Dutch Police Arrest Alleged AVCheck Mastermind Behind Major Counter-Antivirus Platform
Dutch authorities have arrested a 33-year-old man believed to be behind AVCheck, one of the world's largest counter-antivirus services used by cybercriminals to test malware against security products.
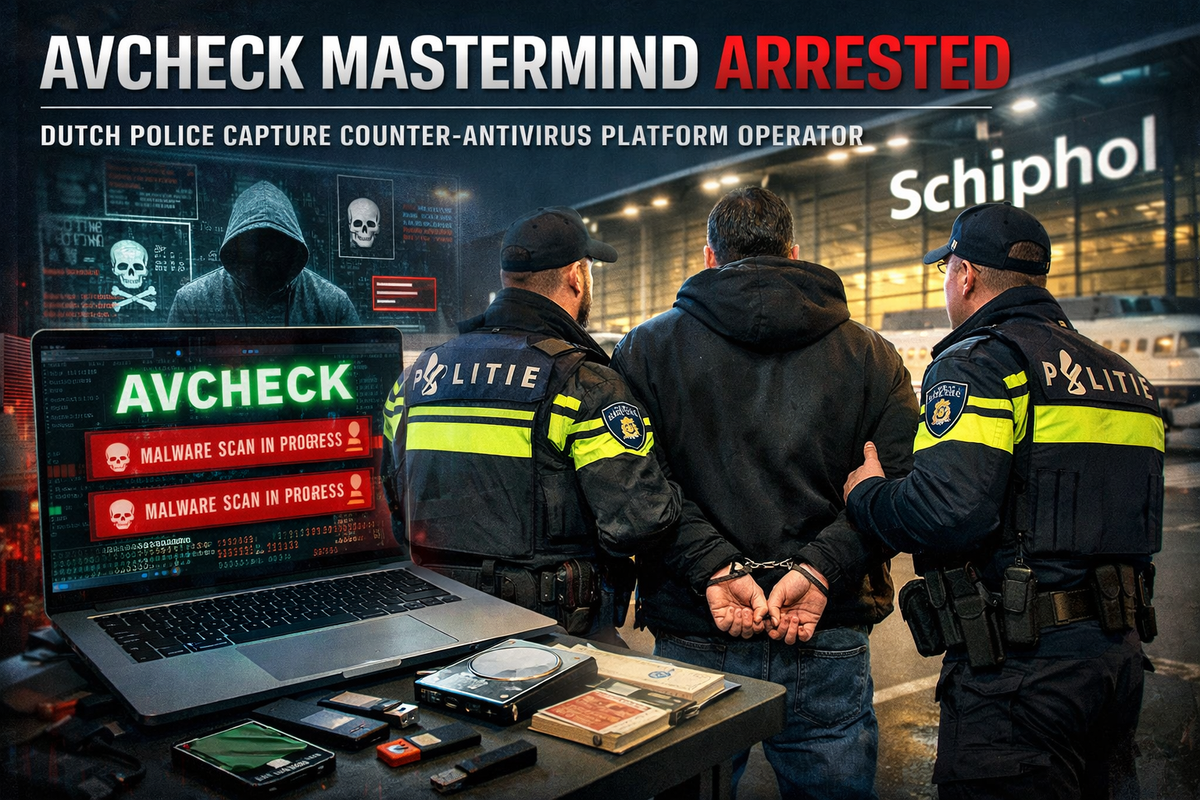
The suspect was detained at Amsterdam's Schiphol Airport on Sunday evening after being under international surveillance. Data storage devices were seized during the arrest.
What Was AVCheck?
AVCheck was an online platform that allowed cybercriminals to test their malware against different antivirus products to identify which detection systems it could evade.
The service gave threat actors a tool to determine which organizations were worth targeting based on their security posture, essentially helping them "perfect" their malware before deployment.
"Cybercriminals don't just create malware; they perfect it for maximum destruction," said Douglas Williams, FBI Houston Special Agent in Charge. "By leveraging counter-antivirus services, malicious actors refine their weapons against the world's toughest security systems to better slip past firewalls, evade forensic analysis, and wreak havoc across victims' systems."
Operation Endgame Connection
AVCheck was taken down on May 27, 2025, as part of Operation Endgame's second wave of coordinated activity between authorities in the Netherlands, United States, and Finland.
Intelligence gathered from that takedown led to the identification of the suspect now in custody.
Flight and Capture
According to the Dutch Public Prosecution Service (Openbaar Ministerie), the suspect deregistered from the Netherlands around the time of the AVCheck bust and fled to the United Arab Emirates.
He remained under international surveillance until his arrest upon returning to the Netherlands. Officials did not disclose why he was at the airport.
The suspect and two companies tied to him are accused of enabling cybercriminals and malware developers to access the platform.




