Inside the Lazarus Group's Contagious Interview Machine: 857 Developers Compromised, 241,000 Credentials Stolen
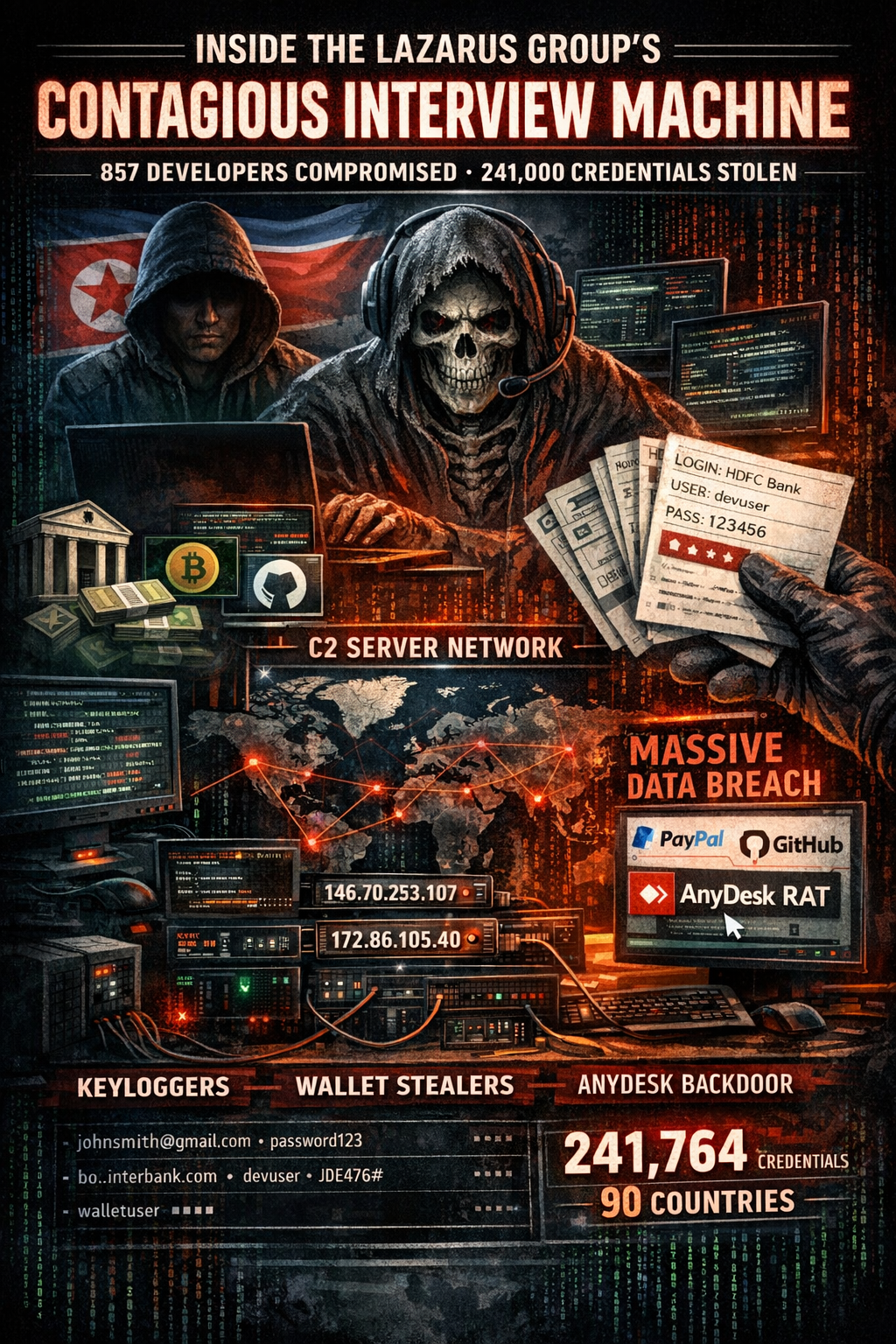
A months-long offensive investigation by Red Asgard's threat research team has produced one of the most detailed public examinations of North Korea's Contagious Interview campaign infrastructure ever published. The findings — spanning four malware families, approximately 20 previously undocumented C2 servers, a novel binary protocol, and unauthenticated endpoints exposing a quarter-million stolen credentials — paint a picture of industrial-scale credential theft targeting the global freelance developer community.
