FedEx Database Access Allegedly Sold on Cybercrime Forum via Insider

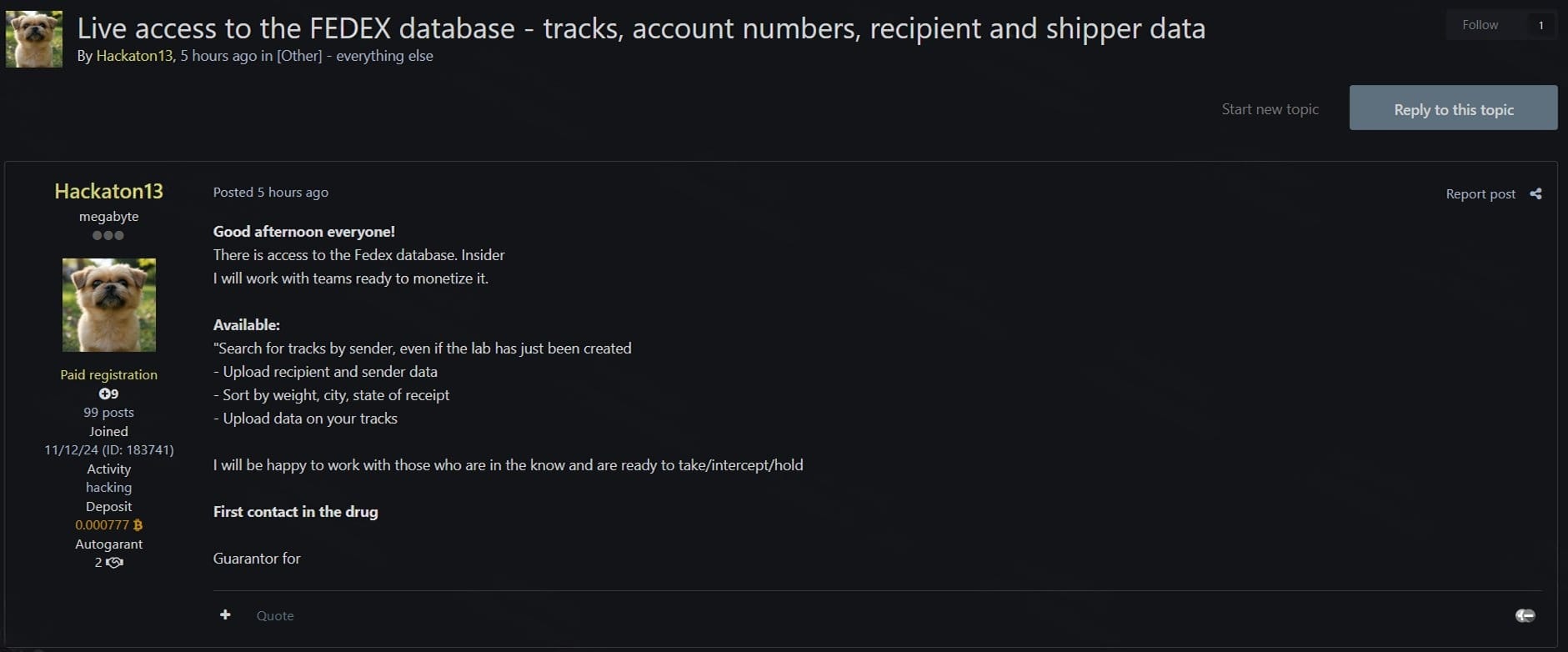
A threat actor is allegedly selling live access to FedEx's internal database through an insider, according to a post on a cybercrime forum.
The seller claims the access enables searching shipments by sender, viewing recipient and shipper details, sorting deliveries by location and package attributes, and the ongoing ability to work with others to target specific shipments.
Insider Threat
Unlike typical data breaches involving stolen databases, this listing advertises continuous access allegedly provided by someone within FedEx's operations. If legitimate, this would allow buyers to identify and potentially intercept high-value shipments in real-time.
Unverified Claims
The authenticity of the alleged access has not been independently verified. FedEx has not publicly commented on any insider compromise. Claims of insider access on cybercrime forums are sometimes exaggerated or fabricated to attract buyers.
Supply Chain Implications
Access to logistics data poses risks beyond customer privacy. Threat actors could use shipment information to identify valuable packages for theft, track executive movements, or gather intelligence on business operations.
Organizations relying on FedEx for sensitive shipments should monitor for any unusual activity and consider additional security measures for high-value deliveries.



