Dozens of Major Data Breaches Linked to Single Threat Actor

Hudson Rock reports that several high-profile data breaches have been tied to a threat actor who gains entry into enterprise networks using stolen credentials.
The actor, known as “Zestix” and also associated with the online persona “Sentap,” operates as an initial access broker (IAB). In addition to facilitating access, the actor has been observed stealing sensitive data from victim organizations and selling it on underground forums.
Hudson Rock says Zestix emerged as a distinct identity in late 2024 or early 2025, though its activity can be traced back to operations conducted under the Sentap alias since 2021.
Both personas have been linked to information-stealer malware infections that led to compromises across global enterprises in sectors including aerospace, government infrastructure, legal services, and robotics.
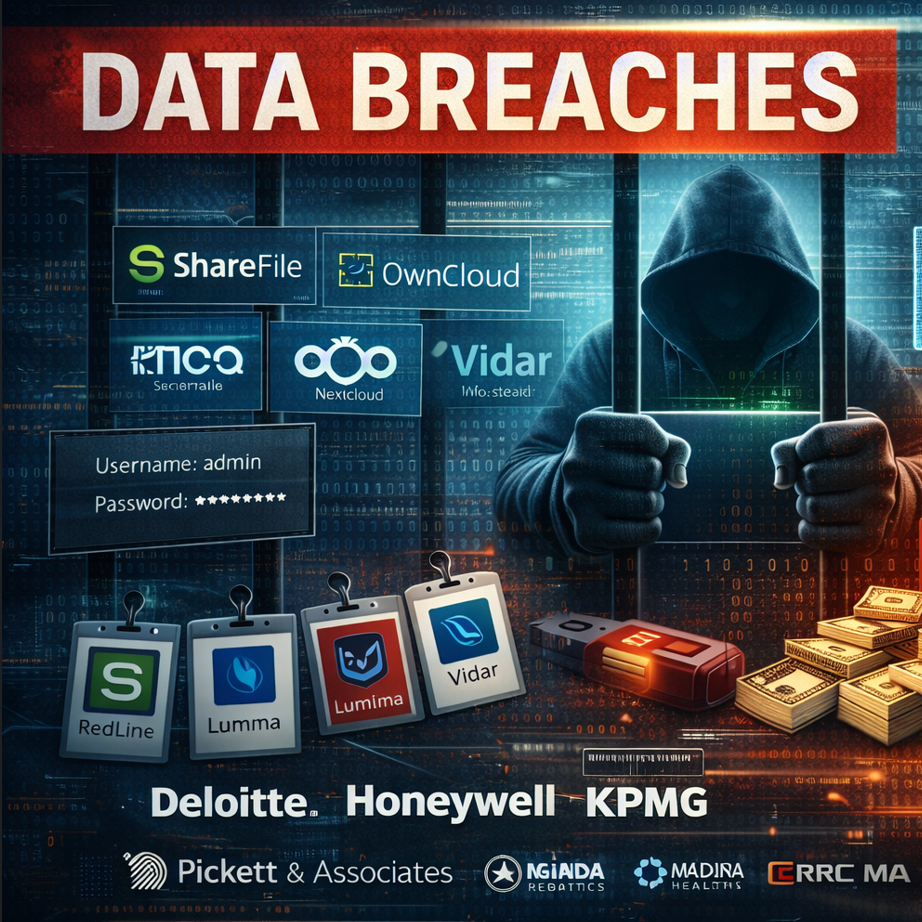
According to the report, the stolen credentials were collected from employees’ personal or work devices using infostealers such as RedLine, Lumma, and Vidar.
“While some credentials were harvested from recently infected systems, others had remained in logs for years before being exploited by an actor like Zestix,” Hudson Rock noted.
The absence of multi-factor authentication (MFA) on accounts with access to file-sharing platforms such as ShareFile, OwnCloud, and Nextcloud enabled Zestix/Sentap to successfully leverage the stolen credentials in approximately 50 incidents.
The stolen data was subsequently offered for sale on private Russian-language forums, while in some cases the actor also sold direct access to compromised systems.
Zestix/Sentap victims
Hudson Rock says Zestix has built a reputation for reliability, which may explain the $150,000 price tag reportedly placed on 77 GB of data allegedly stolen from Iberia, Spain’s national airline.
Other confirmed victims include Pickett & Associates, an engineering firm serving the energy sector; Intecro Robotics, an aerospace and defense manufacturer; Maida Health, which supports Brazil’s military police; CRRC MA, a rolling stock manufacturer subsidiary; K3G, a Brazilian internet service provider; NMCV Business LLC, which manages data for U.S. healthcare facilities; and more than a dozen additional organizations.
Operating under the Sentap identity, the threat actor claimed an even broader list of victims. However, Hudson Rock says it could not definitively link those incidents to file-sharing platforms or infostealer infections.
“It is possible these breaches still originated from infostealer-harvested credentials, given the number of victims we identified with such exposure, but alternative initial access methods cannot be ruled out,” Hudson Rock said.
The actor has claimed responsibility for large-scale data thefts at organizations including Pan-Pacific Mechanical (1.04 TB), Bradley R. Tyer & Associates (1.02 TB), The Providence Group (1 TB), Australia’s NBN (306 GB), UrbanX.io (275 GB), and many others.
The infostealer threat
Hudson Rock warns that credentials linked to thousands of organizations using ShareFile, OwnCloud, and Nextcloud are currently circulating in infostealer logs. Exposed entities reportedly include major brands such as Deloitte, Honeywell, KPMG, Samsung, and Walmart.
“These organizations have employees or partners who were infected, exposing valid credentials or active sessions to sensitive file repositories,” the firm said.
The problem is longstanding and difficult to eliminate. Information stealers have become a foundational component of modern cybercrime, enabling data breaches, identity theft, and fraud.
“Stealers represent the commoditization of cybercrime through malware-as-a-service,” said Trevor Hilligoss, SVP of security research at SpyCloud Labs, in comments to SecurityWeek.
“Attackers no longer need advanced technical skills. They can simply purchase or rent highly effective tools from MaaS marketplaces and deploy them at scale,” Hilligoss added.
Infostealers succeed by operating quickly and discreetly, often exfiltrating sensitive data within minutes and removing themselves shortly after, leaving few indicators of compromise.
For more than a decade, stolen credentials have powered large-scale attack campaigns, including credential stuffing, which remains a persistent cybersecurity challenge.



