Interlock Ransomware Deploys Zero-Day Anti-Cheat Driver Exploit to Kill EDR Processes
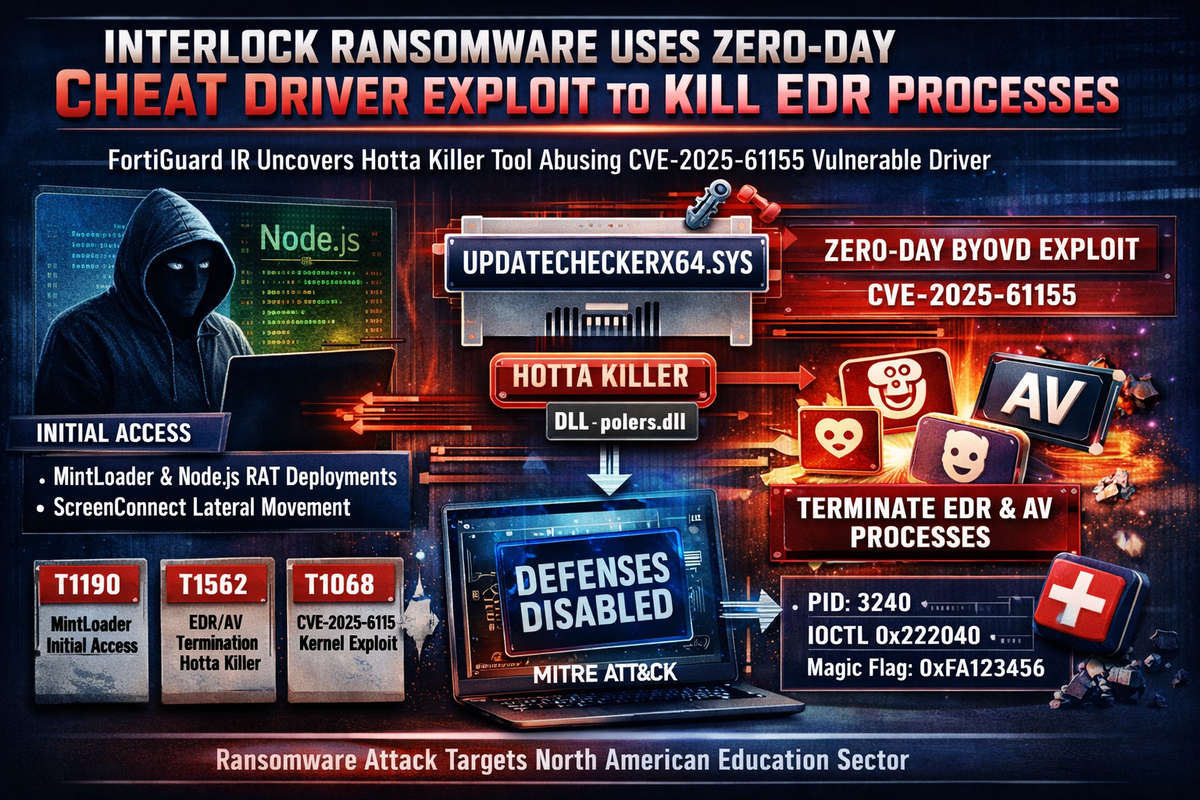
FortiGuard Incident Response has documented a new tool in Interlock ransomware's arsenal — a bring-your-own-vulnerable-driver (BYOVD) process killer that abuses a zero-day vulnerability in a gaming anti-cheat kernel driver to terminate EDR and AV processes before ransomware deployment.
The activity was observed during an intrusion against a North American education organization and represents a continued evolution in Interlock's internally developed tooling. Unlike many ransomware operations that rely on ransomware-as-a-service ecosystems, Interlock develops and maintains its own tools.
