Microsoft and Global Police Disrupt RedVDS, a Scaled Engine Behind Massive BEC Fraud

A coordinated operation led by Microsoft and international law enforcement has dismantled RedVDS, a major infrastructure provider behind large-scale business email compromise (BEC) fraud worldwide.
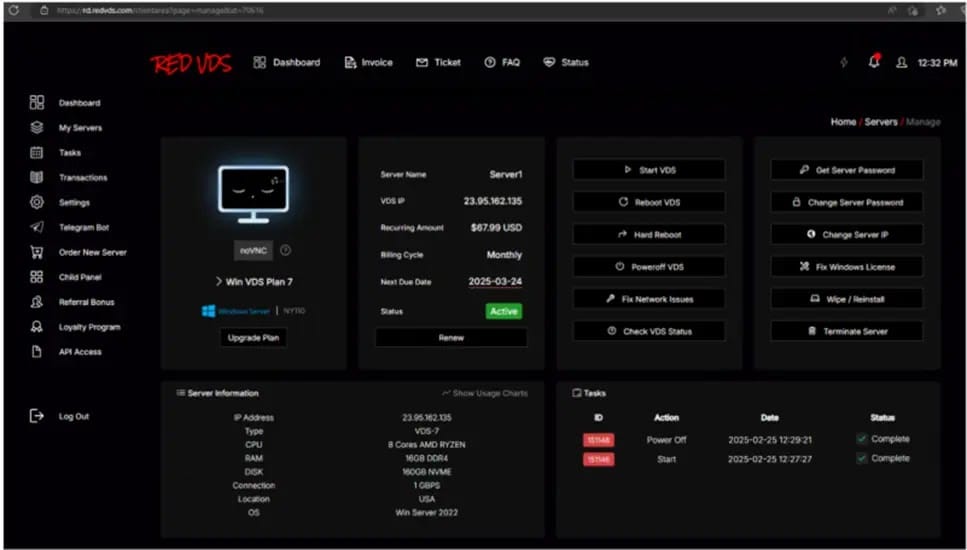
RedVDS functioned as a low-cost, subscription-based cybercrime service, offering criminals disposable virtual machines that appeared online as legitimate Windows systems. These rented environments allowed attackers to blend into normal internet traffic while running phishing campaigns, hosting fraudulent login portals, and executing payment diversion schemes.
Using RedVDS infrastructure, threat actors targeted organizations across finance, real estate, healthcare, and manufacturing. The attack model was straightforward but highly effective. Criminals first sent tailored phishing emails from RedVDS-hosted machines, harvesting credentials for Microsoft 365 and other email platforms.
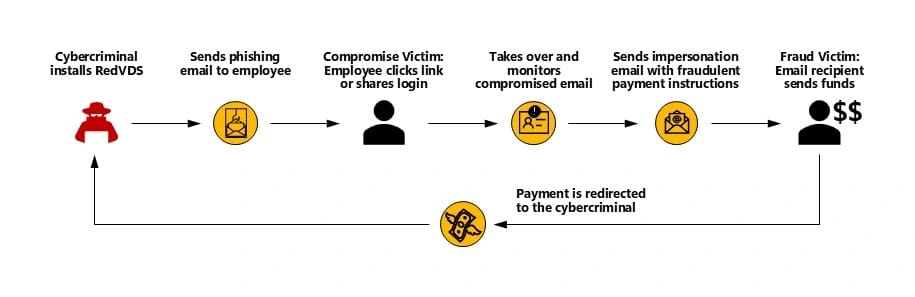
After gaining access to a mailbox, attackers avoided immediate action. Instead, they silently monitored real conversations between employees, vendors, and customers. When they spotted discussions involving invoices, wire transfers, or closing documents, they intervened at precisely the right moment—sending fraudulent replies that replaced legitimate banking details with accounts under their control.
Microsoft analysts found that RedVDS significantly amplified these scams by combining high-volume infrastructure with AI-assisted tools. These tools generated convincing phishing emails, synthetic voice messages, and even deepfake videos to reinforce the fraud. At peak activity, more than 2,600 RedVDS virtual machines sent roughly one million phishing emails per day to Microsoft customers alone, contributing to the compromise or misuse of access at over 191,000 organizations globally.
The platform was also heavily used in real estate fraud. Attackers hijacked mailboxes belonging to agents and title companies, then sent falsified closing instructions to buyers. In many cases, victims transferred life-changing sums of money to mule accounts within minutes of receiving the spoofed messages.
Technically, the BEC operation followed a repeatable script. Attackers spun up a RedVDS instance, deployed basic automation, validated stolen credentials, and scanned inboxes for payment-related conversations. Once a promising thread was identified, they injected fraudulent replies from the compromised account, often reusing authentic signatures and prior message context to avoid suspicion.
The joint takedown disrupted this ecosystem by seizing RedVDS domains, cutting off its payment channels, and removing a critical piece of shared criminal infrastructure. Microsoft emphasized that its legal actions were closely coordinated with global law enforcement partners.
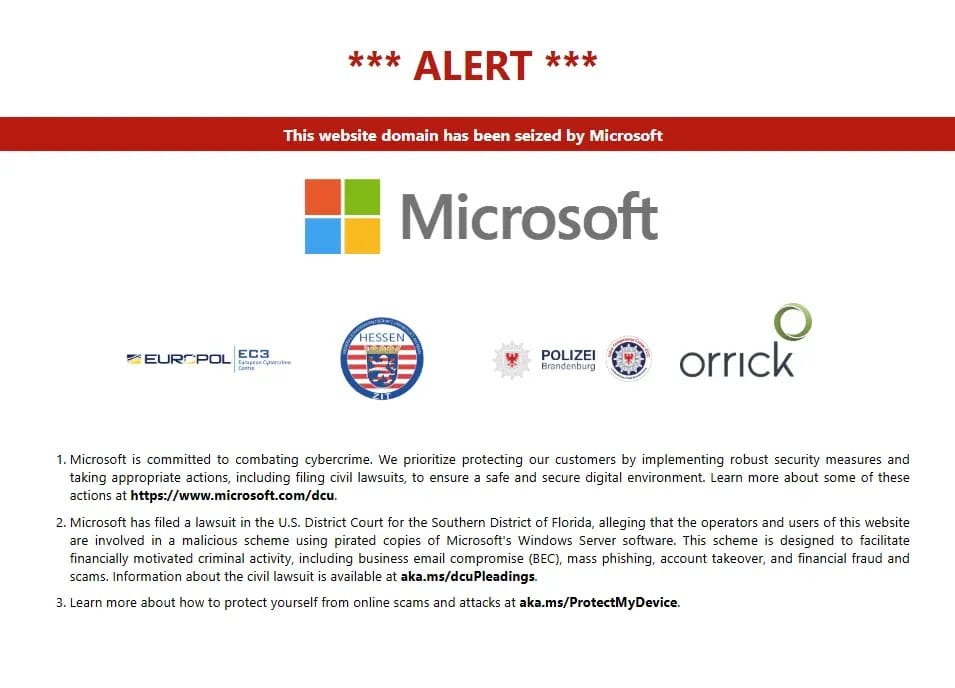
The operation highlights a broader defensive lesson: dismantling common infrastructure used by cybercriminals can be more effective than focusing solely on individual compromised accounts. By targeting the platforms that enable scale and anonymity, defenders can meaningfully reduce the global BEC attack surface.



