eScan Antivirus Compromised in Supply Chain Attack, Pushes Malware Through Legitimate Updates
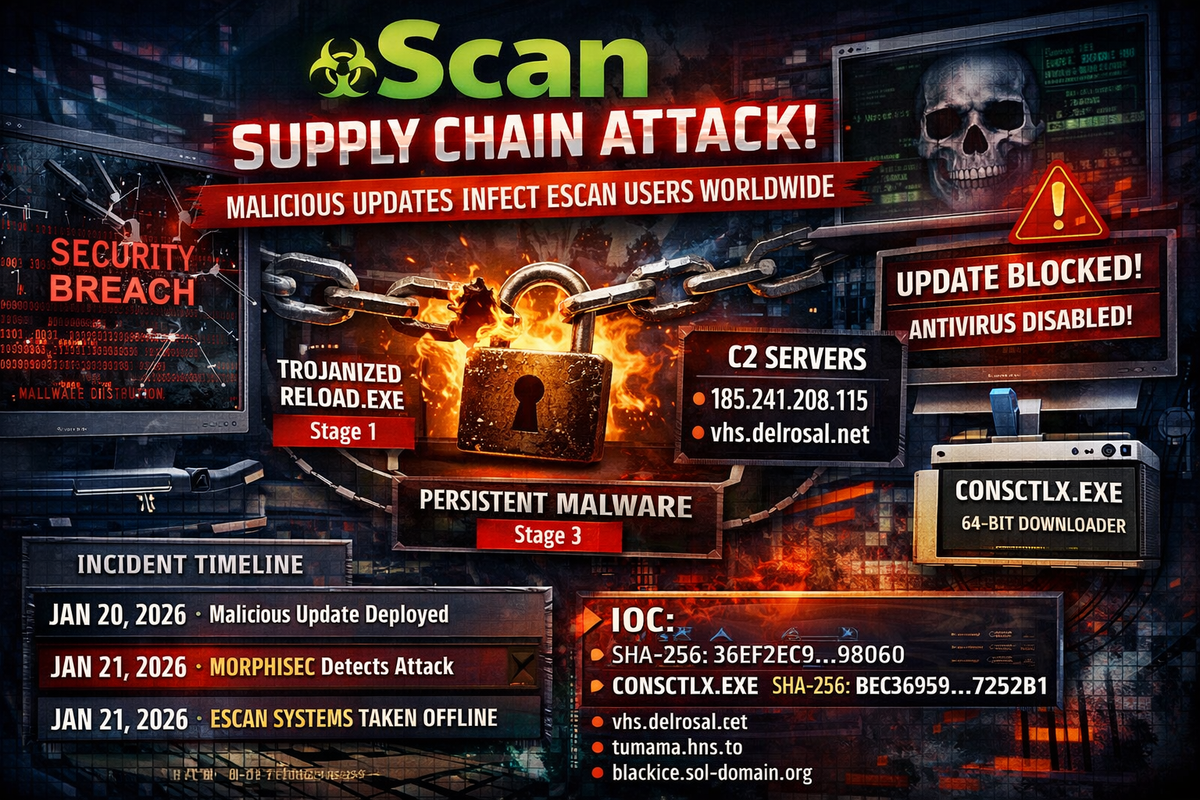
Security firm Morphisec has uncovered a supply chain compromise affecting eScan antivirus software, where attackers distributed malicious updates through the vendor's legitimate update infrastructure.
Discovered on January 20, 2026, the attack targeted both enterprise and consumer editions of the MicroWorld Technologies product, deploying multi-stage malware to endpoints worldwide.
Critical Warning
The malicious payload tampers with eScan's registry, files, and update configuration to prevent future updates and disable antivirus functionality. Automatic remediation is not possible for compromised systems. Affected users must manually contact eScan to obtain the patch.
Attack Chain
The compromise follows a three-stage infection process:
Stage 1: A trojanized version of Reload.exe, a legitimate 32-bit eScan component, is delivered via the update system. The file is signed with eScan's own code signing certificate.
Stage 2: The malware establishes persistence through scheduled tasks, executes PowerShell payloads, and modifies the Windows hosts file to block eScan update servers—preventing the victim from receiving legitimate updates or fixes.
Stage 3: A persistent 64-bit downloader (CONSCTLX.exe) connects to command and control infrastructure for additional payloads.
Incident Timeline
| Date | Event |
|---|---|
| January 20, 2026 | Malicious update distributed via eScan infrastructure |
| January 20, 2026 | Morphisec detects and blocks malicious activity |
| January 21, 2026 | Morphisec contacts MicroWorld Technologies |
| January 21, 2026 | eScan isolates infrastructure within 1 hour, takes update system offline for 8+ hours |
Indicators of Compromise
Trojanized Component (Stage 1):
SHA-256: 36ef2ec9ada035c56644f677dab65946798575e1d8b14f1365f22d7c68269860Persistent Downloader (Stage 3):
Filename: CONSCTLX.exe
SHA-256: bec369597633eac7cc27a698288e4ae8d12bdd9b01946e73a28e1423b17252b1C2 Infrastructure:
hxxps[://]vhs[.]delrosal[.]net/i
hxxps[://]tumama[.]hns[.]to
hxxps[://]blackice[.]sol-domain[.]org
hxxps[://]codegiant[.]io/dd/dd/dd[.]git/download/main/middleware[.]ts
504e1a42.host.njalla.net
185.241.208.115Persistence Mechanisms:
- Scheduled tasks created under
C:\Windows\Defrag\ - Registry keys under
HKLM\Software\<random GUID>containing encoded PowerShell - Hosts file modified to block eScan update servers
Recommended Actions
- Search for the listed hashes across all endpoints
- Review scheduled tasks under
Windows\Defrag\for unexpected entries - Inspect hosts file for entries blocking eScan domains
- Block C2 domains at network perimeter
- Contact eScan directly to obtain the manual patch—do not wait for automatic updates
- Conduct forensic analysis on any system that received updates on January 20, 2026
- Reset credentials for accounts accessed from affected systems
eScan Support Contacts
- Technical Support: support@escanav.com
- Security Inquiries: security@escanav.com
- Enterprise Support: corpsupport@escanav.com



