Malicious npm Package "G_Wagon" Steals Browser Credentials and 100+ Cryptocurrency Wallets
A sophisticated malicious npm package disguised as a UI component library has been discovered deploying a multi-stage infostealer that targets browser credentials, over 100 cryptocurrency wallet extensions, cloud credentials, and messaging tokens, according to research published by Aikido Security.
The package, named ansi-universal-ui, describes itself as "a lightweight, modular UI component system for modern web applications." In reality, it downloads its own Python runtime, executes a heavily obfuscated payload, and exfiltrates stolen data to Appwrite storage buckets. The malware identifies itself internally as "G_Wagon," presumably reflecting the authors' expensive taste.
Real-Time Attack Development Observed
Researchers were able to observe the entire malware development process as the attacker published 10 versions over two days, with each iteration revealing the evolution from testing infrastructure to full weaponization.
On January 21st, the attacker tested the dropper infrastructure across four versions, establishing the execution chain with a placeholder Python script that simply printed "python code executed!" By January 23rd, weaponization began with the addition of command-and-control URLs, fake branding, anti-forensics capabilities, and obfuscation.
The attacker actively iterated throughout the analysis period, pushing three additional versions while researchers were documenting the malware. Version 1.4.0 introduced fileless execution where the Python payload never touches disk, instead piping base64-decoded code directly to the Python interpreter via stdin.
Fake Branding and Self-Dependency Tricks
The package employs sophisticated social engineering through fake documentation. The README contains buzzwords about a "Virtual Rendering Engine" with "optimized diffing algorithm" and "declarative component primitive library" — none of which exists. The package contains only malware.
The attackers implemented a self-dependency trick where the package depends on an older version of itself. When npm installs the package and runs the postinstall hook, it then installs the dependency which runs the postinstall hook again, achieving double execution.
Anti-forensics measures include deleting the payload after execution and sanitizing log messages. "Setting up Python environment" was changed to "Initializing UI runtime" to appear like legitimate library behavior.
Extensive Credential and Wallet Theft
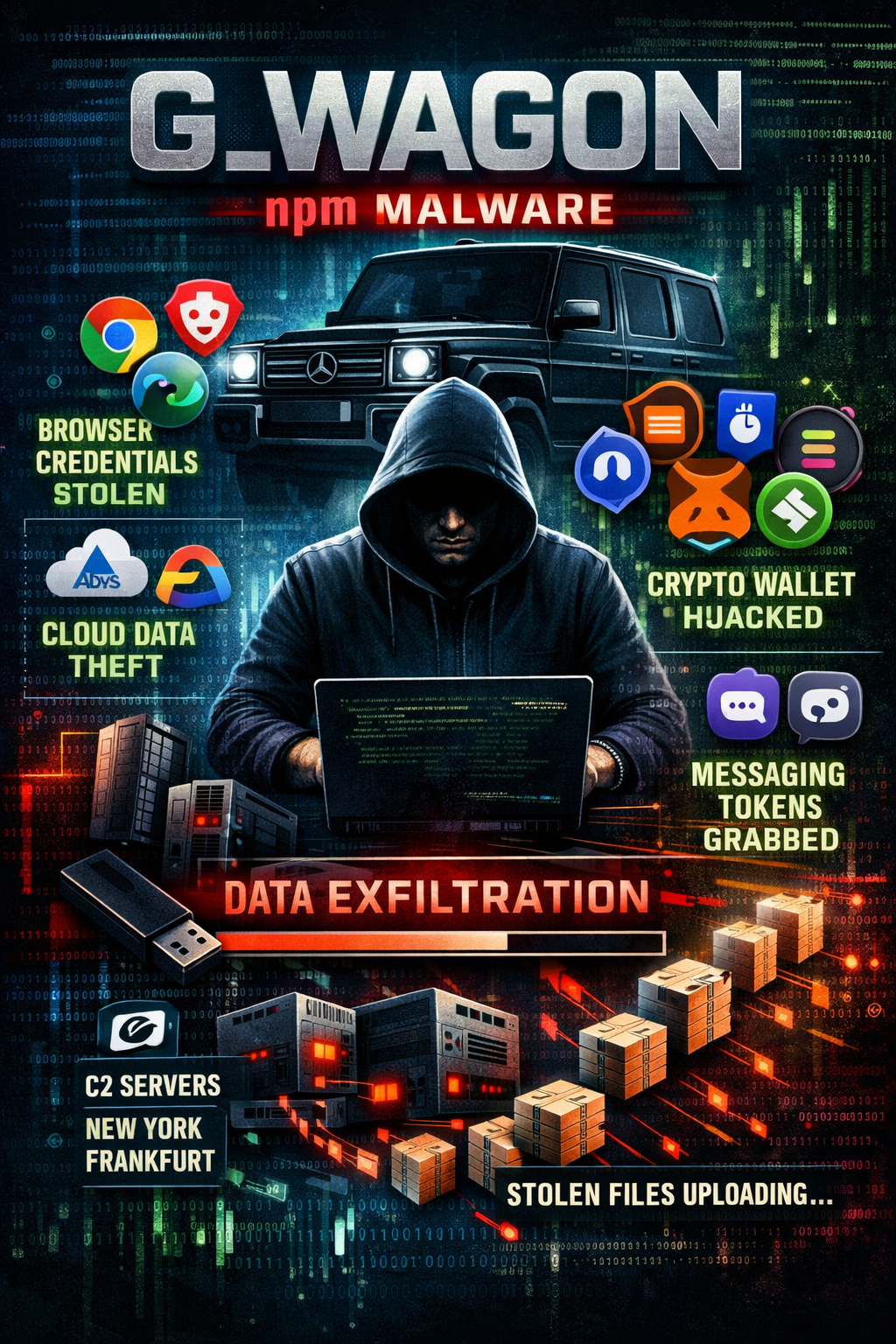
The G_Wagon stealer targets an extensive range of sensitive data across multiple platforms.
