GhostChat Spyware Uses Romance Scams and WhatsApp Hijacking to Target Pakistani Android Users
Security researchers have uncovered a coordinated espionage campaign targeting Android users in Pakistan through a spyware operation that combines romance-themed social engineering, mobile surveillance, and WhatsApp account hijacking.
ESET researchers track the Android component as GhostChat, a spyware that masquerades as a dating application while exfiltrating sensitive data and enabling attackers to hijack victims' WhatsApp sessions.
The Lure: Fake Dating App
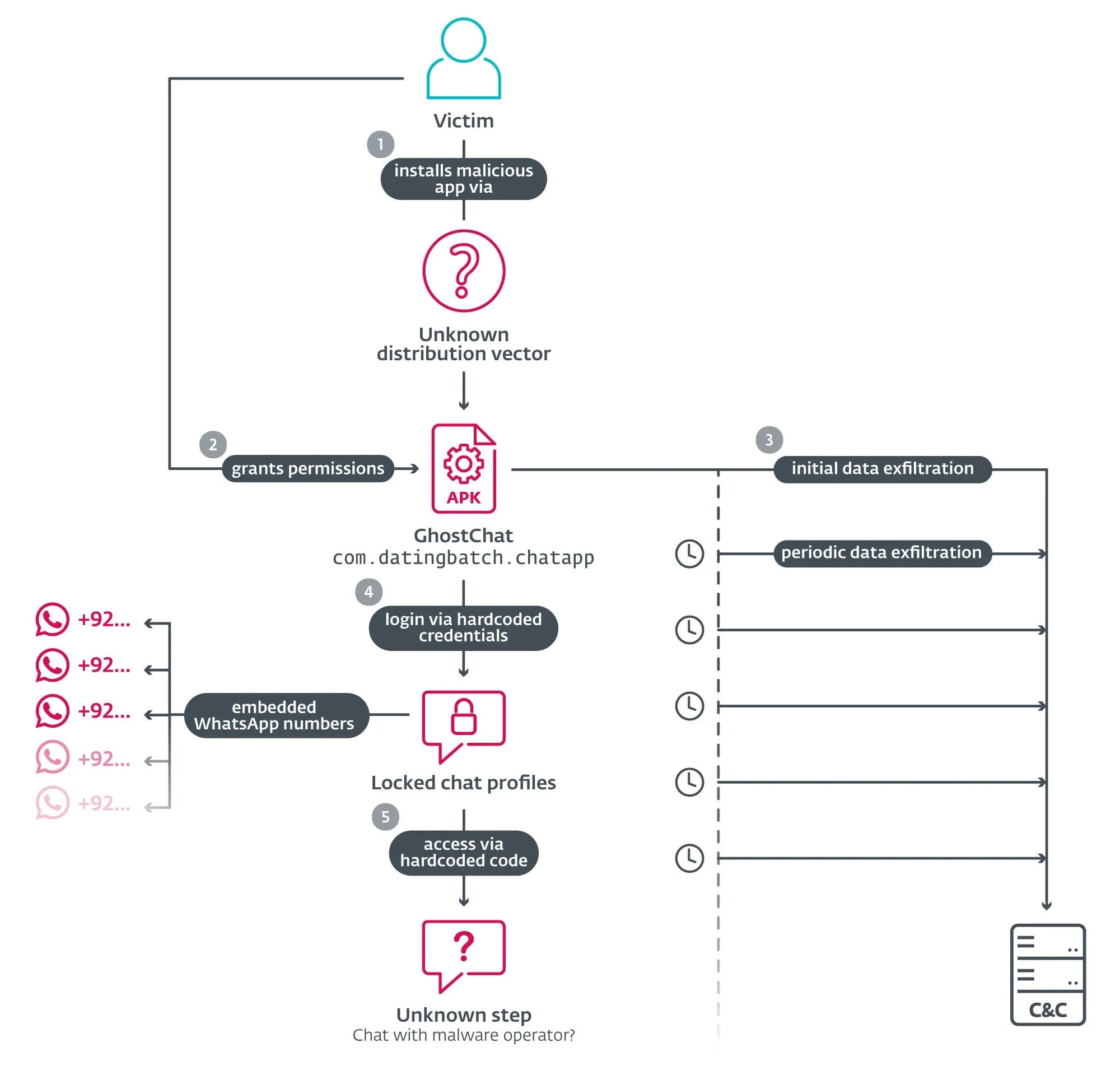
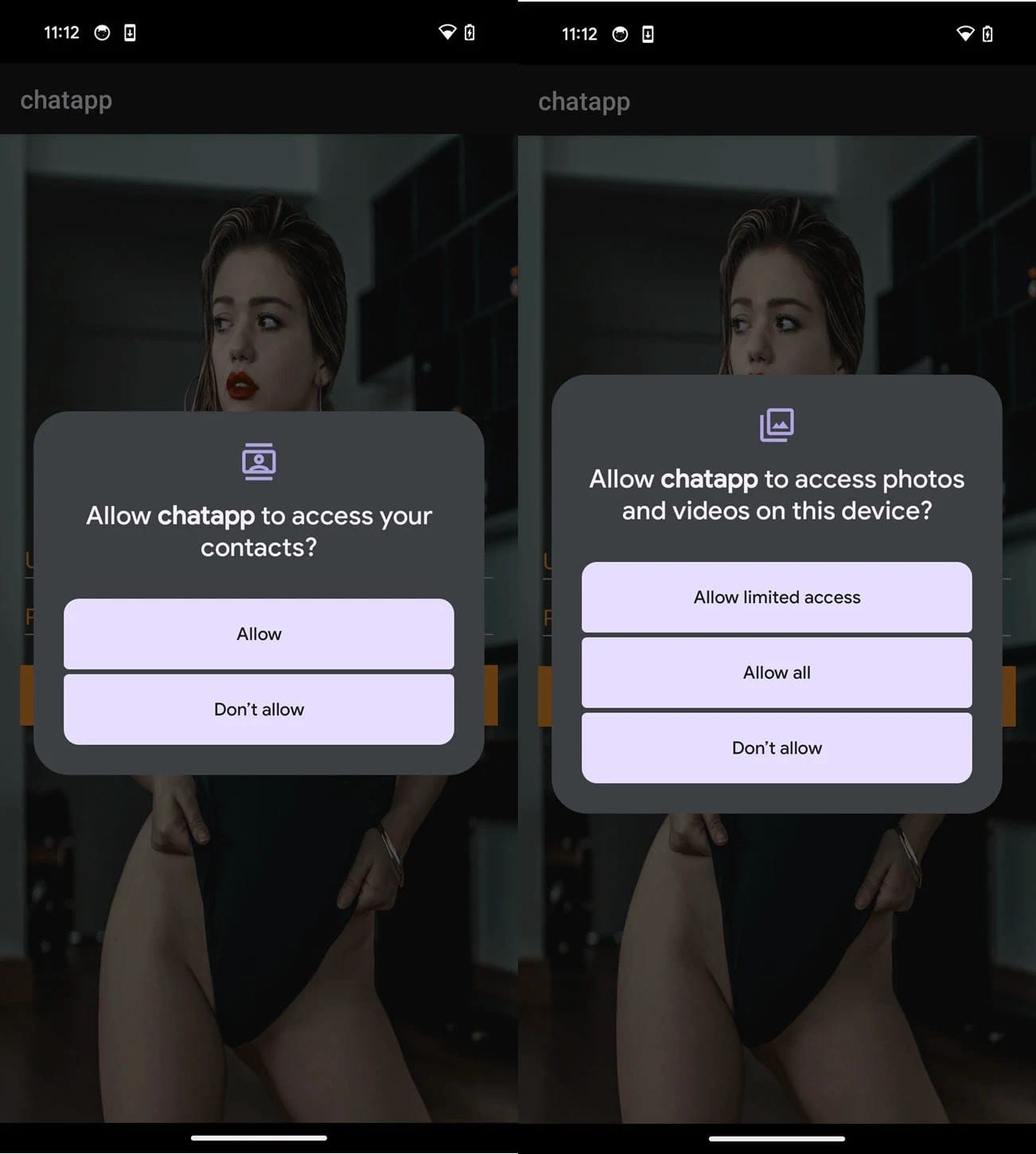
GhostChat disguises itself as a legitimate chat platform called "Dating Apps without payment," stealing the icon from a real application to build trust. The malware is distributed outside Google Play, requiring victims to sideload the APK—a common distribution method for targeted mobile espionage.
