IntelBroker Unmasked: Notorious Hacker Revealed as 25-Year-Old Former UK Crime Agency Trainee

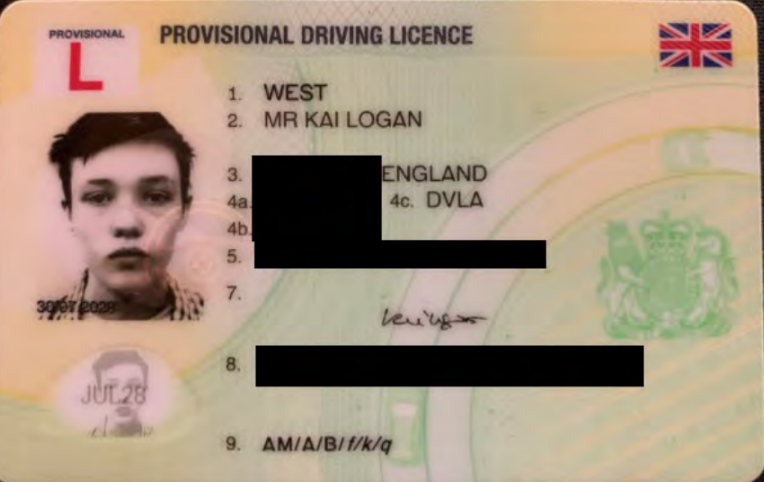
The identity behind one of the most prolific cybercriminal personas of recent years has been revealed. IntelBroker, the hacker who haunted major corporations and government agencies, is Kai Logan West - a 25-year-old British national and former National Crime Agency trainee.
West was arrested in France in February 2025 and charged in June 2025, allegedly causing over $25 million in damages worldwide.
Who Is Kai Logan West?
For years, IntelBroker claimed to be Serbian and living in Russia. In reality, he was a young man from England who had previously worked as a trainee at the UK's National Crime Agency - the British equivalent of the FBI.
Online, he operated under aliases including "IntelBroker" and "Kyle Northern."
Criminal Operations
West's activities spanned multiple fronts:
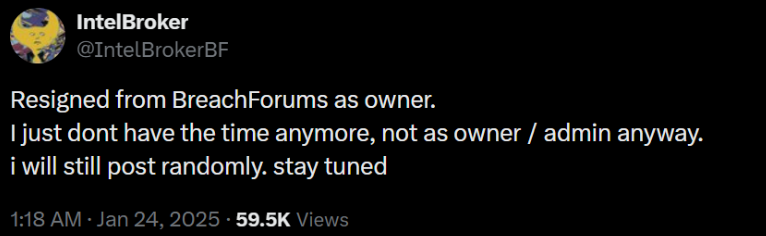
BreachForums Ownership: He became owner of the notorious cybercrime marketplace from August 2024 to January 2025, before resigning citing lack of time.
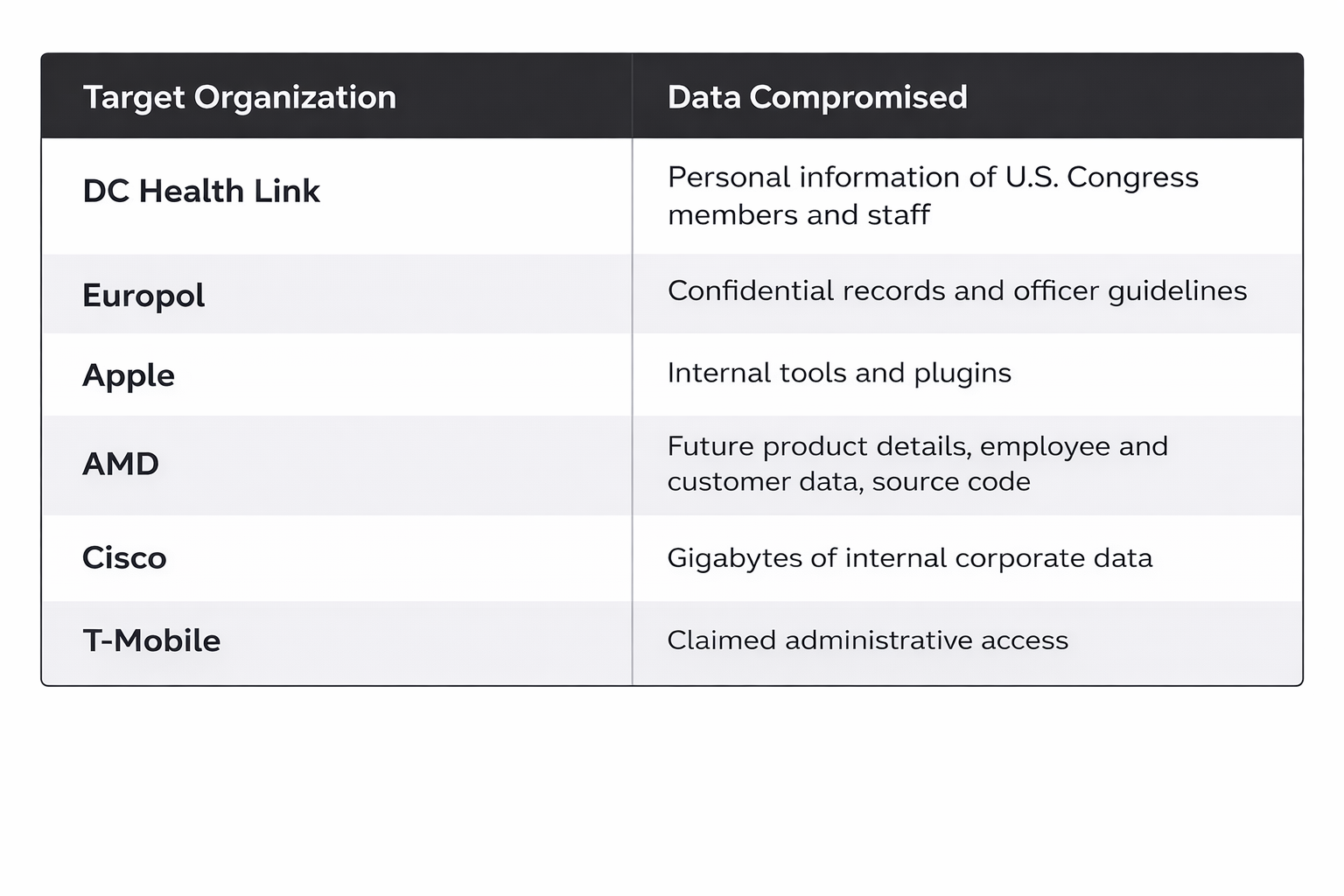
Data Theft: Between 2023 and 2025, he posted over 150 threads selling stolen data or leaking it to build reputation.
Hacking Collective: He coordinated attacks through a group targeting telecommunications firms and healthcare providers.
Endurance Malware: West developed a C# wiper malware called "Endurance" used against U.S. government agencies. Unlike ransomware, it permanently deleted files rather than encrypting them.
High-Profile Targets
How He Got Caught
Despite his sophisticated operations, West made critical mistakes:
- Bitcoin trap: In January 2023, an undercover officer convinced him to accept Bitcoin instead of Monero. Bitcoin transactions are publicly traceable.
- IP address reuse: He used the same internet connection for hacking activities and personal browsing.
- YouTube crossover: His personal IP watched specific YouTube videos that "IntelBroker" then posted on hacking forums.
These operational security failures gave investigators the thread they needed.
Cryptocurrency Preference
West typically demanded payment in Monero for its privacy features that obscure transaction details. His one-time acceptance of Bitcoin proved to be his downfall.



