Initial Access Broker TA584 Deploys High-Speed Phishing Campaigns with ClickFix Social Engineering and New Tsundere Bot Backdoor

The financially motivated threat actor TA584 has significantly escalated its initial access operations, adopting a high-speed attack model built around short-lived campaigns, rapid infrastructure changes, and aggressive social engineering techniques, according to research published by Proofpoint.
The evolution reflects a broader shift in modern cybercrime where speed and adaptability now outweigh long-term persistence, with attack waves often lasting only a few hours before being dismantled and replaced with entirely new infrastructure.
Initial Access Broker Model
TA584 operates primarily as an Initial Access Broker, focusing on gaining early footholds inside enterprise environments rather than executing final-stage attacks. Compromised access is either monetized directly through sale to other threat actors or leveraged to deploy secondary payloads including ransomware.
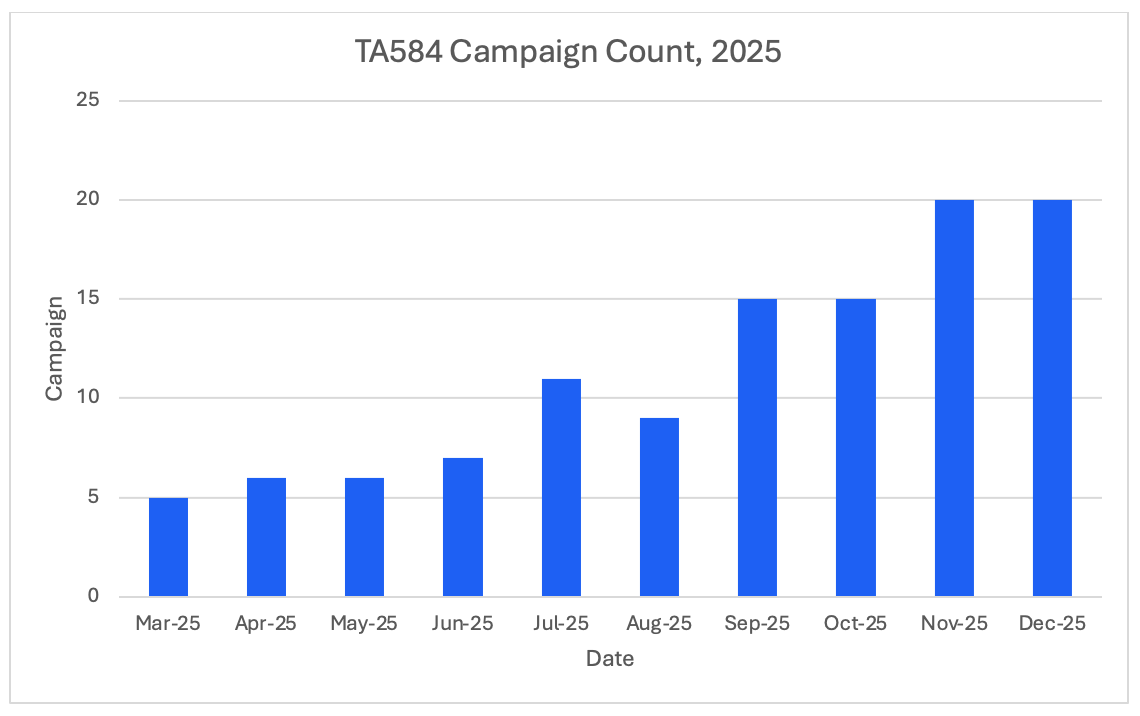
Recent activity shows a sharp increase in campaign frequency throughout 2025, with the operational tempo accelerating significantly. This high-velocity approach allows TA584 to evade detection and takedown efforts while maximizing the window for successful compromises.
Email Phishing with Dynamic Lures
TA584 relies heavily on email phishing campaigns to initiate compromise. Lures impersonate legitimate organizations across multiple sectors including finance, healthcare, recruitment, and government services. Messages are carefully crafted to trigger urgency or curiosity, driving users to malicious landing pages.
These landing pages frequently employ geofencing and content filtering, altering what is displayed based on the victim's location, browser, or IP address. This tactic reduces exposure to automated analysis tools and security researcher sandboxes while improving the success rate of human interaction.
ClickFix Social Engineering Technique
A defining tactic in TA584 campaigns is ClickFix-style social engineering. Victims are presented with fake error messages or CAPTCHA-style verification prompts that instruct them to copy and execute commands. These commands typically launch PowerShell, which retrieves and executes obfuscated scripts directly in memory.
This fileless execution technique minimizes forensic artifacts on disk and allows attackers to bypass traditional signature-based endpoint protections. By tricking users into manually executing the malicious commands, TA584 also bypasses email security controls that would normally block malicious attachments or links.
New Tsundere Bot Backdoor
TA584 continuously rotates malware payloads to avoid detection. New and customized implants have been observed, including a recently identified backdoor known as Tsundere Bot. The malware demonstrates modular command execution and remote control capabilities, allowing operators to adapt functionality based on the compromised environment.
The emphasis on payload experimentation highlights TA584's focus on scalability rather than stability. By constantly introducing new malware variants, the threat actor stays ahead of signature-based detection while testing which implants perform best across different target environments.
Defensive Recommendations
TA584's operations demonstrate why static indicators of compromise are no longer sufficient for defense. The rapid infrastructure rotation means IP addresses, domains, and file hashes become obsolete within hours of identification.
Effective defense requires behavior-based detection focused on monitoring PowerShell and script execution patterns, correlating email-to-endpoint activity to identify users who clicked phishing links and subsequently executed suspicious commands, and identifying abnormal user interaction patterns that may indicate ClickFix-style social engineering.
Organizations should implement controls that prevent users from executing arbitrary PowerShell commands, particularly those copied from external sources. Security awareness training should specifically address ClickFix techniques where fake error messages instruct users to run commands.
As TA584 continues to refine its initial access tradecraft, organizations must adapt defenses to counter high-velocity, socially engineered intrusion campaigns designed to evade traditional security controls.



