Kimwolf IoT Botnet Disrupts I2P Anonymity Network in Massive Sybil Attack

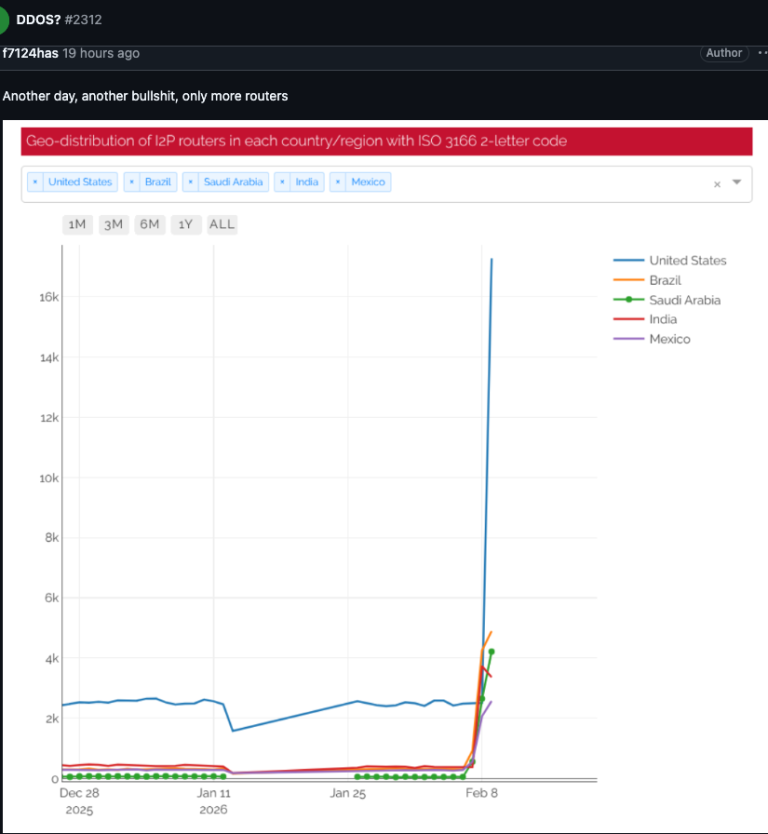
The massive IoT botnet known as Kimwolf has spent the past week disrupting the Invisible Internet Project (I2P), a decentralized anonymity network, after its operators attempted to join approximately 700,000 infected devices as nodes on the network. The incident represents one of the largest Sybil attacks ever observed against a privacy-focused communications infrastructure.
Accidental Takedown
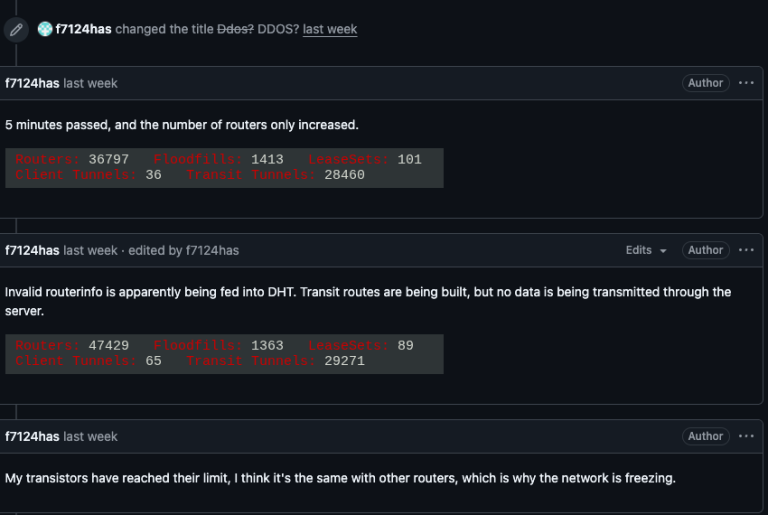
I2P users began reporting disruptions on February 3, with tens of thousands of new routers suddenly overwhelming the network and preventing legitimate users from connecting. One user reported their physical router freezing when connections exceeded 60,000.
The same day, Kimwolf's operators openly acknowledged in their Discord channel that they had accidentally disrupted I2P while attempting to onboard 700,000 bots as network nodes. The I2P network normally consists of between 15,000 and 20,000 devices on any given day, according to Lance James, founder of cybersecurity consultancy Unit 221B and the original founder of I2P.
The influx was many times the network's total capacity. I2P users reported a rapid increase in new routers that were unable to transmit data, effectively drowning out legitimate traffic in what's known as a Sybil attack — where a single entity disrupts a peer-to-peer network by flooding it with fake, controlled identities.
Seeking Takedown-Resistant C2
The disruption was not intentional. Benjamin Brundage, founder of botnet-tracking startup Synthient and the first to document Kimwolf's spreading techniques, told Krebs on Security that the operators were trying to build command-and-control infrastructure that cannot be easily dismantled.
"I don't think their goal is to take I2P down," Brundage said. "It's more they're looking for an alternative to keep the botnet stable in the face of takedown attempts."
Kimwolf has also been experimenting with the Tor anonymity network as a backup C2 channel, though no widespread Tor disruptions have been reported.
Background
Kimwolf surfaced in late 2025 and quickly infected millions of poorly secured IoT devices — including TV streaming boxes, digital picture frames, and routers — turning them into relays for malicious traffic and large-scale DDoS attacks. The botnet previously caused problems for Cloudflare when it instructed millions of infected devices to use Cloudflare's DNS settings, causing Kimwolf control domains to repeatedly overtake Amazon, Apple, Google, and Microsoft in Cloudflare's public ranking of most-requested websites.
Botnet in Decline
There may be a silver lining. Brundage noted that Kimwolf's operators have recently alienated some of their more competent developers, leading to a mistake that caused the botnet to lose more than 600,000 infected systems.
"It seems like they're just running experiments in production," he said. "But the botnet's numbers are dropping significantly now, and they don't seem to know what they're doing."
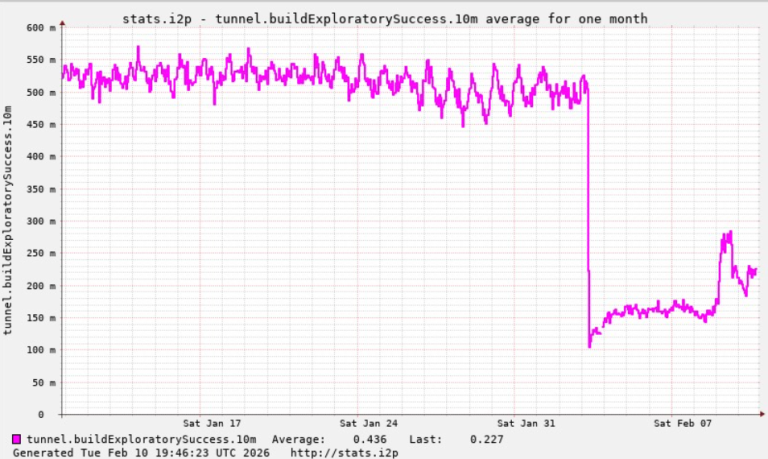
James confirmed that I2P is still operating at roughly half capacity, with a new release rolling out that should bring stability improvements over the coming week.
Recommendation
Organizations should audit IoT device inventories for default credentials and unnecessary network exposure. Monitor for unusual I2P or Tor traffic from internal devices, which may indicate botnet enrollment. Network defenders tracking Kimwolf indicators should note the shift toward anonymity-network-based C2 as a potential evolution in the botnet's infrastructure resilience strategy.



