LockBit 5.0 Deploys Cross-Platform Ransomware Targeting Windows, Linux, and ESXi Simultaneously
LockBit 5.0 has introduced cross-platform ransomware payloads capable of hitting Windows, Linux, and VMware ESXi environments in a single campaign, according to analysis of 19 samples published by LevelBlue.
The release marks a significant technical evolution for the RaaS operation, with specialized routines designed to maximize damage across enterprise virtualization infrastructure — where a single compromised hypervisor can take down dozens of virtual machines simultaneously.
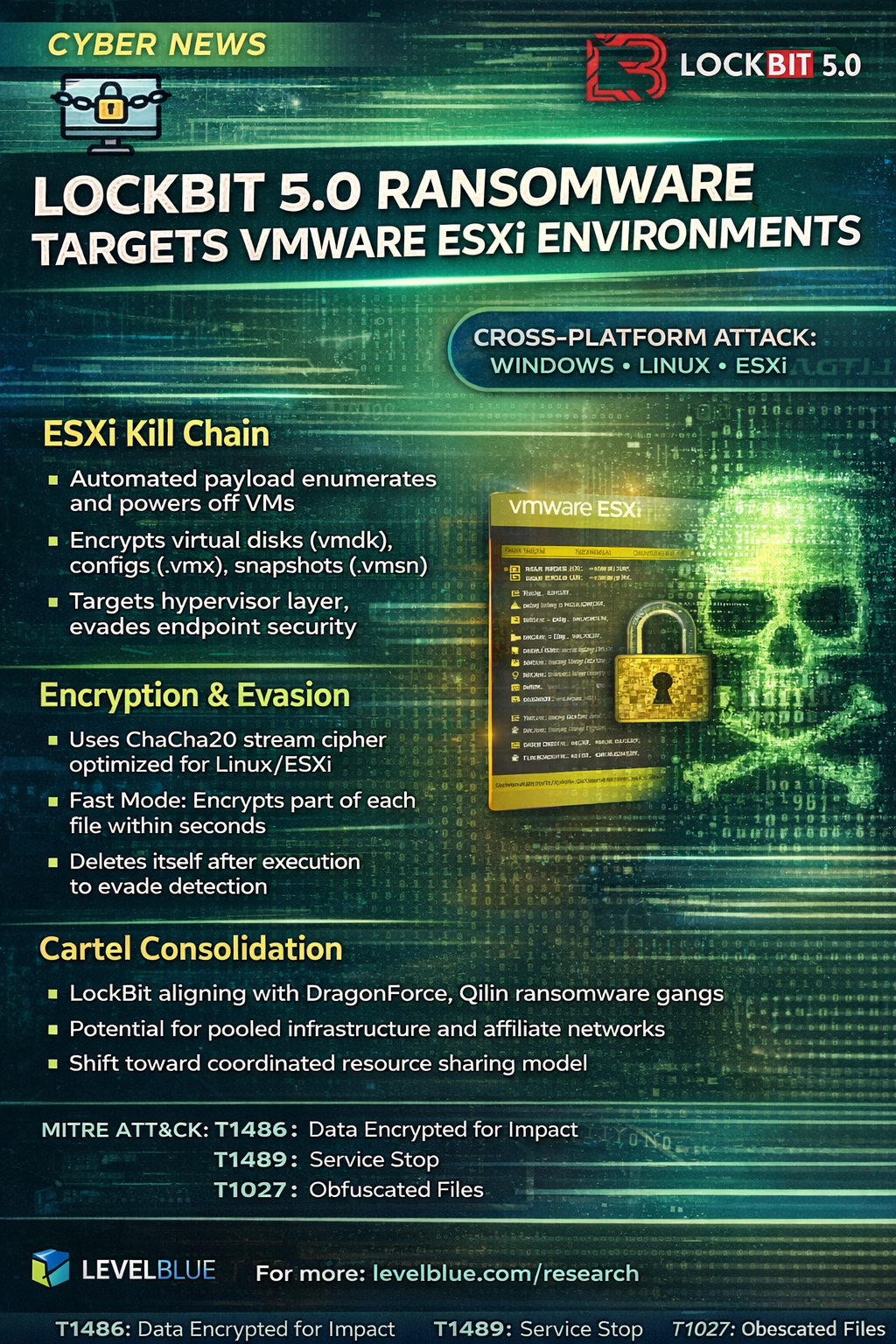
ESXi Kill Chain
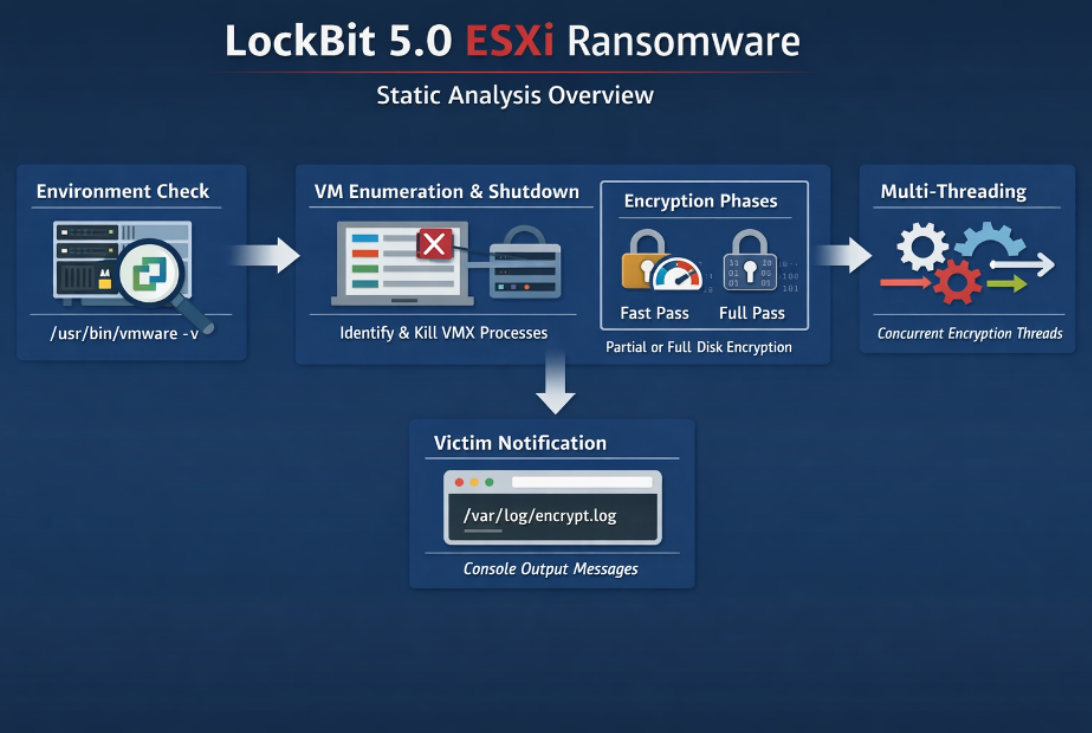
The ESXi variant follows an automated execution flow purpose-built for hypervisor environments. On execution, the payload validates it is running on a legitimate ESXi host via vmware -v, then uses the built-in vim-cmd tool to enumerate all active virtual machines and forcibly power them off. With VMs shut down and disk files unlocked, the ransomware encrypts virtual hard disks (.vmdk), configuration files (.vmx), and snapshot data (.vmsn) — effectively destroying the entire virtualized environment in a single pass.
By targeting the hypervisor layer rather than individual guest operating systems, LockBit 5.0 bypasses endpoint security tools running inside VMs entirely.
Encryption and Evasion
LockBit 5.0 has replaced AES with ChaCha20, a stream cipher optimized for speed on systems without hardware AES acceleration — a common characteristic of Linux and ESXi hosts. The payload also includes a "Fast Mode" that encrypts a small percentage of each file first, rendering data unusable within seconds before completing a full encryption pass.
