Dutch Police Arrest Third Suspect Behind JokerOTP Phishing Platform That Caused $10M in Losses

Netherlands police have arrested a 21-year-old man from Dordrecht suspected of selling access to the JokerOTP phishing automation platform — a tool designed to intercept one-time passwords through automated voice calls that tricked victims into handing over their MFA codes.
The arrest is the third in a three-year investigation that dismantled the JokerOTP phishing-as-a-service operation in April 2025. Authorities previously arrested the platform's developer and a co-developer who operated under the aliases "spit" and "defone123."
How JokerOTP Worked
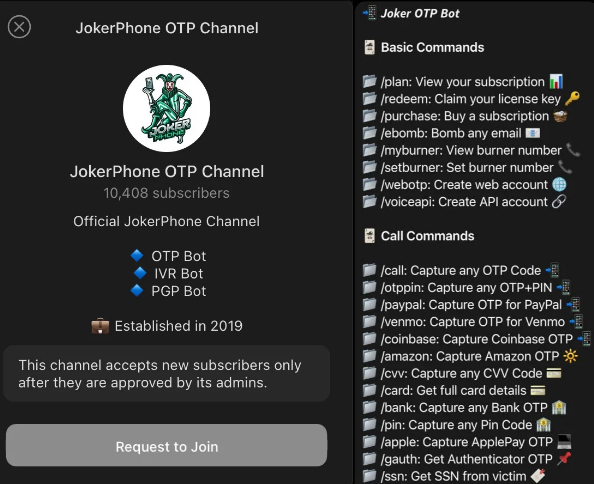
The platform operated on a subscription model, with the arrested suspect selling license keys via Telegram. Subscribers could configure the tool to automate calls to victims and capture OTPs, PINs, card data, and social security numbers. Targets included users of PayPal, Venmo, Coinbase, Amazon, and Apple.
The attack chain exploited a critical timing window. Attackers would use stolen credentials — obtained from infostealer malware or purchased on dark web markets — to initiate a login on a target account. This triggered a legitimate OTP delivery to the victim. Simultaneously, JokerOTP placed an automated call to the victim impersonating the service's security team, requesting the code they had just received.
"Victims were automatically called by the bot and informed that criminals were attempting to gain access to their account," explained Anouk Bonekamp, team leader of Cybercrime Oost-Brabant. "The bot then asked them to enter the one-time password. Victims therefore believe they are protecting themselves by cooperating."
Because the calls coincided precisely with the real authentication prompt, many victims failed to recognize the scam and willingly provided their codes.
Scale and Impact
Over two years of operation, JokerOTP was used in more than 28,000 attacks targeting users across 13 countries, causing an estimated $10 million in financial losses. Compromised accounts were used for unauthorized purchases, fund transfers, and full account takeovers.
Investigation Ongoing
Dutch police confirmed the investigation continues, with dozens of JokerOTP subscribers in the Netherlands already identified and facing prosecution. The takedown underscores law enforcement's increasing focus on the PhaaS ecosystem that enables credential theft at scale.
Recommendation
Users who receive unsolicited calls requesting OTPs or PINs should hang up immediately — legitimate services never ask for authentication codes via phone. Check exposure on Have I Been Pwned, as leaked credentials are the prerequisite for these attacks. Organizations should consider transitioning from SMS and voice-based OTP to hardware security keys or app-based FIDO2 authentication, which are resistant to real-time phishing interception.



