Django Patches Three High-Severity SQL Injection Flaws Across All Supported Versions
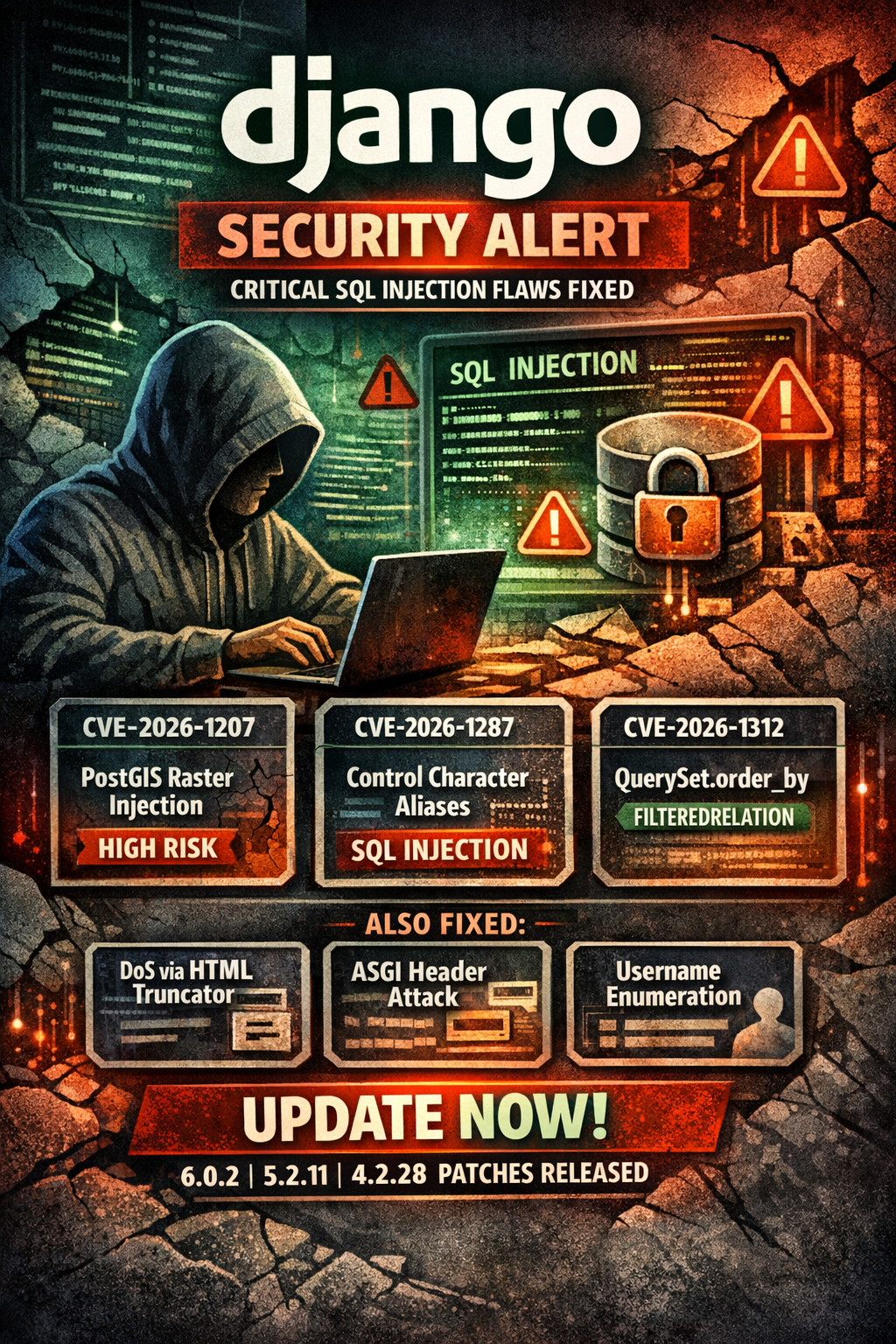
The Django project has issued security releases across all supported versions — Django 6.0.2, 5.2.11, and 4.2.28 — addressing six vulnerabilities, three of which are high-severity SQL injection flaws that could allow attackers to execute arbitrary SQL commands against backend databases.
All three SQL injection CVEs were reported by security researcher Solomon Kebede and Tarek Nakkouch. Django's main development branch is also affected and has been patched.
The SQL Injection Trio
CVE-2026-1207 — SQL Injection via PostGIS Raster Lookups (High) Raster lookups on GIS fields using PostGIS were vulnerable to SQL injection if untrusted data was passed as a band index. This affects any Django application using PostGIS with geographic data that accepts user-controlled band index values.
CVE-2026-1287 — SQL Injection via Control Characters in Column Aliases (High) FilteredRelation accepted control characters in column aliases, enabling SQL injection through crafted dictionary expansion passed as kwargs to QuerySet methods including annotate(), aggregate(), extra(), values(), values_list(), and alias().
CVE-2026-1312 — SQL Injection via QuerySet.order_by and FilteredRelation (High) QuerySet.order_by() was vulnerable to SQL injection through column aliases containing periods when the same alias was used in FilteredRelation via crafted dictionary expansion.
The CVE-2026-1287 and CVE-2026-1312 flaws share an attack pattern — both exploit FilteredRelation through dictionary expansion, suggesting that any application passing user-influenced dictionaries to QuerySet methods should be treated as potentially exposed.
Additional Fixes
CVE-2026-1285 — DoS via Truncator HTML Methods (Moderate) The Truncator.chars() and Truncator.words() methods with html=True, along with the truncatechars_html and truncatewords_html template filters, were vulnerable to denial of service via inputs containing large numbers of unmatched HTML end tags, causing quadratic time complexity.
CVE-2025-14550 — DoS via Repeated Headers on ASGI (Moderate) ASGIRequest handled duplicate headers through repeated string concatenation, allowing an attacker to cause service degradation or outage with specifically crafted requests containing multiple duplicate headers.
CVE-2025-13473 — Username Enumeration via mod_wsgi Timing Attack (Low) The check_password() function in Django's mod_wsgi authentication handler leaked timing information that could allow remote attackers to enumerate valid usernames.
Affected Versions
All currently supported Django branches are affected: 6.0, 5.2, and 4.2, plus the main development branch. Patches have been applied to all four branches.
Remediation
Update immediately to Django 6.0.2, 5.2.11, or 4.2.28 depending on your deployment. As a general practice, all user input passed to QuerySet methods, GIS lookups, or FilteredRelation should be validated and sanitized — but patching is the priority.



