Lazarus Group Poisons npm and PyPI With Fake Recruitment Campaign Deploying Token-Based RAT
The North Korea-linked Lazarus Group has been planting malicious packages across both npm and PyPI repositories through an elaborate fake recruitment campaign targeting developers in the blockchain and cryptocurrency space, deploying a modular remote access trojan with a command-and-control mechanism unique to North Korean operations.
ReversingLabs researchers discovered the campaign, codenamed graphalgo, and assess it has been active since May 2025.
The Social Engineering Pipeline
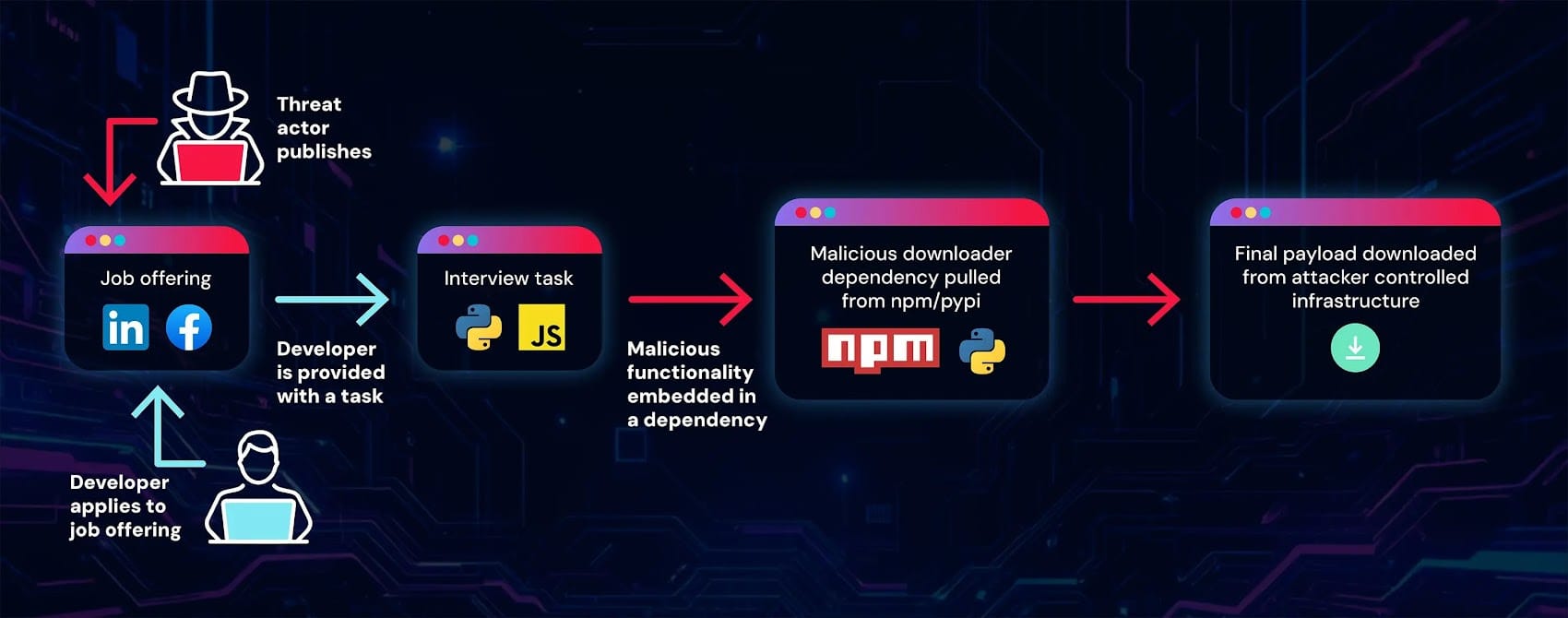
The operation follows the established North Korean playbook of weaponizing job recruitment. Lazarus created a fake blockchain company called Veltrix Capital, complete with a registered domain and GitHub organization hosting repositories for coding assessments in Python and JavaScript.
