Electron Vulnerability Allows Backdooring of Signal, 1Password, Slack, and Chrome
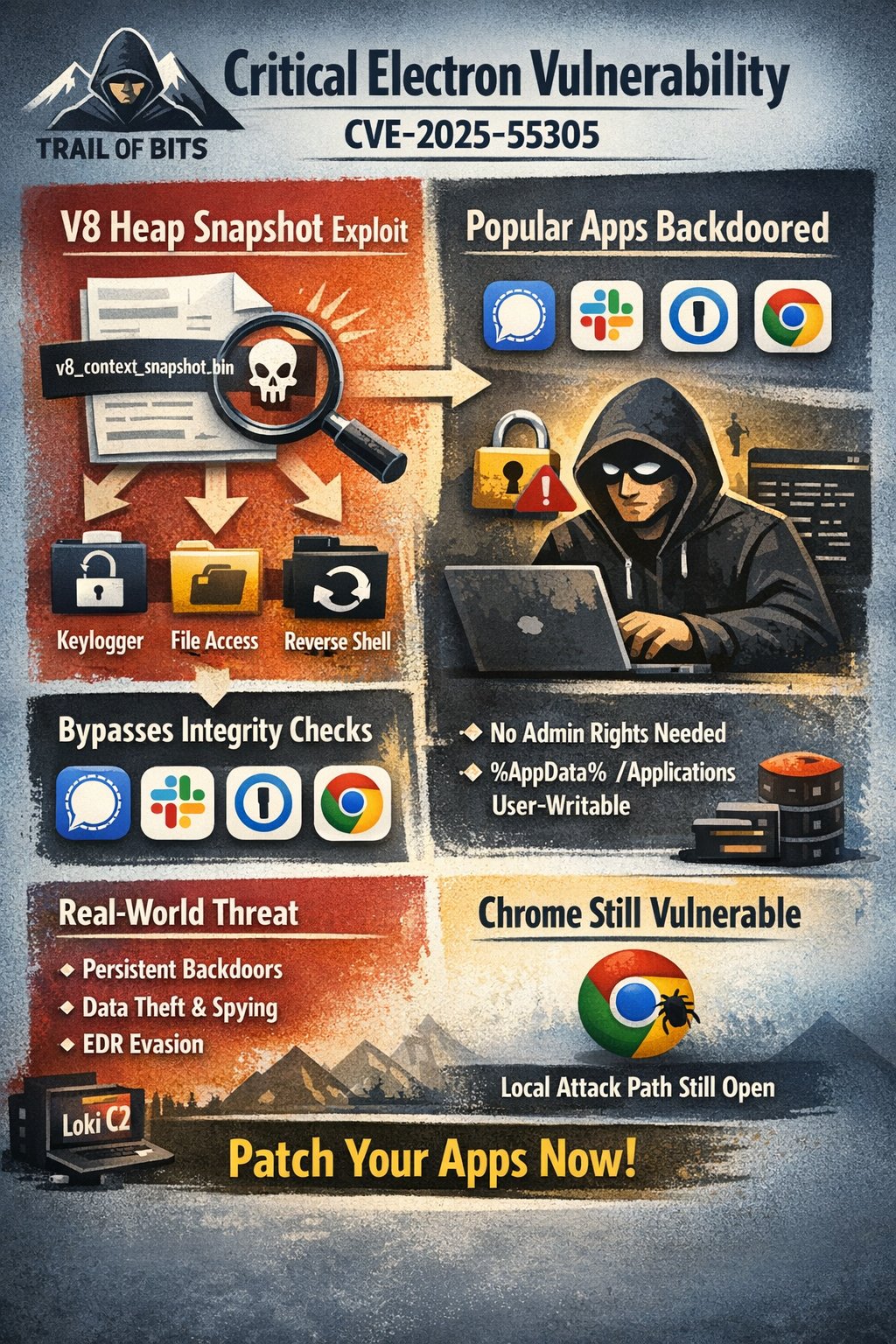
Security researchers at Trail of Bits have discovered a critical vulnerability in Electron-based applications that allows attackers to inject persistent backdoors into Signal, 1Password, Slack, and Chrome by tampering with V8 heap snapshot files.
Tracked as CVE-2025-55305, the flaw bypasses code integrity checks in nearly all applications built on the Chromium engine.
How the Attack Works
Chromium-based applications use V8 heap snapshot files to speed up loading of browser components. These snapshots contain pre-initialized JavaScript engine state that gets loaded directly into memory.
While Electron provides integrity checking fuses to validate application code, researchers found that heap snapshots were not considered "executable" content - and therefore not integrity checked.
An attacker with filesystem write access can overwrite the v8_context_snapshot.bin file with a malicious version. The tampered snapshot:
- Doesn't present as an executable file
- Is not rejected by OS code-signing checks
- Is not integrity-checked by Chromium or Electron
- Gets loaded into every V8 isolate in the application
The Risk
The vulnerability is particularly dangerous because many Chromium applications install to user-writable locations by default:
%AppData%\Localon Windows/Applicationson macOS
This means no privilege elevation is required. An attacker can quietly backdoor existing applications or bring their own vulnerable application.
Proof of Concept
Researchers demonstrated trivial backdoors in high-profile applications including:
- Embedding keyloggers in Slack
- Accessing unconstrained filesystem operations
- Spawning processes
- Loading native code via dlopen
The technique provides access to elevated Node.js functionality in Electron's main process, enabling extensive bypasses of application security controls.
Real-World Abuse
This attack vector is already documented in MITRE ATT&CK as technique T1218.015. The Loki C2 framework uses backdoored versions of trusted applications like VS Code, Cursor, and GitHub Desktop to evade EDR solutions including CrowdStrike Falcon and bypass controls like AppLocker.
Patches and Response
1Password has patched the vulnerability in version 8.11.8-40.
"We were made aware of Electron CVE-2025-55305 through Trail of Bits responsible disclosure and 1Password has patched the vulnerability," said Jacob DePriest, CISO at 1Password. "Protecting our customers' data is always our highest priority."
The Electron team has issued a fix for CVE-2025-55305. Signal and Slack also received courtesy disclosures.
Chrome Remains Vulnerable
Trail of Bits researcher Emilio Lopez demonstrated the same technique works against Chrome and derivative browsers. However, the Chrome team states that local attacks are explicitly excluded from their threat model.
The researchers consider this a realistic avenue for persistent, undetected browser compromise - especially since attackers could distribute copies of Chrome containing malicious code that still pass code signing.
Recommendations
- Update 1Password to v8.11.8-40 or later
- Update Electron-based applications to patched versions
- Monitor for unexpected changes to V8 snapshot files
- Consider installing applications to non-user-writable locations
- Chromium-derivative developers should implement integrity checking on heap snapshots



