Critical vm2 Sandbox Escape Vulnerability Allows Arbitrary Code Execution on Host Systems (CVE-2026-22709)
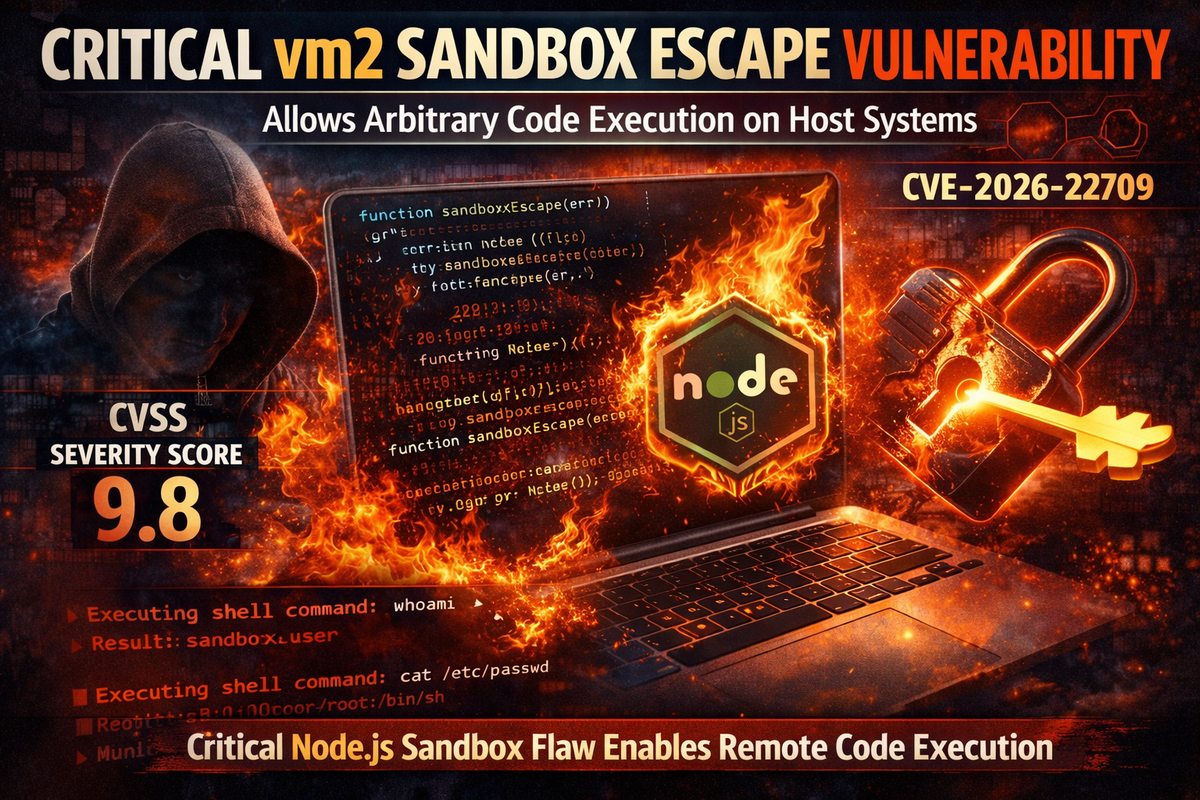
A critical vulnerability in vm2, a widely-used Node.js sandbox library, allows attackers to completely bypass sandbox isolation and execute arbitrary code on host machines. The flaw carries a CVSS severity score of 9.8, the highest possible rating for a remotely exploitable vulnerability.
The vulnerability, tracked as CVE-2026-22709, affects vm2 versions 3.10.0 and below. Organizations running applications that rely on vm2 for executing untrusted code should upgrade to version 3.10.2 immediately.
Promise Callback Sanitization Bypass
The vulnerability stems from incomplete sanitization of Promise callback functions within the vm2 sandbox environment. While the library sanitizes callbacks for localPromise.prototype.then, it fails to apply the same protections to globalPromise.prototype.then.
This discrepancy creates an exploitable gap because async functions return globalPromise objects rather than local Promise instances. Attackers can leverage this oversight to escape the sandbox by catching errors from async functions and using the error constructor to access the host system's Function constructor.
Once an attacker obtains access to the Function constructor outside the sandbox context, they can execute arbitrary code on the host system with the same privileges as the Node.js process. Proof-of-concept code demonstrates the ability to spawn child processes and execute system commands directly on the host machine.
Millions of Applications Potentially Affected
The vm2 library is extensively used across the Node.js ecosystem to safely execute untrusted or user-supplied code in isolated environments. Common use cases include online code editors, automated testing platforms, plugin systems, serverless function runners, and any application that needs to evaluate dynamic code without exposing the host system.
With millions of downloads, the library's widespread adoption means a significant number of applications may be vulnerable. Any system using vm2 to isolate untrusted code execution is at risk of complete compromise through this sandbox escape.
Immediate Remediation Required
The vulnerability has been patched in vm2 version 3.10.2. Organizations should audit their Node.js applications and dependencies for vm2 usage and upgrade to the patched version immediately.
Applications that cannot be immediately updated should consider disabling functionality that relies on vm2 sandboxing until patches can be applied, as the vulnerability provides a direct path to arbitrary code execution with no additional exploitation steps required.
Given the critical severity rating and the straightforward exploitation path, this vulnerability should be treated as a priority remediation item for any organization running affected vm2 versions.