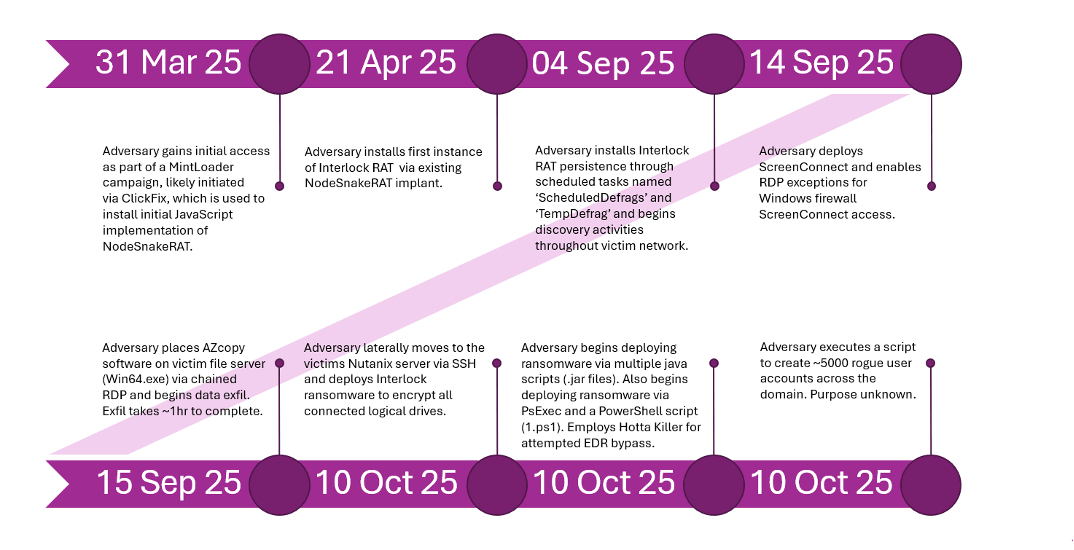
Initial Access and Persistence
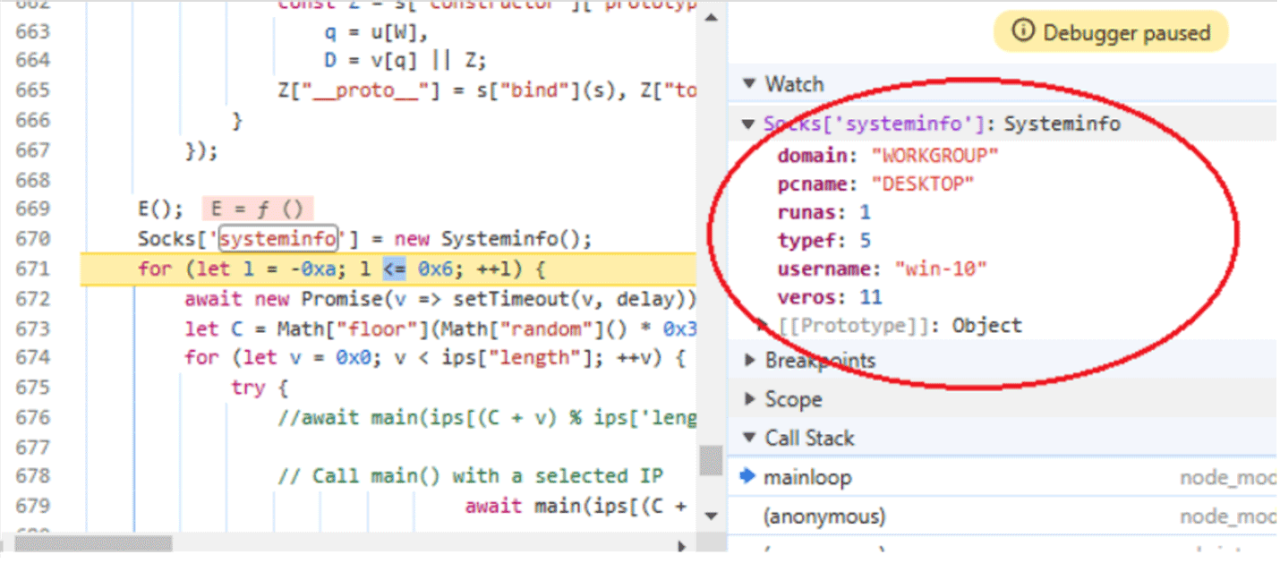
Initial access was tied to MintLoader activity on an end-user system, followed by delivery of a legitimate Node.js runtime used to execute malicious JavaScript implants. The JavaScript stages align with previous reporting on NodeSnakeRAT and Interlock RAT, which provided persistence, discovery, SOCKS5 proxy capability, and remote command execution.
