LummaStealer Rebounds With CastleLoader Campaigns as ClickFix Infections Surge Globally
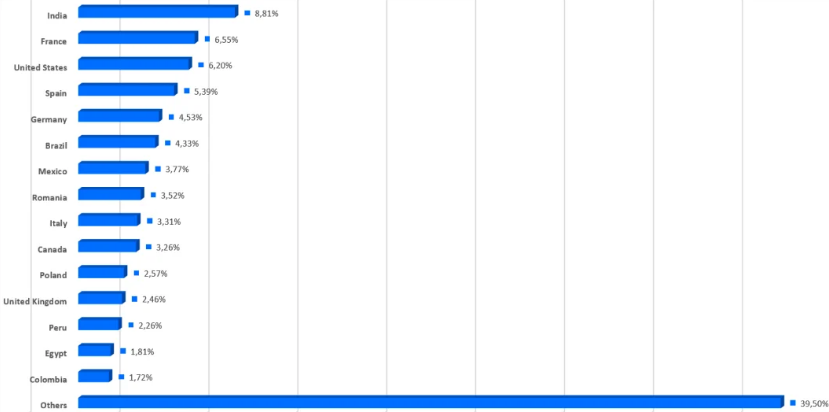
LummaStealer — the prolific infostealer-as-a-service operation that law enforcement disrupted in May 2025 — has staged a significant comeback, with Bitdefender researchers documenting a major surge in infections between December 2025 and January 2026. The resurgence is powered by CastleLoader, a modular malware loader that uses ClickFix social engineering to trick users into executing malicious PowerShell commands.
From Takedown to Rebuild
In May 2025, a coordinated operation by multiple tech firms and law enforcement seized 2,300 domains and dismantled LummaStealer's central command infrastructure. Activity dropped sharply — but by July 2025, the MaaS operation had begun rebuilding. Six months later, Bitdefender warns that LummaStealer is now operating at scale once again.
The infostealer targets browser-stored credentials and cookies, cryptocurrency wallet data, session tokens, authentication cookies, VPN configurations, and sensitive documents — making it one of the most versatile credential theft tools in the cybercriminal ecosystem.
CastleLoader: The New Delivery Engine
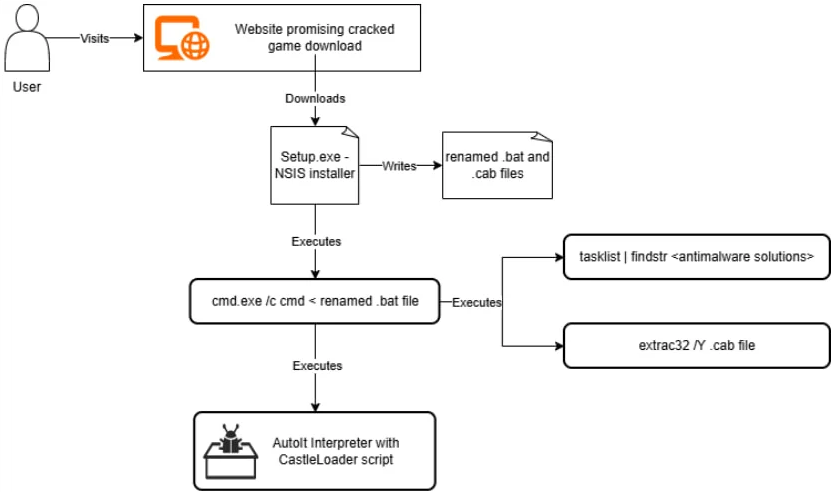
At the center of the resurgence is CastleLoader, a heavily obfuscated script-based loader that first emerged in early 2025 and has since become a key distribution mechanism for multiple malware families including StealC, RedLine, Rhadamanthys, CastleRAT, SectopRAT, NetSupport RAT, and WarmCookie.
CastleLoader executes entirely in-memory, using AutoIT or Python scripts with multiple obfuscation layers — dictionary-based variable renaming, runtime string decoding, junk code injection, and arithmetic operations that resolve to trivial results. Before deploying its payload, it performs environment and sandbox checks and adjusts file paths based on which security products are detected on the host.
For persistence, CastleLoader copies its AutoIT script to a persistence path, places the interpreter in a separate location, and creates an internet shortcut file in the Windows Startup folder that launches the interpreter with the malicious script as an argument.
Bitdefender also identified a detection opportunity: CastleLoader deliberately initiates a failed DNS lookup for a non-existent domain before executing its payload. This artifact can be used by defenders to identify CastleLoader activity in network telemetry.
ClickFix: The Social Engineering Engine
The primary delivery vector is ClickFix — a social engineering technique where users encounter fake CAPTCHA or verification pages with instructions to execute a command that has already been silently copied to their clipboard. Victims open the Windows Run dialog, paste the command, and unknowingly execute a PowerShell script that retrieves CastleLoader from attacker infrastructure, which then fetches and runs LummaStealer in-memory.
Bitdefender describes ClickFix as a "highly effective infection vector" that bypasses browser security features like Google Safe Browsing because the user manually executes the command rather than downloading a file through the browser.
Distribution channels extend beyond ClickFix to include trojanized software installers, pirated software from fake sites and torrents, and fake media or game archives — targeting users globally.
Recommendation
Defenders should monitor for unusual PowerShell execution chains, particularly those initiated from the Windows Run dialog. Hunt for failed DNS lookups to non-existent domains as a potential CastleLoader indicator. Block or restrict PowerShell and cmd.exe access for users who don't require it. Educate users that legitimate websites never ask them to paste commands into a terminal or Run dialog as part of a verification process. Organizations should also consider disabling the Windows Run prompt via Group Policy where operationally feasible.