The investigation, published across two research installments (Parts III and IV of an ongoing series), began with the discovery of a new malware family and ended with the recovery of 241,764 plaintext credentials belonging to 857 victims across 90 countries — including logins for banking platforms, cryptocurrency wallets, and developer services.
Red Asgard filed reports with FBI IC3 and CISA before the deepest findings, then continued digging.
The Campaign: Contagious Interview
Contagious Interview is Lazarus Group's long-running social engineering operation targeting software developers through fake job interviews. The attack vector is consistent: recruiters on platforms like Upwork and Fiverr approach developers with coding tests or repository reviews. The repositories contain malicious code that executes on open — via VSCode auto-run tasks, npm install scripts, or embedded payloads — deploying multiple malware families in sequence.
Previous research by SentinelOne, Sekoia, and Unit42 has documented the campaign's BeaverTail and InvisibleFerret malware families. Red Asgard's investigation adds two previously undocumented families — OtterCookie and an AnyDesk RAT — while mapping the operational infrastructure behind the campaign at a depth not previously achieved.
OtterCookie: A More Capable Second-Stage Implant
In late January 2026, Red Asgard identified a new Vercel domain (tetrismic.vercel.app) delivering a 43KB JavaScript payload structurally distinct from BeaverTail. The payload contained a hardcoded C2 IP (172.86.105.40:5918) and campaign identifiers not present in any public threat intelligence database at the time of discovery.
The malware, designated OtterCookie (consistent with naming conventions used by other Contagious Interview researchers), represents a significant capability upgrade over BeaverTail.
Keylogging
OtterCookie deploys a system-wide keyboard hook via GlobalKeyboardListener that captures every keystroke — not just browser input, but passwords typed into desktop applications, terminal commands, and messaging apps. Keystrokes buffer until the user presses Enter, then flush to the C2's /clip endpoint.
Screenshot Capture
Every five seconds, OtterCookie captures all connected monitors, XOR-encrypts the combined image with key 0x5A, and uploads to the C2. Multi-monitor support is deliberate — the operators anticipate developer workstations with multiple displays.
Persistence
Unlike BeaverTail, which had no persistence and relied on VSCode re-execution (meaning a reboot killed the implant), OtterCookie implements two independent persistence mechanisms:
- Registry Run Key:
HKCU\...\Run→ "NodeHelper" →node index.js - Scheduled Task: "NodeUpdate" → runs at logon with highest privileges
If one mechanism is cleaned, the other reinstates the malware on next login.
VM Detection
OtterCookie fingerprints the execution environment across Windows, macOS, and Linux, detecting VMware, VirtualBox, QEMU, Parallels, KVM, Xen, Bochs, and Hyper-V. If a virtual machine is detected, the malware degrades its behavior — explaining why sandbox analysis may capture an incomplete picture of its capabilities.
27 Wallet Extensions Targeted
OtterCookie targets 27 cryptocurrency wallet browser extensions — a massive expansion from BeaverTail's 2-3 targets. The target list includes MetaMask, Phantom, Keplr, Binance Chain, Core, Tonkeeper, Trust, Coinbase, Rabby, Brave, Exodus, OKX, SafePal, Math, ONTO, MyEtherWallet, TronLink, Ronin, Temple, and Nami, among others. For each extension, OtterCookie extracts vault data (encrypted private keys), seed phrase backups, IndexedDB contents, Secure Preferences, and Service Worker data.
