KONNI Deploys AI-Generated PowerShell Backdoor in Campaign Targeting Blockchain Developers
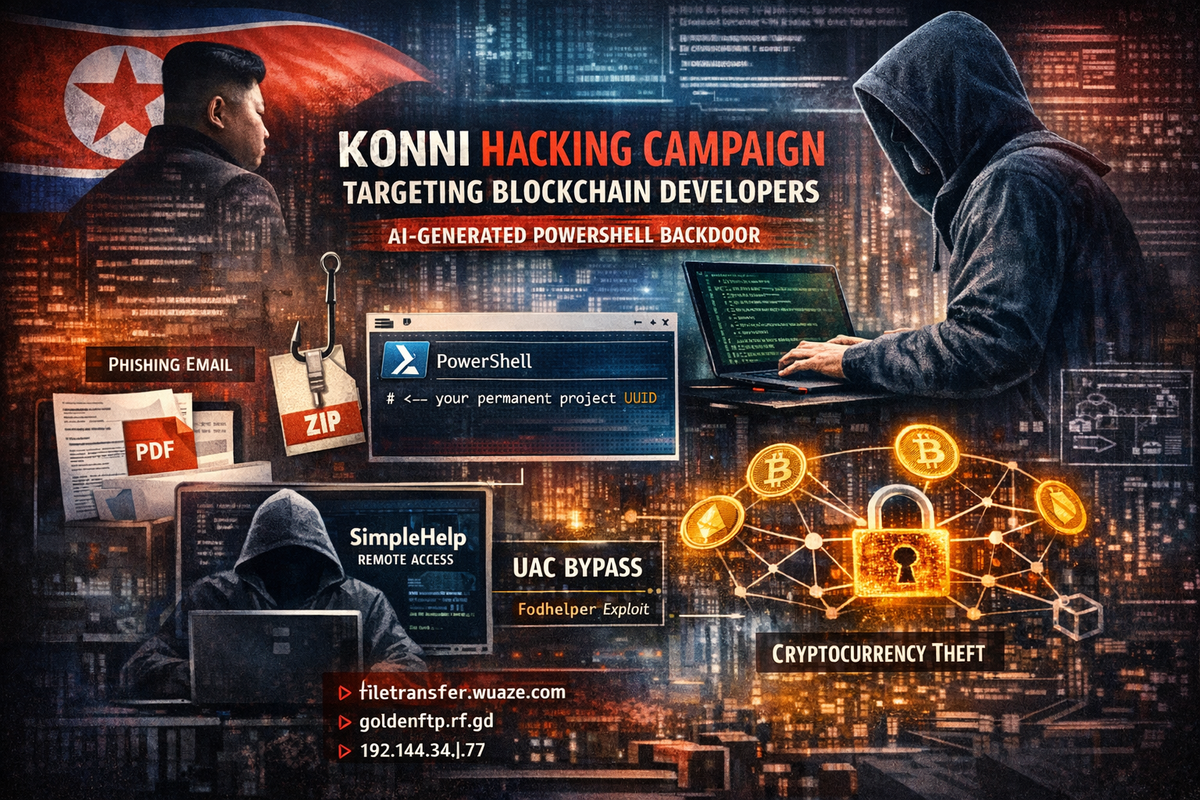
North Korean-linked threat actor KONNI is deploying an AI-generated PowerShell backdoor in an ongoing phishing campaign targeting software developers and engineering teams with access to blockchain infrastructure. The campaign, documented by Check Point Research, marks a notable evolution in both the group's targeting and tooling.
Expanding Beyond Traditional Targets
KONNI has operated since at least 2014, historically focusing on South Korean diplomatic, government, and academic targets. This campaign represents a geographic expansion, with samples uploaded to VirusTotal from Japan, Australia, and India—regions outside the group's typical operating area.
The targeting shift is equally significant. Rather than pursuing geopolitical intelligence, the campaign aims to compromise development environments where attackers could gain access to API credentials, wallet keys, and cryptocurrency holdings.
AI Fingerprints in the Malware
The PowerShell backdoor exhibits clear indicators of AI-assisted development. Check Point researchers identified several telltale signs: unusually polished documentation describing the script's functionality, well-defined modular sections following modern software engineering conventions, and most tellingly, an embedded comment reading # <– your permanent project UUID—phrasing characteristic of LLM-generated code where the model instructs a human user on customizing placeholder values.
Infection Chain
The attack begins with Discord-hosted ZIP archives containing PDF lures disguised as legitimate blockchain project documentation—complete with architecture diagrams, technology stacks, and development timelines. A malicious LNK file launches an embedded PowerShell loader that deploys the backdoor alongside batch files and a UAC bypass executable.
The backdoor implements extensive anti-analysis checks, including hardware threshold validation, monitoring for tools like IDA and Wireshark, and mouse activity tracking. Once satisfied, it establishes persistence via scheduled tasks masquerading as OneDrive processes.
Privilege escalation uses the fodhelper UAC bypass technique, and elevated infections eventually deploy SimpleHelp—a legitimate remote monitoring tool—for long-term interactive access.
Indicators of Compromise
Domains:
filetrasfer.wuaze[.]comgoldenftp.rf[.]gdplaza.xo[.]jegabber.42web[.]io
IPs:
46.4.112[.]56192.144.34[.]77192.144.34[.]40
Source: Check Point Research



