Instagram Vulnerability Exposed Private Photos Without Authentication, Meta Silently Patched and Denied Report

A server-side vulnerability in Instagram allowed unauthenticated attackers to access private photos and captions without logging in or having a follower relationship, according to security researcher Jatin Banga who published a full disclosure this week after a 102-day interaction with Meta's bug bounty program.
Meta silently patched the vulnerability within 48 hours of receiving vulnerable test accounts, then closed the report as "Not Applicable" claiming they were unable to reproduce the issue they had just fixed.
Discovery During Automation Tool Development
Banga discovered the vulnerability while building a workflow automation tool for HTTP requests. While examining Instagram's mobile web responses, he noticed CDN links being returned for content that should not have been accessible—private posts, full resolution images, and captions all embedded in HTML responses to unauthenticated requests.
Initial testing on his own private account confirmed the issue was not a caching artifact. After creating a post, waiting several hours, and running an unauthenticated request, the private content was fully accessible via the returned CDN links.
Video from Jatin Banga
Authorization Bypass Through Mobile Headers
The vulnerability exploited a failure in Instagram's server-side authorization logic. By sending an unauthenticated GET request to instagram.com/<private_username> with specific mobile user-agent headers, attackers could trigger a response containing the polaris_timeline_connection JSON object populated with private content.
Under normal circumstances, this object should return empty for private accounts viewed by non-followers. However, for affected accounts, the server returned a full edges array containing direct CDN links to private media and their associated captions.
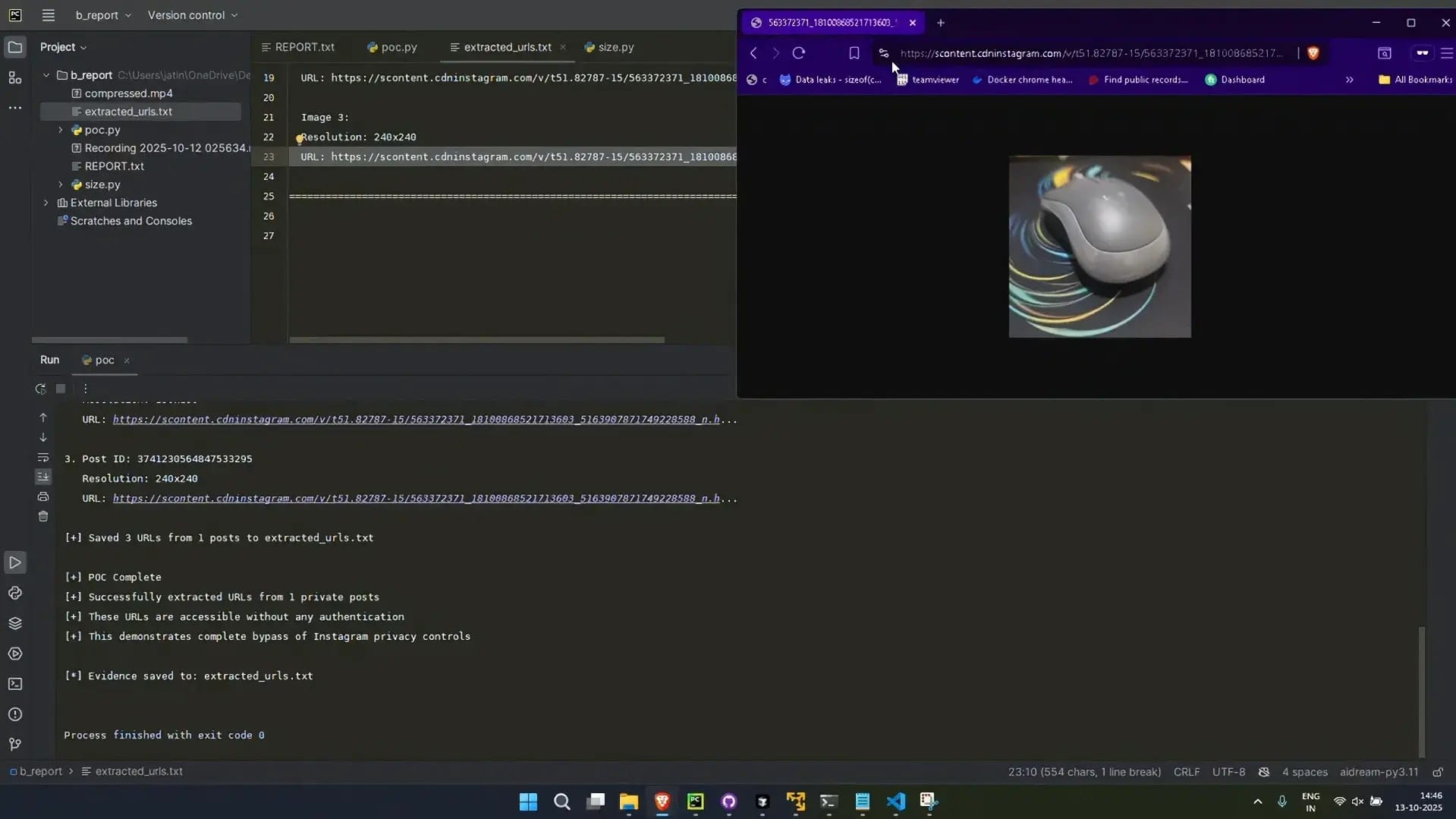
The attack workflow involved four steps. First, the attacker sends a header-manipulated GET request to a private profile. The server returns HTML with embedded JSON data. The attacker then parses the polaris_timeline_connection object to locate the edges array. Finally, high-resolution images and post details are accessed directly via the exposed CDN URLs.