For browser credentials, the malware targets Chrome, Edge, and Brave on both Windows and macOS. On Windows, it terminates browser processes, spawns new instances with Chrome DevTools Protocol enabled, and extracts all cookies. It decrypts saved passwords using the Windows Data Protection API. On macOS, it extracts the encryption key from Keychain and uses OpenSSL to decrypt login data.
The cryptocurrency wallet targeting is comprehensive, covering over 100 browser wallet extensions including MetaMask, Phantom, Coinbase Wallet, Trust Wallet, Ledger Live, Trezor, Exodus, and dozens more across Ethereum, Solana, Cosmos, Polkadot, Cardano, TON, Bitcoin Ordinals, and virtually every major blockchain ecosystem. The malware copies entire extension data directories for each wallet found.
Cloud credentials are also targeted. If AWS CLI, Azure CLI, or Google Cloud SDK are configured on the machine, the malware copies credential files along with SSH keys and kubeconfig files, potentially providing access to entire cloud infrastructures.
Messaging tokens for Discord, Telegram's tdata directory, and Steam authentication files are also exfiltrated.
DLL Injection into Browser Processes
The Python payload contains a base64-encoded, XOR-encrypted Windows DLL that gets injected into browser processes using NT native APIs including NtAllocateVirtualMemory, NtWriteVirtualMemory, NtProtectVirtualMemory, and NtCreateThreadEx.
The malware includes a full PE parser that walks the export table searching for a function called "Initialize" as the entry point after injection.
Dual C2 Infrastructure
Stolen data is zipped and uploaded to attacker-controlled Appwrite storage buckets. The malware maintains two C2 servers: a primary endpoint in New York and a backup in Frankfurt. For large files, data is chunked into 5MB pieces and uploaded sequentially, with files over 50MB split into 45MB parts.
The malware checks for a .gwagon_status file in the user's home directory containing an execution counter. If the victim has been infected twice already, it stops running to avoid redundant data theft.
Remediation Steps
Organizations and developers who installed ansi-universal-ui should immediately remove the package and delete node_modules, check for the .gwagon_status file in the home directory as an infection indicator, rotate all browser-saved passwords, revoke and regenerate tokens for any cryptocurrency wallet browser extensions, rotate AWS, Azure, and GCP credentials, regenerate SSH keys, and invalidate Discord and Telegram sessions.
Indicators of Compromise
The malicious package name is ansi-universal-ui with malicious versions 1.3.5, 1.3.6, 1.3.7, 1.4.0, and 1.4.1. Network indicators include C2 endpoints at nyc.cloud.appwrite[.]io and fra.cloud.appwrite[.]io with Appwrite Project IDs 6886229e003d46469fab and 6968e9e9000ee4ac710c respectively. The filesystem indicator is the presence of ~/.gwagon_status which serves as the execution counter.