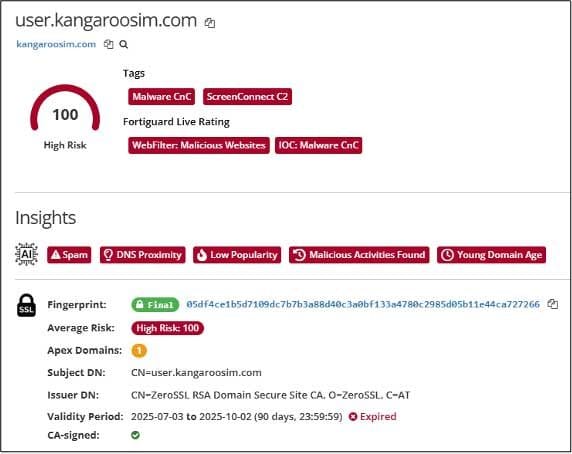
The operators also deployed ScreenConnect for GUI-based access and used standard administrative tradecraft — RDP and firewall allow rules — to move laterally through the environment.
The BYOVD Tool: Hotta Killer
The standout development is a DLL dubbed "Hotta Killer" by FortiGuard IR (observed as polers.dll). The tool drops and installs a signed x64 kernel driver named UpdateCheckerX64.sys — a renamed version of GameDriverx64.sys, an anti-cheat driver vulnerable to CVE-2025-61155.
The kill chain works as follows. The payload first collects system information via PowerShell's systeminfo command. It then creates a demand-start kernel driver service using standard Windows APIs (OpenSCManagerW, CreateServiceW, StartServiceW), registering the vulnerable driver as a kernel service rather than a user-mode program.
Once loaded, the tool parses a command-line keyword (for example "Forti"), converts it into a target pattern (such as Forti.exe), enumerates running processes, and extracts the PID of a match. It then passes the PID to the driver via a device interface using DeviceIoControl, where the driver validates an IOCTL code (0x222040) and a magic flag (0xFA123456) before calling ZwTerminateProcess to kill the targeted process.
The operators attempted to keep the killer running in a looped execution pattern — a watchdog-like approach aimed at continuously suppressing security tooling during later ransomware stages.
Impact and Limitations
FortiGuard notes that the tool is best described as an elevated process killer rather than a complete EDR bypass. In this specific incident, it did not fully disrupt the targeted Fortinet software's operation. However, the technique matters — anti-cheat drivers have a growing history of being repurposed by ransomware actors to gain kernel-level leverage over defensive processes.
Detection Guidance
Defenders should hunt for unexpected kernel driver installations, particularly new .sys files registered as services. Suspicious service creation tied to unsigned or repurposed drivers, BYOVD telemetry matching defense-evasion patterns during hands-on-keyboard activity, and looped process termination attempts targeting security product executables are all strong indicators.
Monitor for DeviceIoControl calls with IOCTL 0x222040 and the magic flag 0xFA123456 as specific signatures of this tool.
MITRE ATT&CK
- T1190 — Exploit Public-Facing Application (MintLoader initial access)
- T1059.007 — Command and Scripting Interpreter: JavaScript (NodeSnakeRAT/Interlock RAT)
- T1219 — Remote Access Software (ScreenConnect)
- T1021.001 — Remote Services: RDP (lateral movement)
- T1562.001 — Impair Defenses: Disable or Modify Tools (Hotta Killer EDR termination)
- T1068 — Exploitation for Privilege Escalation (CVE-2025-61155 kernel driver)
- T1543.003 — Create or Modify System Process: Windows Service (driver service creation)
- T1057 — Process Discovery (process enumeration for PID extraction)