Detection evasion is aggressive. At time of analysis, only 1 out of 65 security engines on VirusTotal identified the ESXi sample. The malware incorporates anti-analysis checks for debugging tools and deletes itself after execution to minimize forensic artifacts. LevelBlue noted the ESXi payload is labeled internally as "LINUX Locker v1.06," which may indicate a shared codebase with the Linux variant or a version counter oversight by the operator.
Cartel Consolidation
Intelligence suggests LockBit is moving toward a cartel-style consolidation model, potentially aligning with DragonForce and Qilin to pool infrastructure, tooling, and affiliate networks. If confirmed, this would represent a shift from competing RaaS operations toward coordinated resource sharing — increasing the operational capability available to individual affiliates.
Recommendations
Organizations running VMware ESXi should restrict SSH access to hypervisor hosts, monitor for unexpected vim-cmd and esxcli execution, and ensure ESXi patches are current. Network segmentation between management interfaces and production traffic is critical — hypervisor management planes should never be reachable from general user networks. Backup infrastructure should be isolated from environments accessible to ESXi administrators to prevent simultaneous encryption of production and recovery systems.
MITRE ATT&CK: T1486 (Data Encrypted for Impact), T1489 (Service Stop), T1082 (System Information Discovery), T1027 (Obfuscated Files or Information), T1070.004 (Indicator Removal: File Deletion), T1480 (Execution Guardrails)