BeaverTail vs OtterCookie Comparison
C2 Protocol — BeaverTail: HTTP + Socket (port 1244) / OtterCookie: HTTP only (port 5918) Keylogger — BeaverTail: No / OtterCookie: System-wide (GlobalKeyboardListener) Screenshot — BeaverTail: No / OtterCookie: All monitors, 5-second interval, XOR 0x5A Persistence — BeaverTail: None (VSCode re-execution) / OtterCookie: Registry Run key + Scheduled Task VM Detection — BeaverTail: VirtualBox MAC only / OtterCookie: Full (VMware, QEMU, KVM, Xen, Parallels, Bochs) Wallet Targets — BeaverTail: 2-3 extensions / OtterCookie: 27 extensions Clipboard — BeaverTail: Every 3 seconds / OtterCookie: Every 5 seconds Obfuscation — BeaverTail: 64 nested layers / OtterCookie: Single-layer JavaScript
The two families provide complementary coverage: BeaverTail handles initial access and evasion through deep obfuscation, while OtterCookie delivers persistent, comprehensive data collection.
The Ghost Server Network
While pivoting from the OtterCookie C2, Red Asgard identified approximately 20 additional servers not present in any public threat intelligence database. The discovery came from infrastructure correlation — same hosting providers, adjacent IP ranges, and a distinctive port fingerprint that made the pattern unmistakable.
Every server presented the same 13 ports:
- 21/tcp — FTP — Data exfiltration
- 80/tcp — HTTP — Web interface
- 443/tcp — HTTPS — Encrypted web
- 1224/tcp — Custom — BeaverTail alternate C2
- 1244/tcp — Express.js — BeaverTail primary C2
- 3389/tcp — RDP — Operator access
- 5918/tcp — Custom — OtterCookie primary C2
- 5934/tcp — Custom — OtterCookie alternate
- 5961/tcp — Custom — OtterCookie alternate
- 5974/tcp — Custom — OtterCookie alternate
- 5985/tcp — WinRM — Remote management
- 8000/tcp — HTTP — Custom application
- 54321/tcp — Unknown — Unknown purpose
This level of consistency across approximately 20 Windows servers spanning three hosting providers (Majestic Hosting, TIER-NET, EuroHoster) is not manual configuration. This is Infrastructure-as-Code — a deployment template executed consistently across every server. The port list also confirms both malware families operate from the same infrastructure: port 1244 serves BeaverTail, port 5918 serves OtterCookie.
Detection opportunity: Any server presenting the unusual combination of ports 1224, 1244, 5918, 5934, 5961, and 5974 simultaneously is likely Lazarus infrastructure, even if the IP has not yet been flagged in threat intelligence feeds.
Five confirmed C2 IPs fall within a single /20 netblock — 147.124.208.0/20 — owned by Majestic Hosting Solutions (SpinServers) in Carrollton, Texas (AS396073), with the IPs distributed across four different /24 subnets to avoid pattern-based detection.
The Honeypot Question
Red Asgard attempted to exploit the C2 infrastructure — and encountered something unprecedented. They systematically probed the Express.js services across multiple C2 IPs, testing 11 vulnerability classes. SSTI across six template engines, prototype pollution, HTTP request smuggling, XXE, command injection, deserialization, SSRF, file upload RCE, CRLF injection, three Express.js CVEs, and FTP brute force. Every single one came back not vulnerable.
Zero out of eleven. In Red Asgard's experience across years of testing APT infrastructure, they had never encountered a criminal C2 server with a perfect security posture.
Combined with five additional anomalies — an exposed private key at /cert/private.pem (likely bait), every upload returning "DONE" regardless of content (data sink behavior), performative rate limiting trivially bypassed by changing VPN exit country, no evidence of real victim traffic on command polling endpoints, and deployment timing coinciding with Red Asgard's investigation — the researchers assigned a 70/30 probability that the standardized servers were a honeypot or counter-intelligence operation.
