attackers to completely escape the sandbox environment and achieve remote code execution on the host system.
Tracked as CVE-2026-23830 and carrying a maximum CVSS score of 10.0, the flaw stems from an incomplete implementation of the library's core security mechanism.
Async Functions Left Unprotected
SandboxJS attempts to isolate code execution by replacing the global Function constructor with a sandboxed version. However, security researchers discovered that the library failed to apply the same restrictions to AsyncFunction, GeneratorFunction, and AsyncGeneratorFunction constructors.
While these constructors are not exposed as global properties, they remain accessible through the .constructor property of their respective instances. An attacker can simply create an async function within the sandbox and access its constructor to obtain the native, unsandboxed AsyncFunction object.
Because JavaScript function constructors create functions that execute in the global scope, obtaining the host AsyncFunction constructor allows an attacker to create new functions that run entirely outside the sandbox context with full access to the underlying system.
Exploitation Is Trivial
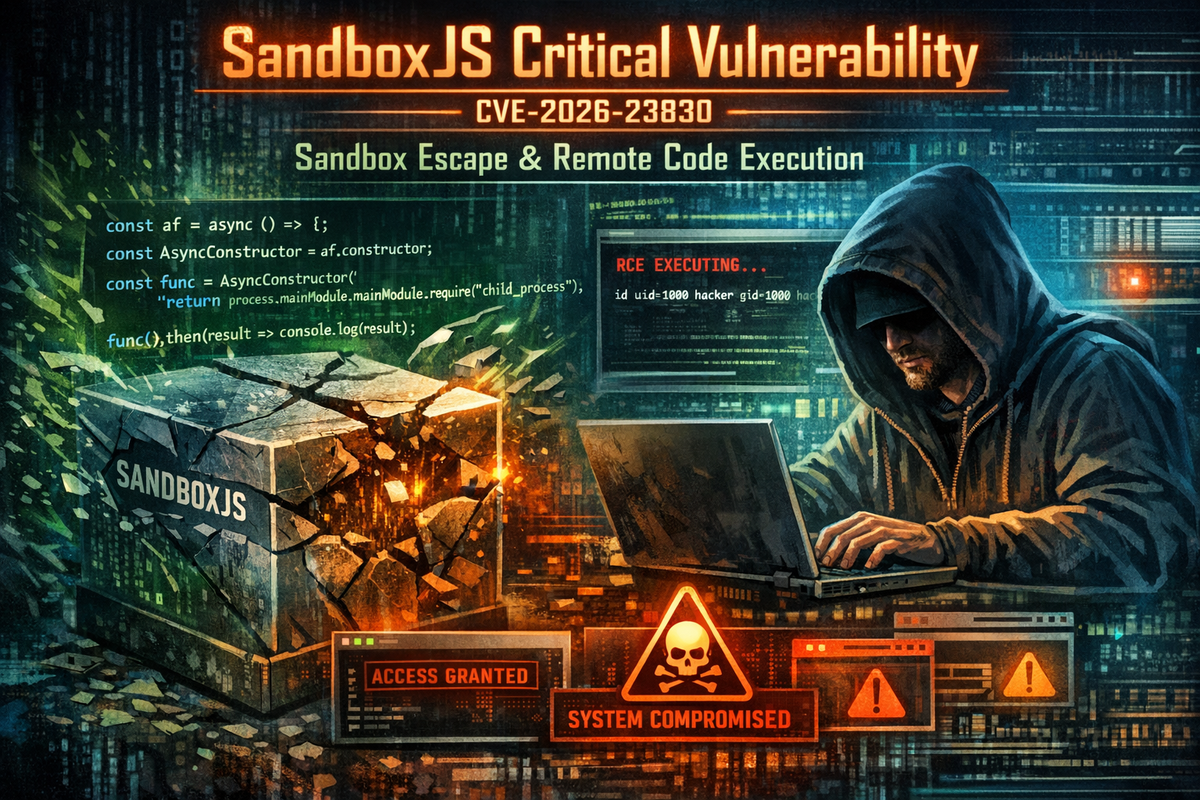
The attack requires minimal complexity. An attacker can access the unrestricted constructor, create a malicious function, and execute system commands in just a few lines of code:
javascript
const af = async () => {};
const AsyncConstructor = af.constructor;
const func = AsyncConstructor("return process.mainModule.require('child_process').execSync('id').toString()");
func().then(result => console.log(result));In Node.js environments, this enables direct command execution on the server. Browser-based implementations face equivalent risks, with attackers able to access the window object and perform actions in the context of the host page.
Immediate Action Required
Organizations using SandboxJS to execute untrusted code should treat any sandboxed environment as potentially compromised until patches are applied. The vulnerability affects any application relying on the library's isolation guarantees for security-critical functionality.
Developers should update to patched versions immediately and audit systems for potential exploitation. Applications that accepted user-supplied JavaScript code through SandboxJS-protected environments should be considered at risk.



