Microsoft January 2026 Patch Tuesday: 114 Vulnerabilities Fixed Including 3 Zero-Days
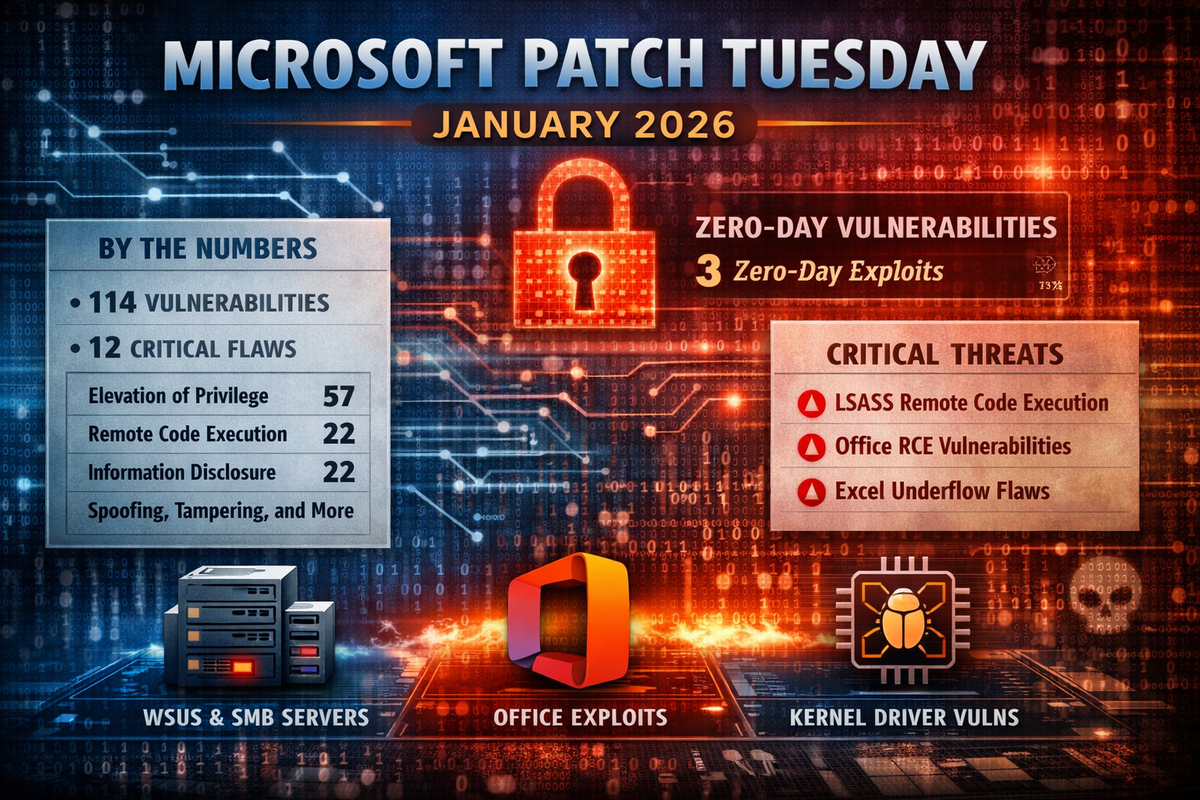
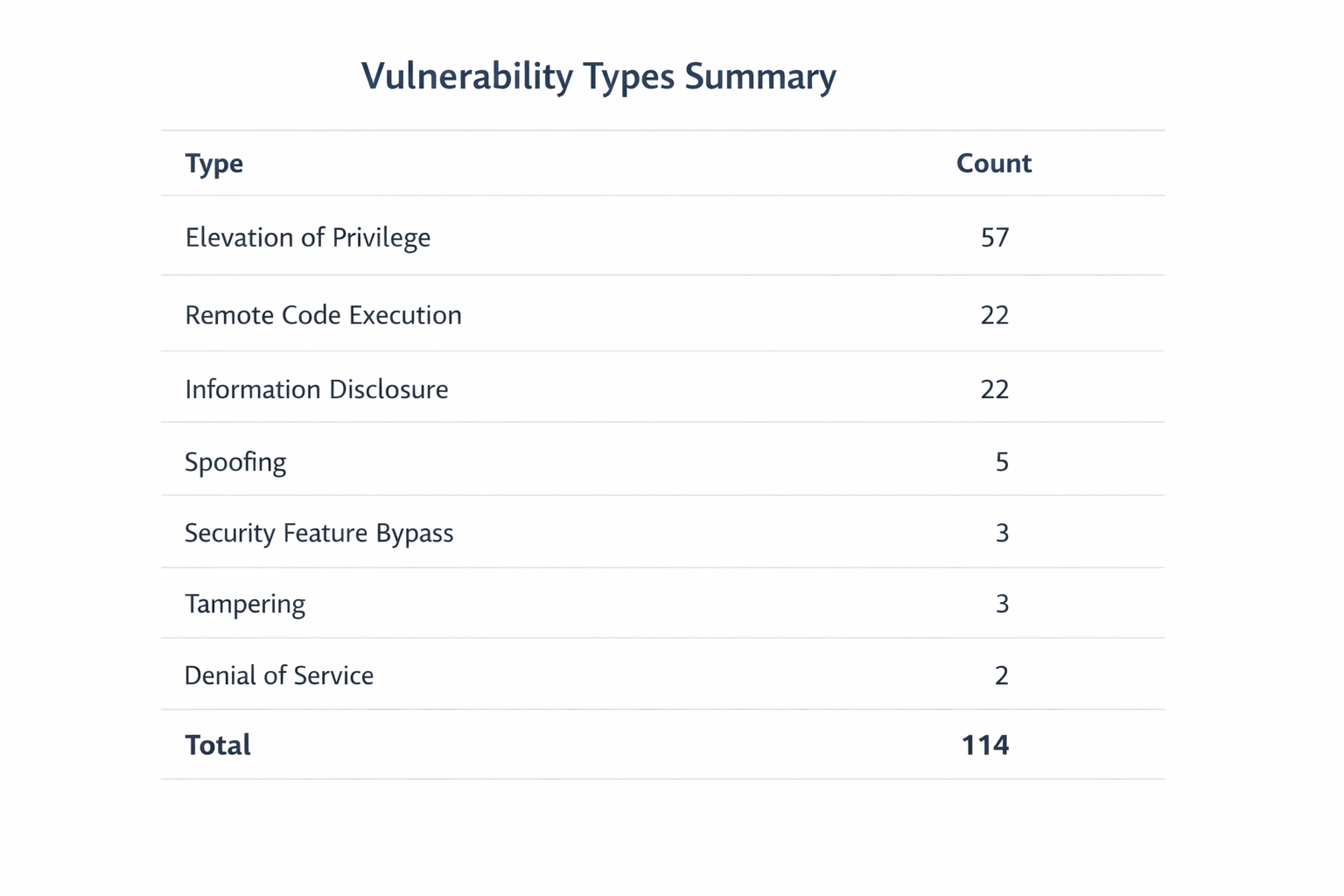
Microsoft's first Patch Tuesday of 2026 addresses 114 security vulnerabilities across Windows, Office, and related services. The release includes 12 critical-severity flaws and patches for three zero-day vulnerabilities.
By the Numbers
Zero-Days Patched
Three zero-day vulnerabilities were addressed in this release:
- CVE-2026-20805 - Desktop Window Manager information disclosure flaw allowing unauthorized access to sensitive data
- CVE-2026-21265 - Windows Digital Media elevation of privilege bug commonly used in attack chains
- CVE-2023-31096 - Legacy Agere Soft Modem driver elevation of privilege issue included in cumulative updates
Critical Vulnerabilities
The most severe flaws patched this month include:
- CVE-2026-20854 - Use-after-free in Windows LSASS enabling remote code execution over the network
- CVE-2026-20944 - Out-of-bounds read in Microsoft Word allowing RCE
- CVE-2026-20953 / CVE-2026-20952 - Use-after-free vulnerabilities in Microsoft Office
- CVE-2026-20955 / CVE-2026-20957 - Pointer and integer underflow issues in Microsoft Excel
- CVE-2026-20822 - Graphics Component elevation of privilege via use-after-free
- CVE-2026-20876 - VBS Enclave elevation of privilege
Patch Priority
Administrators should prioritise:
- Internet-facing systems including WSUS servers (CVE-2026-20856) and SMB servers
- Office endpoints due to multiple critical RCE flaws
- Systems running affected kernel drivers
Testing in staging environments is recommended due to potential regressions in drivers like Cloud Files Mini Filter. Monitor CISA KEV for any rapid additions as zero-days may see active exploitation.



