Fake Notepad++ and 7-Zip Websites Distribute Weaponized RMM Tools to Deploy Backdoor Malware

Threat actors are exploiting legitimate Remote Monitoring and Management software as an initial infection vector, distributing weaponized RMM tools through fake download sites impersonating popular utilities like Notepad++, 7-Zip, Telegram, and ChatGPT, according to research published by ASEC.
The campaigns represent a shift in attacker tactics. Traditionally, threat actors deployed remote control tools after gaining initial network access. These campaigns weaponize legitimate RMM software during the initial infection stage itself, abusing trusted IT administration tools to evade detection by traditional antivirus products.
Fraudulent Download Pages Deliver LogMeIn and PDQ Connect
ASEC researchers uncovered multiple attack campaigns using fraudulent download pages mimicking legitimate software distribution sites. The fake websites impersonate official download portals for widely-used free utilities including Notepad++, 7-Zip, Telegram, ChatGPT, and OpenAI applications.
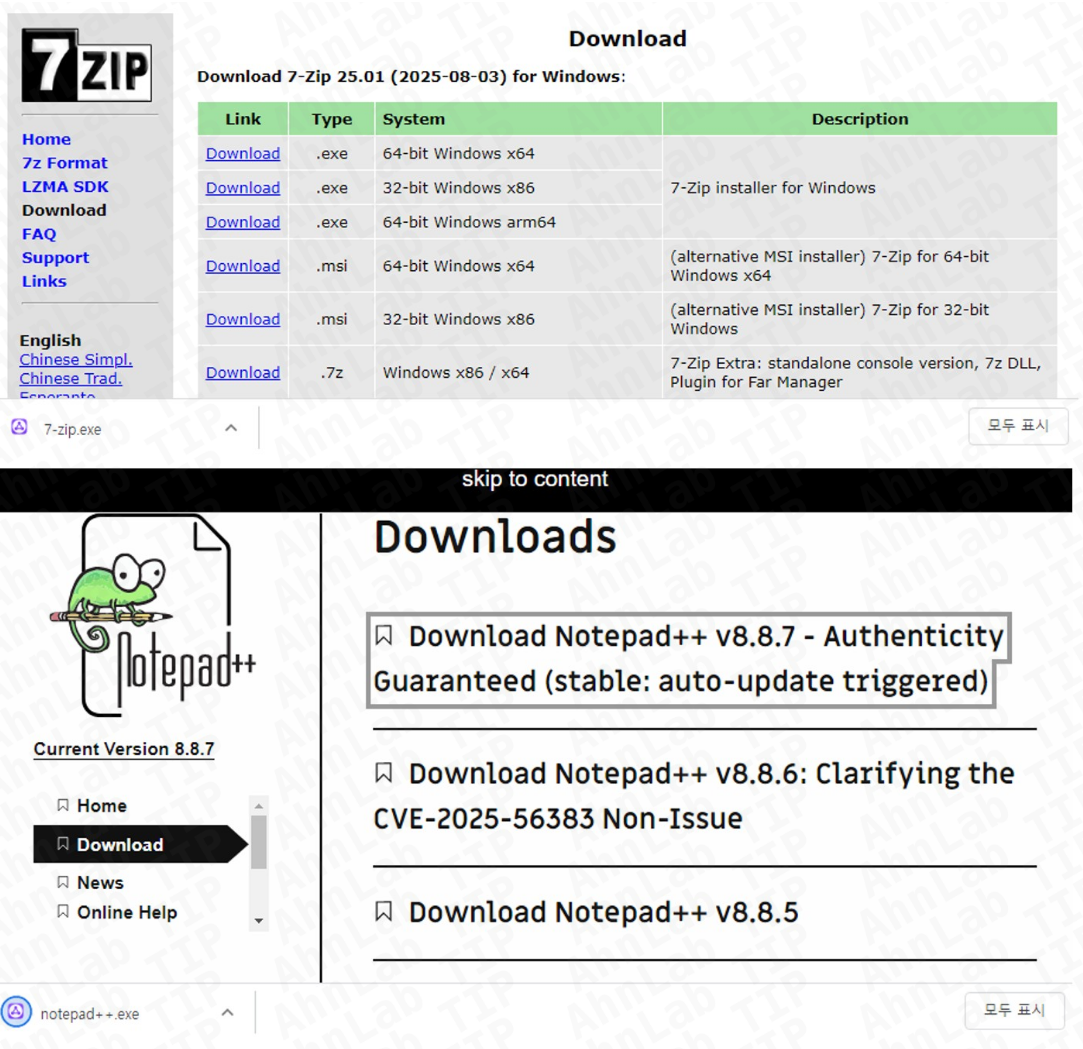
When users attempt to download these tools, they instead receive malicious RMM software controlled by attackers. In one documented campaign, victims downloaded LogMeIn Resolve from counterfeit pages. LogMeIn Resolve is a legitimate RMM tool supporting remote support, patch management, and system monitoring.
Once installed, the software registers with LogMeIn's infrastructure, granting attackers complete remote control over compromised systems. Threat actors exploited this access to execute PowerShell commands and deploy PatoRAT, a backdoor malware enabling persistent system access.
A similar campaign distributed PDQ Connect, another legitimate RMM solution offering software package distribution, patch management, inventory tracking, and remote control capabilities. Like LogMeIn Resolve, PDQ Connect was weaponized to install PatoRAT malware on victim machines.
Phishing Campaigns Distribute Additional RMM Tools
ASEC also identified sophisticated phishing campaigns distributing various RMM tools through malicious email attachments. These attacks employed PDF documents with filenames containing keywords like "Invoice," "Product Order," and "Payment" to appear legitimate.
The PDF files displayed in exceptionally high resolution, making preview impossible and forcing victims to click embedded Google Drive links that downloaded malicious payloads.
These campaigns distributed Syncro RMM, a monitoring and management platform for managed service providers and IT teams. Syncro has been previously exploited by Chaos and Royal ransomware operators, as well as the Iranian APT group MuddyWater.
Six RMM Tools Identified in Campaigns
Analysis of digital certificates revealed additional RMM tools distributed since October 2025, including ScreenConnect, NinjaOne, and SuperOps.
ScreenConnect provides remote access and screen control for troubleshooting and maintenance. The tool has been leveraged by ALPHV/BlackCat and Hive ransomware groups in previous campaigns.
NinjaOne offers cloud-based remote monitoring, patch deployment, and IT asset management. SuperOps delivers integrated RMM and Professional Services Automation capabilities for MSPs, including remote access, asset management, and monitoring functions.
In total, researchers identified six RMM tools being weaponized across these campaigns: LogMeIn Resolve, PDQ Connect, Syncro, ScreenConnect, NinjaOne, and SuperOps.
Detection Challenges
Because RMM tools are legitimate software commonly used in enterprise environments, traditional antivirus solutions face limitations detecting and blocking them without disrupting business operations.
Behavior-based endpoint detection and response solutions can identify suspicious RMM tool execution patterns, alerting administrators to potential compromises before attackers establish persistent access.
Recommendations
Organizations should verify software downloads originate from official websites only, checking version information and digital certificates before installation. Users should exercise caution with emails from unknown senders, avoiding suspicious links and attachments. Maintaining updated operating systems and security products remains essential for protecting against these evolving threats.