Banga emphasized this was not a caching issue. The server was actively generating private data for unauthorized requests, indicating a fundamental authorization check was missing from the response pipeline.
Conditional Bug Affected Subset of Accounts
The vulnerability did not affect every private account. In authorized testing across seven accounts that Banga owned or had explicit permission to test, approximately 28 percent were vulnerable while others returned secure responses. Because he accidentally discovered the bug on a non-authorized account before formal testing began, the researcher noted the true vulnerability rate is likely higher.
Initial analysis suggested a correlation with account age, but the root cause was never determined. Banga observed that affected requests returned anomalous metadata showing zero followers and zero following despite the accounts having active follower counts, suggesting a corrupted session state triggered the exposure.
102-Day Bug Bounty Timeline
Banga submitted the initial report to Meta on October 12, 2025, including a proof-of-concept Python script, full technical explanation, and video demonstration. Meta quickly closed the first report, misinterpreting it as a CDN caching issue under Case Number 1838087146916736.
Banga immediately filed a second report under Case Number 1838100803582037 with clearer language emphasizing this was a server-side authorization failure. This time Meta engaged.
On October 13, Meta requested testing on their own account called 2fa_2fa. The exploit did not work on this account, providing an early indication that the bug was conditional. On October 14, Meta requested another vulnerable account. Banga provided one with the owner's consent, its_prathambanga, where the exploit successfully reproduced. He submitted video evidence of both manual browser reproduction and automated script extraction.
On October 15, Banga sent a detailed analysis explaining the two-part behavior. Specific headers trigger a state where the server returns zero followers and zero following, and in that corrupted state, the private timeline data is incorrectly populated for some accounts.
Silent Patch Deployed Without Notification
On October 16, 2025, the exploit stopped working. Every account that had previously returned private data now returned empty responses. Meta had deployed a server-side patch without any notification to the researcher.
Banga sent a follow-up asking for confirmation that the vulnerability was fixed. He received no response.
Eleven days later on October 27, Meta officially responded stating they were "unable to reproduce this issue" and closed the case as "Not Applicable" with no acknowledgment of the vulnerability.
When Banga challenged the contradiction—pointing out that Meta had requested vulnerable accounts, received them with video proof of successful exploitation, and then those exact accounts were patched—Meta's security team responded that "the fact that an unreproducible issue was fixed doesn't change the fact that it was not reproducible at the time."
Meta added that "even if the issue were reproducible, it's possible that a change was made to fix a different issue and this issue was fixed as an unintended side effect."
No Root Cause Analysis Provided
The closure has drawn criticism for lacking any root cause analysis. Banga offered to provide full network logs with X-FB-Debug headers for internal tracing, but received no response. He also provided a comparative list showing which accounts were exploitable and which were not, creating a ready-made diagnostic dataset for understanding the conditional nature of the bug. Meta did not follow up on either offer.
Without acknowledging the specific flaw or its cause, it remains unclear whether the underlying authorization failure was permanently resolved or merely obscured by configuration changes.
Comprehensive Evidence Published for Peer Review
Banga released complete technical documentation on GitHub including the proof-of-concept Python script that extracted private CDN links, before and after screenshots showing the polaris_timeline_connection object populated with private data versus returning an empty edges array after the patch, four timestamped video recordings with SHA256 hashes and historical git commit history, a complete PDF archive of all Meta correspondence, and network logs with samples showing where the exploit worked, where it did not work, and the CDN links that were exposed.
All evidence was committed to Git during the original reporting process. The timestamps cannot be fabricated retroactively, according to the researcher.
Researcher Questions Meta's Response
Banga stated he does not know whether Meta's handling represents a cover-up or negligence, but noted both explanations are concerning given that Instagram serves over a billion users who rely on private meaning private.
"A conditional bug that exposes some accounts but not others is arguably more dangerous than one that affects everyone," Banga wrote. "It's harder to detect, harder to diagnose, and harder to confirm as fixed. Dismissing it with 'infrastructure changes' doesn't inspire confidence."
The standard coordinated disclosure window is 90 days. Banga gave Meta 102 days and multiple escalation attempts before publishing. While the exploit stopped working on all accounts tested, without root cause analysis from Meta there is no confirmation the underlying issue is truly resolved.
The researcher is inviting independent security researchers to review the technical analysis, timelines, and artifacts to assess whether the described behavior was possible at the time of testing. Meta has not publicly commented on the disclosure.