They recommended: do not trust data obtained from these servers.
Then they found the data.
241,764 Stolen Credentials: The Honeypot Theory Dies
While debating probabilities, Red Asgard kept probing. The C2 server at 146.70.253.107:1224 exposes unauthenticated HTTP endpoints — /uploadInfo and /uploadFile — defined in the malware's own source code. These are not hidden admin panels. The malware instructs victims to POST stolen data to these endpoints, and the endpoints serve that data back to anyone who sends a GET request with a valid campaign ID.
Campaign 5346 returned 121 victims with 31,473 credentials. Campaign 15 returned 287 victims with 72,493 credentials. Campaign 99 returned 449 victims with 137,798 credentials.
Total: 857 compromised developer workstations. 241,764 credentials. 90 countries.
The honeypot theory collapsed under the weight of the data. Test infrastructure does not contain credentials for HDFC Bank and PayPal from 90 different countries. Counter-intelligence operations do not fabricate a quarter-million credential records with internally consistent timestamps spanning weeks of real-time collection.
What Was Stolen
Every credential record sat in plaintext — not hashes, not encrypted blobs — on a server that responded to unauthenticated HTTP requests. Each record included the URL, username, plaintext password, victim hostname, timestamps, IP address, country, and a cache_path pointing to a downloadable archive of the victim's full browser data.
Banking and Financial Services: HDFC Bank (India), Bank of America, Charles Schwab, OTP Bank (Hungary), Bankinter (Spain), Scotia (Costa Rica), DBS Bank (Singapore), Revolut, Wise, PayPal, Payoneer, Stripe, plus credentials for MetaMask, Phantom, Coinbase, Trust Wallet, and 23 additional wallet extensions.
Developer Platforms: 2,647 GitHub credentials, 969 Upwork credentials, 4,280 Google accounts, plus 2,808 localhost:3000 (React default) and 665 localhost:5173 (Vite default) credential entries — a forensic fingerprint that only exists on active developer workstations running local development environments.
Lure Domains: Two domains appeared repeatedly as credential origins — elvengold.com (573 credentials) and email.tokenloopz.com (189 credentials). These are fake project websites where victims sign up during the "interview" process. Password reuse turns these fake signup forms into skeleton keys for victims' real accounts.
Geographic Distribution
- India — 6,863 credentials (2.8%)
- Bangladesh — 4,979 credentials (2.1%)
- Vietnam — 3,301 credentials (1.4%)
- Pakistan — 2,933 credentials (1.2%)
- United States — 2,396 credentials (1.0%)
- Russia — 1,859 credentials (0.8%)
- Nigeria — 1,685 credentials (0.7%)
- Sri Lanka — 1,475 credentials (0.6%)
- Croatia — 1,233 credentials (0.5%)
- France — 1,125 credentials (0.5%)
The remaining credentials span 80 additional countries. The concentration in South Asia aligns precisely with the Upwork/Fiverr freelancer ecosystem — the regions where a disproportionate share of remote software development talent is sourced. These are developers competing for freelance work on global platforms, often in economies where a compromised bank account represents months of income.
The AnyDesk RAT: A Fourth Malware Family
While enumerating C2 endpoints, Red Asgard discovered a fourth malware family — a purpose-built AnyDesk deployment and backdoor tool that completes the attack chain with persistent remote desktop access.
The attack sequence:
- Downloads AnyDesk from the C2 via
GET /any - Installs and launches AnyDesk silently
- Waits for AnyDesk to generate configuration files
- Steals the victim's AnyDesk credentials from
service.conf - Exfiltrates stolen credentials via
POST /keysover plaintext HTTP - Injects hardcoded attacker credentials into the victim's AnyDesk configuration
- Restarts AnyDesk with the backdoor credentials active
After step 7, the operators have persistent remote desktop access that survives password changes on other services, network changes, and reboots. The victim would need to specifically audit their AnyDesk installation to detect the compromise.