Upon installation, the app displays a login screen with hardcoded credentials (username: "chat", password: "12345"). After authentication, victims see 14 fake female profiles, each locked behind preset codes shared by the attackers.
These profiles link to Pakistani WhatsApp numbers (+92 country codes). When victims enter a code, they're redirected to WhatsApp for conversations controlled by the threat actors. This creates a false sense of exclusivity while masking the spyware's true purpose: continuous surveillance.
Persistent Data Theft
GhostChat activates in the background even before the victim completes login, immediately beginning data exfiltration to a command-and-control server at hitpak[.]org.
The malware harvests device identifiers, complete contact lists exported as text files, and stored documents including images, PDFs, Word documents, Excel spreadsheets, and PowerPoint files.
To ensure ongoing surveillance, GhostChat sets content observers that instantly upload new photos and runs scheduled tasks every five minutes to scan for and steal fresh documents.
WhatsApp Session Hijacking: GhostPairing
Beyond traditional spyware capabilities, the operation employs a technique researchers dubbed GhostPairing to hijack victims' WhatsApp accounts.
Attackers operate fake Ministry of Defence pages that push QR codes for supposed "community joins." When victims scan these codes, they unknowingly link their WhatsApp account to the attacker's WhatsApp Web session.
Victims receive a new device notification approximately two hours later, but by then the damage is done. Attackers gain full access to read messages, contacts, and chat history with owner-level privileges. This technique echoes previous campaigns like BadBazaar that targeted Signal users.
Cross-Platform Infrastructure
Analysis of the C2 server revealed the same threat actors operate linked Windows malware operations. Batch scripts on the server fetch and execute a DLL from hitpak[.]org/notepad2[.]dll using ClickFix-style social engineering—fake alerts that trick users into executing malicious code via rundll32.exe.
One related site, buildthenations[.]info/PKCERT/pkcert.html, impersonates Pakistan's national CERT, displaying fake warnings about national threats to convince victims to download malware.
The Windows payload (detected as Win64/Agent.HEM) phones home with machine details, then polls every five minutes for base64-encoded PowerShell commands executed in hidden mode.
Indicators of Compromise
Android:
- SHA-1: B15B1F3F2227EBA4B69C85BDB638DF34B9D30B6A (Live Chat.apk)
- Detection: Android/Spy.GhostChat.A
Windows:
- SHA-1: 8B103D0AA37E5297143E21949471FD4F6B2ECBAA (file.dll)
- Detection: Win64/Agent.HEM
Network Infrastructure:
- hitpak[.]org (C2 server)
- hitpak[.]org/notepad2[.]dll (payload delivery)
- buildthenations[.]info/PKCERT/pkcert.html (fake PKCERT)
- 188.114.96[.]10 (Cloudflare-hosted C2)
Recommendations
- Block installation of applications from unknown sources
- Scrutinize apps requesting excessive permissions immediately after install
- Check WhatsApp linked devices regularly and revoke unknown sessions
- Enable Google Play Protect on all Android devices
- Be suspicious of login screens with preset or shared credentials
- Treat unsolicited dating app recommendations with extreme caution
Attribution
First spotted via VirusTotal upload from Pakistan on September 11, 2025, no firm attribution has been established. However, the multi-platform infrastructure and coordinated tactics suggest a well-resourced espionage operation rather than commodity cybercrime.



