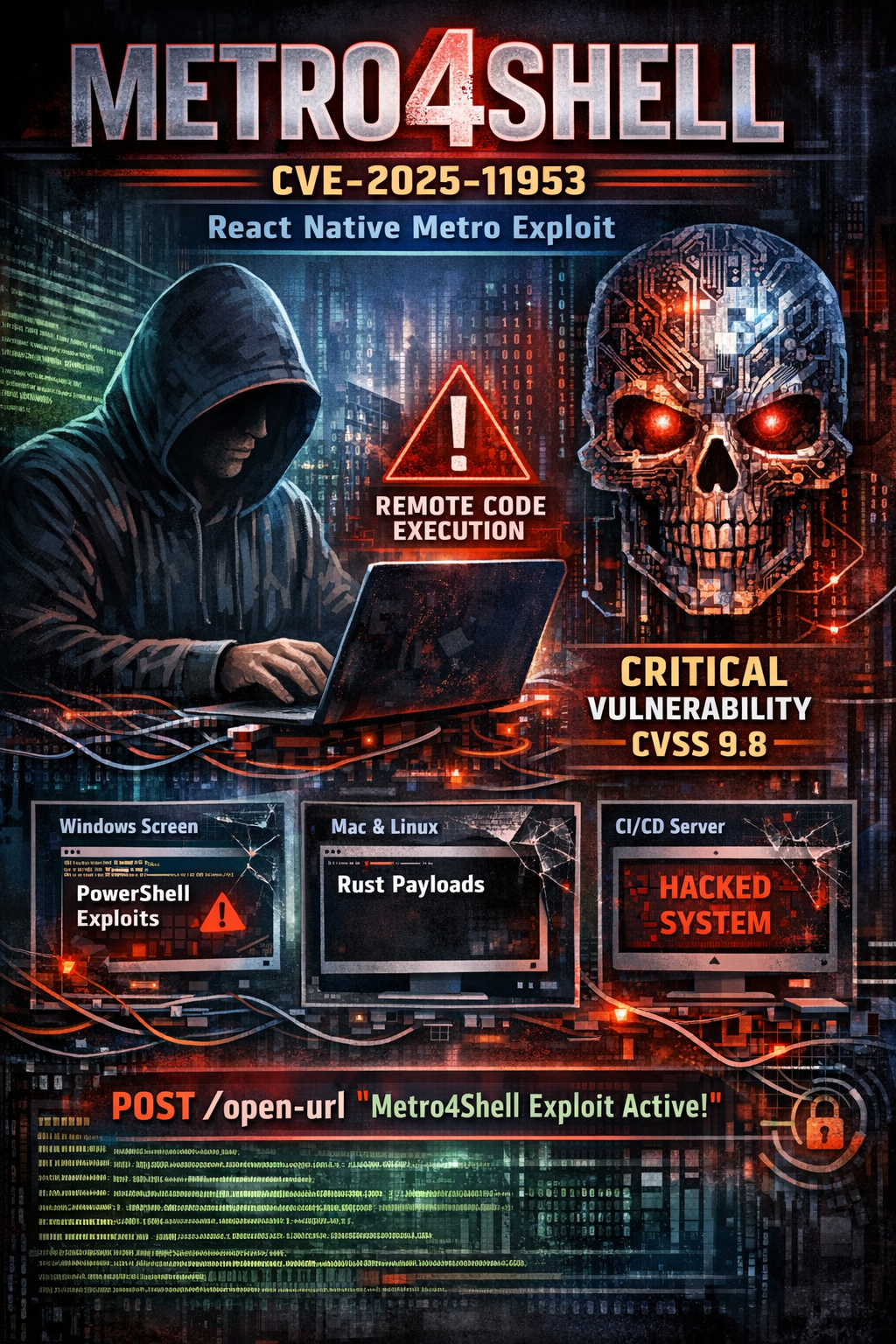
Hackers Exploit Critical React Native Metro Flaw to Compromise Developer Systems (CVE-2025-11953)
A critical vulnerability in the React Native Community CLI Metro development server is being actively exploited to compromise developer workstations and CI/CD environments.
Tracked as CVE-2025-11953 and dubbed Metro4Shell, the flaw carries a CVSS score of 9.8 and allows unauthenticated OS command injection through the server's /open-url endpoint. When Metro is accessible beyond localhost, attackers can achieve remote code execution with the privileges of the developer running the service.
Sustained Exploitation Confirmed
VulnCheck's Canary network has observed exploitation activity dating back to December 21, 2025, with additional waves on January 4 and January 21, 2026. The sustained campaign marks a significant escalation from November 2025, when no in-the-wild exploitation had been confirmed.
Attackers are sending crafted POST requests to exposed Metro instances, with observed post-exploitation activity including PowerShell-based loaders and Rust-compiled payloads.
How It Works
The vulnerability exists in the @react-native-community/cli-server-api package, affecting versions from 4.8.0 through 20.0.0-alpha.2. The /open-url handler processes attacker-supplied input without adequate sanitization, allowing it to reach OS execution paths — a classic CWE-78 command injection condition.
Exploitation requires the Metro server to be actively running and reachable from outside localhost. This makes the following environments particularly vulnerable:
- Developer laptops on shared or untrusted networks
- CI runners and build agents where Metro starts during workflows
- Development hosts where Metro listens on non-local interfaces
Impact varies by platform. On Windows, attackers achieve arbitrary shell command execution. On macOS and Linux, exploitation allows execution of arbitrary binaries with more limited parameter control, but still sufficient for initial access.
Critically, the flaw does not affect production React Native applications — only development and build infrastructure.
Patching and Hardening
Patches are available in versions 18.0.1, 19.1.2, and 20.0.0+. Organizations should verify the actual version in use, as the vulnerable package may be pulled through nested dependencies or global CLI installations rather than appearing directly in project manifests.
Check both locations:
npm list @react-native-community/cli-server-api
npm list -g @react-native-community/cli-server-apiBeyond patching, defenders should bind Metro to localhost explicitly using --host 127.0.0.1, apply host firewall rules to block inbound access to the Metro port, and avoid running Metro on internet-accessible machines.
Detection Opportunities
Security teams should monitor for unauthenticated POST requests to /open-url against developer endpoints and build agents. On Windows, look for suspicious PowerShell encoded commands and attempts to add Microsoft Defender exclusions prior to payload retrieval — a pattern consistent with observed exploitation chains.