The AnyDesk RAT communicates with a separate C2 (95.164.17.24:1224) obfuscated using a simple base64 rotation — split the string at position 8, swap halves, decode. Three campaign variants were recovered (IDs: 5346, hkMrMq7, team15), all sharing the same C2 infrastructure and hardcoded attacker credentials:
pwd_hash: 967adedce518105664c46e21fd4edb02270506a307ea7242fa78c1cf80baec9d
pwd_salt: 351535afd2d98b9a3a0e14905a60a345
token_salt: e43673a2a77ed68fa6e8074167350f8fThis completes a full attack chain: initial access via fake job interview → credential theft via browser stealer → persistent remote access via AnyDesk backdoor.
Breaking Into the Operator Panel
Red Asgard's investigation revealed a critical architectural gap in Lazarus's infrastructure. The approximately 20 hardened front-end servers documented in the honeypot analysis are victim-facing data collection nodes. Behind them sits 146.70.253.107 — the operator server — running on XAMPP with Apache 2.4.58 and PHP 8.1.25 on Windows Server 2022.
The operator endpoints (/info, /allinfo, /getUser, /rSvr, /dumpsql) exist exclusively on this one server. The victim-facing servers respond only to /uploadInfo and /uploadFile.
The critical finding: the /allinfo endpoint accepts a campaign ID parameter and returns all victim records for that campaign — without any authentication. No session token, no API key, no IP allowlist. A GET request with a valid campaign ID returns everything.
This is the gap between the front-end and the back-end. The victim-facing infrastructure is hardened to a degree Red Asgard has never observed from an APT — zero vulnerabilities across 11 attack classes. But the operator infrastructure behind it has the kind of IDOR vulnerability seen in routine penetration tests. The researchers suggest either separate teams with different security standards, or deliberate prioritization that hardened everything victim-facing while treating the operator panel as internal-only.
Operator Account Discovery
Through enumeration of the /info and /adc endpoints, Red Asgard identified six operator accounts: 55, 98, 15, 16, yjs, and Eric. The non-numeric identifiers yjs and Eric suggest personal handles rather than system-generated accounts. The /dumpsql endpoint confirmed account validity — UID 15 returned "No permission" while unknown UIDs returned a TypeError leaking the authorization model: a boolean is_admin field.
Six operators. 857 victims. 241,764 credentials.
Cracking the Binary Protocol
The binary protocol on ports 22411-22413 had been opaque since Part I of the investigation. In their final wave, Red Asgard cracked it.
The encryption is layered but not complex: UTF-16LE encoding with XOR key 0x47 on port 22411. The key 0x47 is the ASCII value of G — the first byte of G01d*8@(, the XOR key recovered from BeaverTail. The operators derive per-port keys from a master key family: 0xcb (203) for port 22412 (the original binary protocol key), 0x47 (71) for port 22411, 0x8c (140) for port 22413 (derived via 0x47 XOR 0xcb), and 0x5A (90) for OtterCookie screenshot encryption.
This deterministic derivation means recovering any single key from the family potentially compromises the others.
Decrypted output from port 22411 revealed 6,208 lines of operator beacon data spanning January 29 through February 3, 2026. Two processes alternate every approximately 10 minutes — WINSTART.exe (PID 9999) and WINEXIT.exe (PID 8888) — with hardcoded PIDs indicating automated C2 beacon scheduling rather than dynamic OS assignment. The beacons reference Z:\ drive paths consistent with network-mounted operational data storage.
The 6-day span of continuous beacon data confirms the infrastructure is actively managed as of publication.