Developers are approached via LinkedIn, Facebook, and Reddit job listings. Candidates who apply are asked to run coding assessment projects on their machines. The repositories themselves contain no malicious code — the payload is delivered indirectly through dependencies hosted on npm and PyPI.
"The malicious functionality was not introduced directly via the job interview repositories, but indirectly — through dependencies hosted on the npm and PyPI open-source package repositories," explained ReversingLabs researcher Karlo Zanki.
35+ Malicious Packages
The campaign published over 35 packages across both ecosystems. One package, bigmathutils, accumulated over 10,000 downloads after an initial clean version was published before a malicious second version was pushed — a trust-building technique designed to bypass suspicion.
npm packages include graphalgo, graphorithm, graphstruct, graphlibcore, netstruct, graphnetworkx, graphkitx, graphchain, graphflux, graphorbit, graphnet, graphhub, graphrix, bignumx, bignumberx, bignumex, bigmathex, bigmathlib, bigmathutils, graphlink, bigmathix, and graphflowx.
PyPI packages include graphalgo, graphex, graphlibx, graphdict, graphflux, graphnode, graphsync, bigpyx, bignum, bigmathex, bigmathix, and bigmathutils.
Token-Based C2 Mechanism
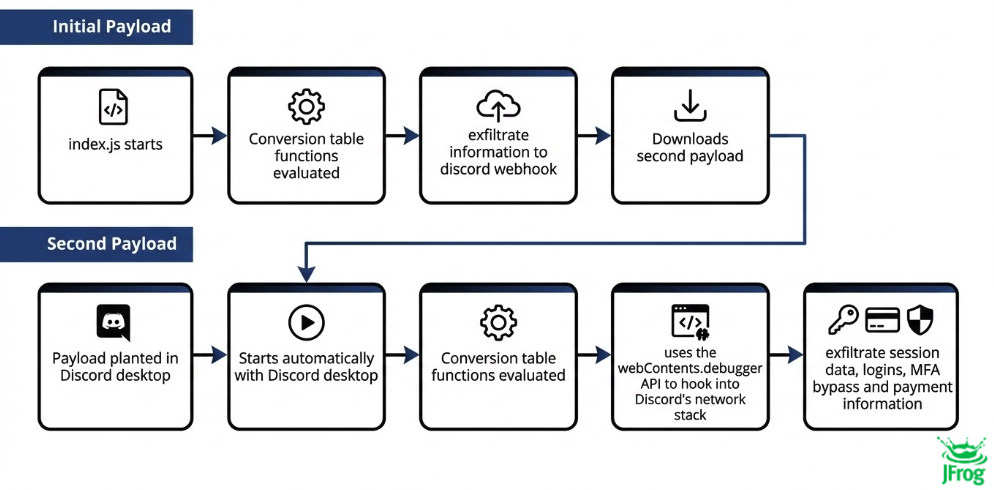
The deployed RAT uses a distinctive token-based authentication system for C2 communication. Infected systems send system data as a registration step, receive a unique token in response, and include that token in all subsequent requests to prove they are registered endpoints.
This mechanism was previously observed in 2023 campaigns linked to Jade Sleet (also tracked as TraderTraitor and UNC4899) and has not been used by any other threat actors in public package repository malware, making it a reliable Lazarus attribution indicator.
The RAT supports commands for system information gathering, file and directory enumeration, process listing, folder creation, file manipulation, and file upload/download. It also checks for the MetaMask browser extension — consistent with Lazarus's focus on cryptocurrency theft.
Recommendation
Developers should treat unsolicited job offers involving coding assessments with extreme caution, particularly in the blockchain and cryptocurrency space. Audit project dependencies before executing any code from recruitment processes. Monitor for the graphalgo and related package names across development environments. Organizations should implement dependency scanning and package allowlisting in CI/CD pipelines. The campaign's sophistication — modular design, trust-building through clean initial versions, and multi-platform targeting — reflects state-sponsored investment in supply chain compromise.



