EmEditor Supply Chain Attack: Trusted Installer Weaponized to Deploy Multi-Stage Malware
Summary
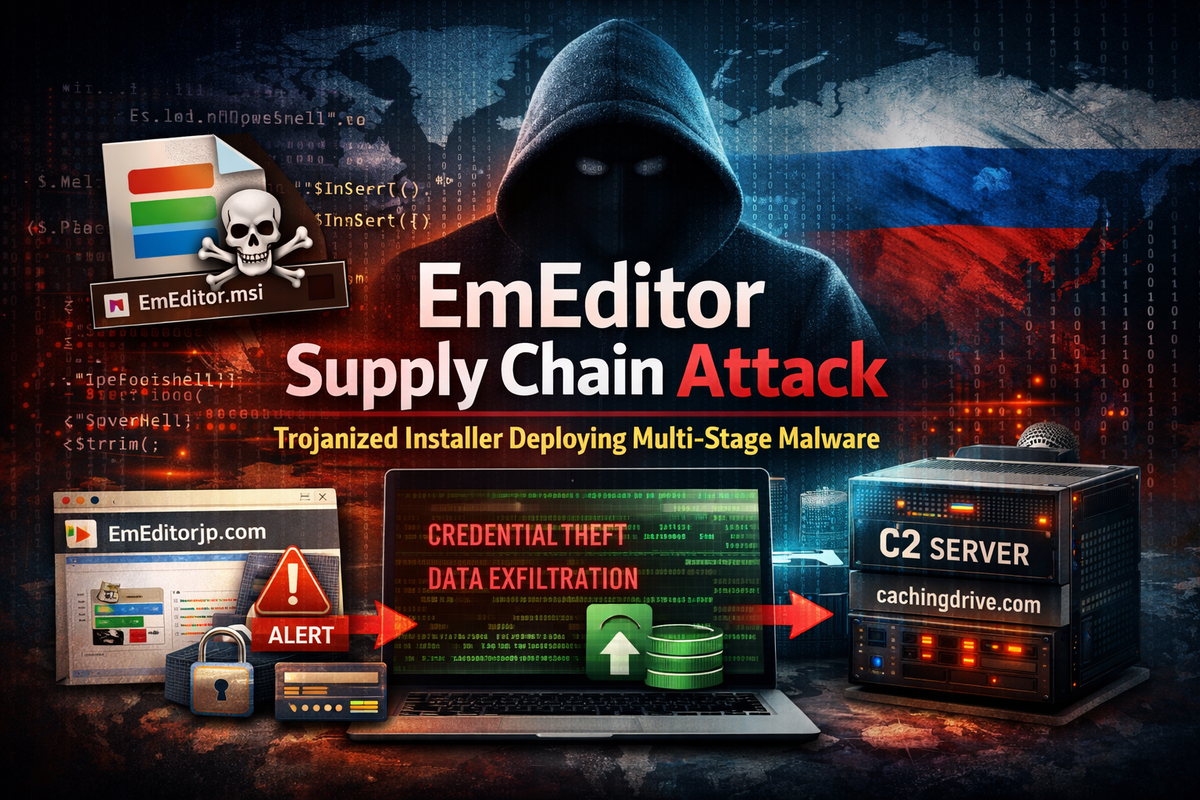
Attackers compromised the official download page of EmEditor, a popular text and code editor, to distribute a trojanized installer containing multi-stage malware. The attack targeted the software's primarily Japanese developer user base during the late December 2025 holiday period when security monitoring typically weakens.
The malware performs credential theft, system reconnaissance, and data exfiltration while employing sophisticated evasion techniques including ETW disabling and anti-virtualization checks.
Attack Overview
In late December 2025, Emurasoft disclosed that their official EmEditor download page had been compromised. Attackers modified the legitimate Microsoft Installer (.MSI) file to execute malicious PowerShell commands upon installation.
The compromised installer retrieves first-stage code from a spoofed domain (EmEditorjp[.]com), which then connects to additional URLs to download the primary payloads. Geofencing behavior in the malware suggests Russian or CIS-origin threat actors, though attribution remains unconfirmed.
Technical Analysis
Initial Infection Vector
The attackers modified the CustomAction script within the MSI installer to execute an obfuscated PowerShell command. The malware uses string manipulation methods (Insert, Remove, Replace, Substring, Trim) for obfuscation across all payload stages.
Payload 1: Anti-Security & Credential Theft
- Disables PowerShell Event Tracing for Windows (ETW)
- Harvests credentials from Windows Credential Manager
- Detects running security software processes
- Implements anti-VM/anti-sandbox evasion
- Captures screenshots for reconnaissance
Payload 2: Persistence & Exfiltration
- Performs system fingerprinting and hardware enumeration
- Scans registry for security applications
- Implements geofencing (blocks execution in Armenia, Belarus, Georgia, Kazakhstan, Kyrgyzstan)
- Establishes C2 communication with cachingdrive[.]com
- Exfiltrates collected data with campaign identifier "2daef8cd"
Indicators of Compromise
| Type | Value |
|---|---|
| Malicious Domain | EmEditorjp[.]com |
| C2 Server | cachingdrive[.]com |
| Campaign ID | 2daef8cd |
Defensive Recommendations
Installer Verification: Validate digital signatures on all installers before execution, even from official vendor sources.
PowerShell Governance: Implement strict logging and monitoring for obfuscated scripts and network-enabled commands.
ETW Monitoring: Alert on attempts to disable Event Tracing for Windows, a key indicator of defense evasion.
Credential Hygiene: Apply least-privilege principles to limit lateral movement opportunities post-compromise.
Telemetry Protection: Monitor for attempts to disable logging mechanisms across endpoints.
Key Takeaway
This incident demonstrates that official vendor download channels are not inherently trustworthy. Organizations must treat all third-party software, regardless of source, as a potential attack vector and implement verification controls accordingly.