MITRE ATT&CK Mapping
OtterCookie-Specific
T1056.001 — Input Capture: Keylogging GlobalKeyboardListener, exfil to /clip
T1113 — Screen Capture captureAllMonitors(), 5-second interval
T1115 — Clipboard Data /clip endpoint, continuous exfiltration
T1555.003 — Credentials from Web Browsers 27 wallet extensions, vault data
T1528 — Steal Application Access Token Wallet seed phrases, IndexedDB
T1020 — Automated Exfiltration Continuous upload to /total
T1059.007 — JavaScript Node.js RAT
T1547.001 — Registry Run Keys / Startup Folder "NodeHelper"
T1053.005 — Scheduled Task "NodeUpdate", logon trigger
T1497 — Virtualization/Sandbox Evasion VMware, VirtualBox, QEMU, KVM, Xen, Parallels, Bochs
T1027 — Obfuscated Files or Information XOR 0x5A (screenshots)
T1102.001 — Dead Drop Resolver tetrismic.vercel.app
AnyDesk RAT
T1219 — Remote Access Software AnyDesk deployment and backdoor
T1098 — Account Manipulation Injecting attacker credentials into AnyDesk config
T1005 — Data from Local System Full browser credential extraction
T1560 — Archive Collected Data Victim data packaged via /downloadFile
T1552.001 — Unsecured Credentials Plaintext passwords on unauthenticated endpoints
Campaign-Wide (All Parts)
T1566.003 — Phishing via Service — Part I (Upwork, Fiverr) T1204.002 — Malicious File — Part I (VSCode tasks) T1027.002 — Software Packing — Part I (64-layer obfuscation) T1102.001 — Dead Drop Resolver — Parts I-III (Pastebin → Polygon → Vercel) T1573.001 — Symmetric Encryption — Part I (XOR keys) T1573.002 — Asymmetric Encryption — Part I (RSA-PSS) T1496 — Resource Hijacking — Part I (XMRig)
Indicators of Compromise
C2 IP Addresses
Operator Infrastructure:
146.70.253.107 (port 1224) — Primary operator C2, ACTIVE
95.164.17.24 (port 1224) — AnyDesk RAT C2, ACTIVEBeaverTail Victim C2s:
147.124.213.232 (port 1244)
147.124.212.125 (port 1244)
147.124.214.129 (port 1244)
66.235.168.238 (ports 1244, 22411-22413)
45.59.163.55 (port 1244)
216.250.251.87 (port 1247)
87.236.177.9 (port 3000)OtterCookie Victim C2s:
172.86.105.40 (port 5918)
172.86.116.178 (port 5918)
86.106.85.234 (port 4558)
144.172.104.117 (port 5918)
144.172.101.45 (port 1224)Netblock of Interest: 147.124.208.0/20 (AS396073, Majestic Hosting / SpinServers, Carrollton TX)
Domains
- tetrismic.vercel.app — OtterCookie delivery — ACTIVE
- codeviewer-three.vercel.app — BeaverTail delivery — Active
- elvengold.com — Lure domain — Active
- email.tokenloopz.com — Lure domain — Active
- jerryfox-platform.vercel.app — Unknown — Taken down (451)
- brantwork.vercel.app — BeaverTail — Taken down (451)
- task-hrec.vercel.app — BeaverTail — Taken down (451)
- kb102531x.vercel.app — BeaverTail — Taken down (451)
Campaign Identifiers
- 5346 — Multi-family — Primary campaign (121 victims)
- 15 / team15 / dGVhbTE1 — Multi-family — Secondary campaign (287 victims)
- 99 — Credential stealer — Largest campaign (449 victims)
- hkMrMq7 — BeaverTail + AnyDesk — Majestic Hosting campaign
- kmHgMq7 — BeaverTail — Secondary token
- env08539 — BeaverTail — EuroHoster campaign
- 31df390f0305 — BeaverTail — Vercel campaign
XOR Key Family
- G01d*8@( — BeaverTail file encryption
- 0x47 — Binary protocol, port 22411
- 0xcb — Binary protocol, port 22412
- 0x8c — Binary protocol, port 22413
- 0x5A — OtterCookie screenshot encryption
- Vw1aGYoP — Base85 layer decryption
- Xt3rqfmL — Payl module encryption
- Ze4pq4iT — MetaMask injector encryption
AnyDesk Backdoor Credentials
pwd_hash: 967adedce518105664c46e21fd4edb02270506a307ea7242fa78c1cf80baec9d
pwd_salt: 351535afd2d98b9a3a0e14905a60a345
token_salt: e43673a2a77ed68fa6e8074167350f8fString IOCs
# OtterCookie
GlobalKeyboardListener
node-screenshots
NodeHelper
NodeUpdate
module-listener
captureAllMonitors
# BeaverTail
TSUNAMI_INJECTOR
TSUNAMI_PAYLOAD
!!!HappyPenguin1950!!!
