Critical WordPress LMS Plugin Flaw Under Active Exploitation Enables Full Site Takeover
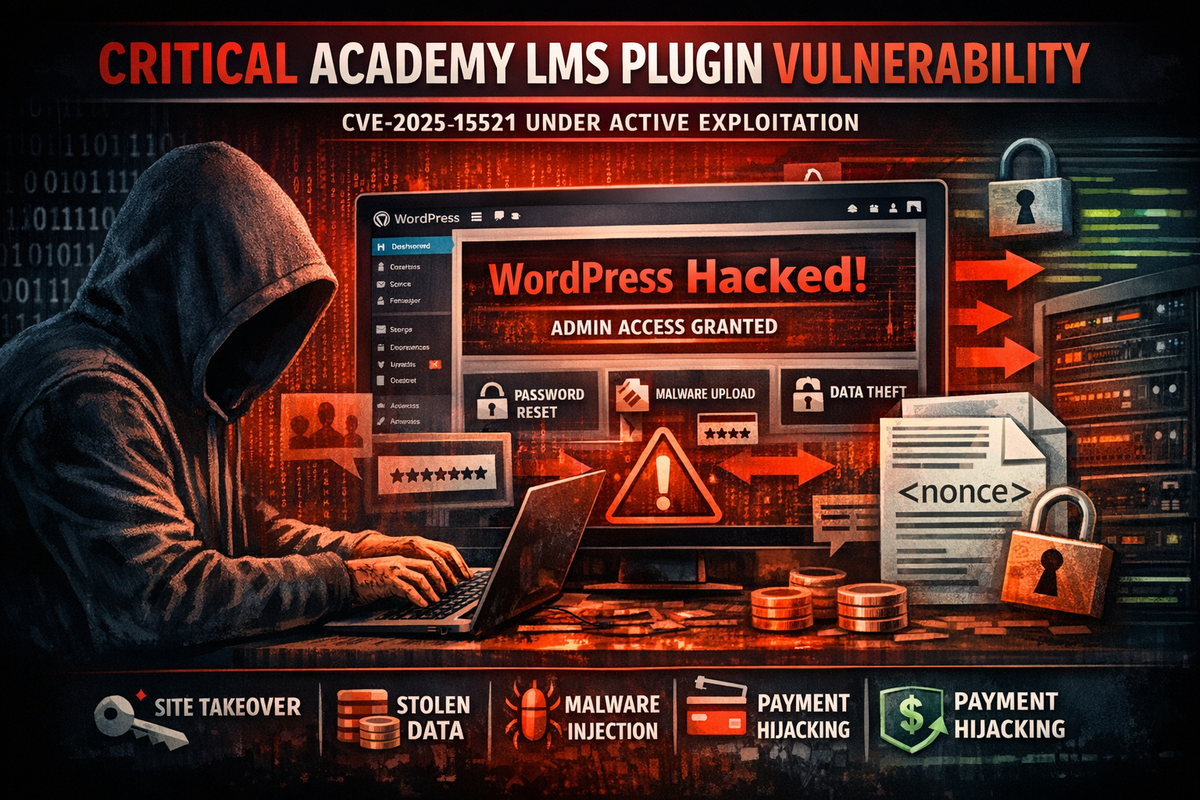
A critical vulnerability in the Academy LMS plugin for WordPress is under active exploitation, allowing unauthenticated attackers to take over administrator accounts and gain full control of affected eLearning platforms.
The flaw, tracked as CVE-2025-15521, carries a CVSS score of 9.8 and affects all versions of the plugin up to 3.5.0. Academy LMS is widely used by educators and organizations to build and monetize online training platforms, with features including course creation, student enrollment, quizzes, and payment integration.
Exploiting Exposed Nonces
The vulnerability stems from a broken authentication mechanism in how the plugin handles password updates. Rather than properly verifying user identity through cryptographic signatures or secret keys, the plugin relies on a publicly exposed nonce that attackers can harvest from the site.
With the captured nonce, attackers can reset passwords for any account—including administrators—without authentication. This grants them full control over the WordPress installation.
Post-Exploitation Impact
Once attackers gain administrative access, the potential damage is significant:
- Steal sensitive student and payment data
- Inject malware or backdoors for persistent access
- Modify course content or redirect payments
- Use the compromised site to distribute further attacks
Active Exploitation Confirmed
Wordfence has confirmed active exploitation attempts in the wild, with attackers actively scanning for and targeting vulnerable installations. The simplicity of the attack—requiring only a harvested nonce and no authentication—makes it attractive for both opportunistic and targeted campaigns.
Remediation
Site administrators running Academy LMS should immediately update to version 3.5.1 or later. Given the active exploitation, organizations should also audit for signs of compromise, including unexpected administrator accounts, modified files, or unfamiliar plugins.



