MacSync Infostealer Targets macOS Users with Fake Terminal Commands and Trojanized Wallet Apps

A new macOS Malware-as-a-Service operation dubbed MacSync is targeting cryptocurrency users through ClickFix-style social engineering attacks that trick victims into executing a single malicious Terminal command.
The campaign combines credential harvesting, multi-stage payload delivery, and trojanized hardware wallet applications to steal cryptocurrency assets and sensitive system data.
Attack Chain Begins with Fake Microsoft Login
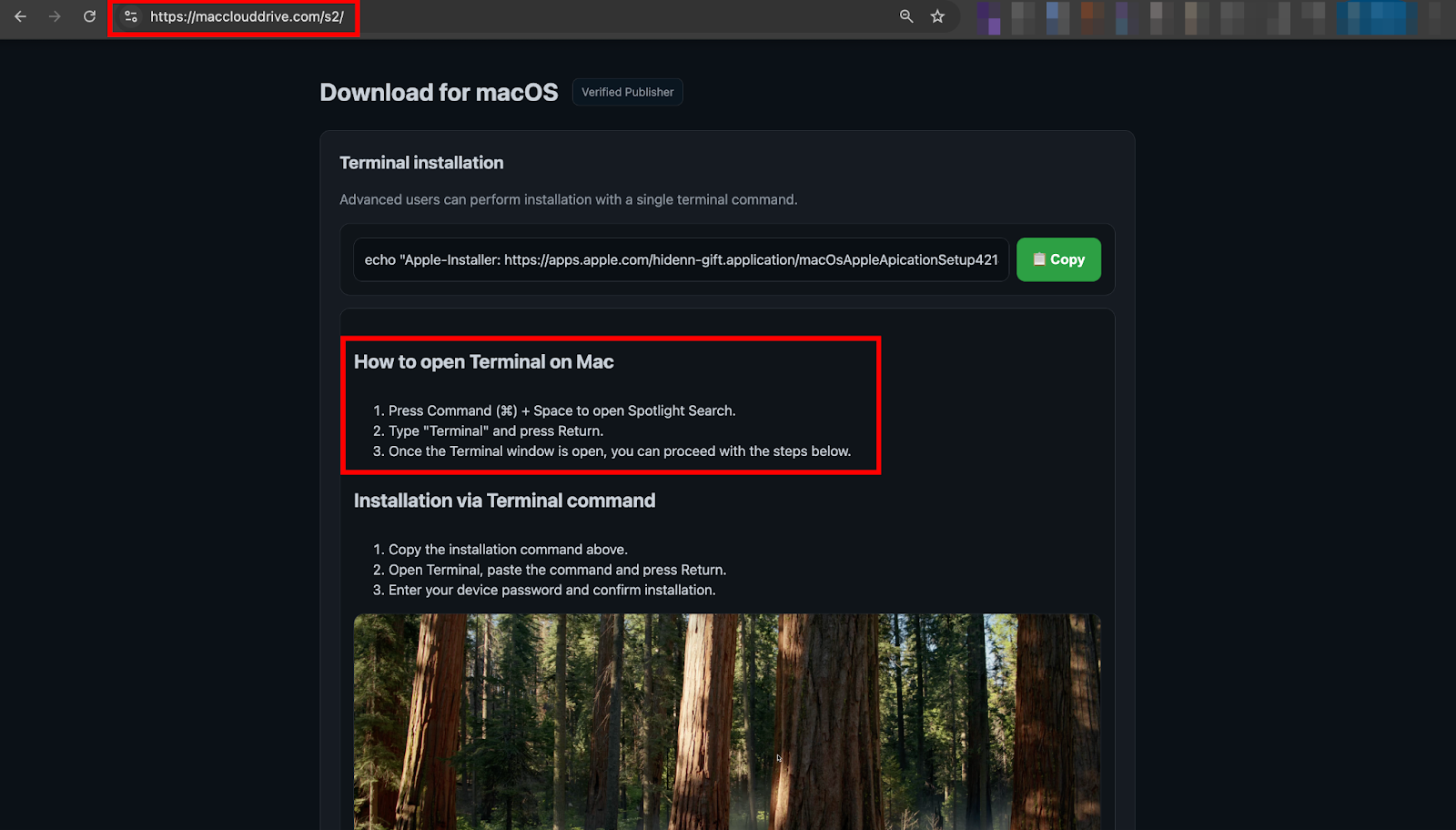
The infection starts with phishing pages impersonating Microsoft authentication. Researchers identified crosoftonline[.]com spoofing legitimate Microsoft login flows, with HTTP redirects leading victims to macclouddrive[.]com—a convincing fake macOS cloud storage installer page.
The lure presents a Terminal command under the guise of "advanced installation," complete with fake App Store branding and a copy button. When executed, the command fetches additional payloads from jmpbowl[.]xyz, initiating the full infection chain.
Multi-Stage Infection Process
The attack unfolds in three stages. The initial Terminal command pipes base64-encoded content directly to Zsh, bypassing macOS Gatekeeper and notarization protections. This downloads a daemonized loader that immediately backgrounds itself, hiding from Terminal visibility.
The second stage fetches an AppleScript payload from dynamic endpoints using unique build tokens for victim tracking. All output redirects to /dev/null for silent execution while maintaining command-and-control connectivity.
The final stage performs systematic data harvesting across multiple categories including browser profiles from Chrome, Brave, Edge, Arc, Vivaldi, Opera, and Yandex. The malware targets over 25 cryptocurrency wallet extensions including MetaMask, Phantom, Binance Wallet, and Coinbase Wallet.
Desktop wallet applications including Exodus, Electrum, Atomic, Wasabi, Bitcoin Core, and Guarda are also targeted, along with complete Keychain databases containing WiFi passwords, application credentials, and SSH keys. AWS credentials, Kubernetes configurations, Telegram session data, and Apple Notes databases are exfiltrated as well.
Fake System Dialogs Harvest Passwords
The malware deploys persistent phishing dialogs mimicking macOS System Preferences to capture the victim's login password. The credential is stored in plaintext and used for offline decryption of encrypted browser data and Keychain contents.
Hardware Wallet Trojanization
MacSync escalates select infections through conditional application trojanization. When Ledger Wallet or Trezor Suite are detected, the malware downloads malicious replacement bundles.
For Ledger, only app.asar and Info.plist files are overwritten while preserving legitimate resources to minimize detection. The modified bundle uses ad-hoc code signing to bypass Gatekeeper validation.
For Trezor Suite, the entire application bundle is replaced. Both variants inject phishing wizards presenting fake error recovery screens followed by PIN and recovery phrase collection forms, capturing credentials under the guise of firmware fixes.
Active Campaign Infrastructure
At least eight rotating command-and-control domains follow consistent naming patterns based on jmpbowl[.]xyz variants. Multiple API paths and five near-identical clone sites indicate ongoing campaign evolution, with unique tokens enabling precise victim tracking and payload customization.
Recommendations
Organizations and individuals should treat unsolicited Terminal commands with extreme suspicion, particularly those presented as installation alternatives. Hardware wallet users should verify application integrity through official sources and monitor for unexpected permission prompts or recovery phrase requests.
The script-based execution chain and absence of traditional binary artifacts complicates endpoint detection, making user awareness the primary defense against this campaign.