Windows Update Script.pyw
G01d*8@(Port Configuration Signature
Any host presenting ALL of the following ports simultaneously is likely Contagious Interview infrastructure:
1224/tcp AND 1244/tcp AND 5918/tcp AND 5934/tcp AND 5961/tcp AND 5974/tcpAdditional confirming ports: 21, 80, 443, 3389, 5985, 8000, 54321
Recommendations
Immediate Actions for Developers
If you have participated in a coding interview involving a GitHub repository from an unknown party in the last 18 months:
- Check browser saved passwords for entries to
elvengold.com,tokenloopz.com, or any domain from a "job interview" — if present, assume compromise - Rotate ALL saved browser passwords immediately — start with banking and cryptocurrency
- Check for AnyDesk — if installed and you did not install it, remove it and audit
service.conffor the credential hashes listed above - Search for OtterCookie persistence: registry key "NodeHelper" and scheduled task "NodeUpdate"
- Enable 2FA on every account — hardware keys are ideal, SMS is better than nothing
Network Detection
# Block all confirmed C2 IPs (full list above)
# Alert on connections to port 1224 (non-standard HTTP)
# Alert on connections to ports 22411-22413 (binary protocol)
# Alert on the 13-port configuration signature
# Monitor connections to *.vercel.app from backend server processes
# Block tetrismic.vercel.app specificallyHost Detection
powershell
# AnyDesk backdoor detection
$adConfig = Get-Content "$env:ProgramData\AnyDesk\service.conf" -ErrorAction SilentlyContinue
if ($adConfig -match "967adedce518105664c46e21fd4edb02270506a307ea7242fa78c1cf80baec9d") {
Write-Warning "COMPROMISED: AnyDesk config contains Lazarus backdoor credentials"
}
# OtterCookie persistence
Get-ItemProperty "HKCU:\Software\Microsoft\Windows\CurrentVersion\Run" |
Where-Object { $_.NodeHelper -like "*node*" }
Get-ScheduledTask | Where-Object {
$_.TaskName -like "*NodeUpdate*" -or
$_.Actions.Execute -like "*node*"
}
# Keylogger module detection
Get-Process node -ErrorAction SilentlyContinue |
Where-Object { $_.Modules.ModuleName -contains "module-listener" }Organizational Mitigations
For organizations hiring remote developers through freelancing platforms:
- Implement mandatory repository vetting before any code is opened
- Disable VSCode auto-execution of tasks
- Review
package.jsonscripts before runningnpm install - Isolate contractor development environments from production credentials
- Use hardware wallets for any cryptocurrency holdings over trivial amounts
- Separate browser profiles for cryptocurrency activity
- Enable extension whitelisting via Chrome enterprise policies
Detection Content
Red Asgard produced 16 YARA rules and 88 Snort rules covering C2 beacon traffic, binary protocol handshakes, credential exfiltration patterns, AnyDesk backdoor deployment, operator panel access, lure domain resolution, XOR-encrypted data patterns, and campaign token patterns. Full rule packages are available to law enforcement and vetted threat intelligence partners via Red Asgard (contact@redasgard.com).



