Microsoft Teams Gets External Domain Anomaly Detection to Combat Social Engineering Attacks

Microsoft is introducing the External Domains Anomalies Report for Teams, a security feature designed to help administrators identify suspicious external communications before they escalate into breaches.
The tool, scheduled for global rollout in February 2026, addresses a critical gap as threat actors increasingly exploit Teams for social engineering campaigns.
How It Works
The feature uses pattern analysis to establish baselines of normal communication behavior and flags deviations that could indicate security concerns. The system monitors three key indicators:
- Sudden spikes in messaging volume with external parties
- First-time communications with previously unknown domains
- Unusual engagement patterns that deviate from established norms
When anomalies are detected, administrators receive actionable insights through a dedicated report, enabling security teams to investigate risky interactions before data exfiltration occurs.
Why It Matters
The feature arrives as ransomware groups have intensified social engineering attacks through Teams. Black Basta has been observed flooding victim inboxes with thousands of emails, then using Teams chats to pose as IT help desk staff and convince users to install remote access tools like AnyDesk.
In late October 2024, the group added targeted users to Teams chats with external users operating from newly created Entra ID tenants designed to appear as legitimate support personnel—ultimately gaining remote access to victim machines.
Availability
The External Domains Anomalies Report will roll out to standard multi-tenant environments on the web platform starting February 2026 under Microsoft 365 Roadmap ID 536572.
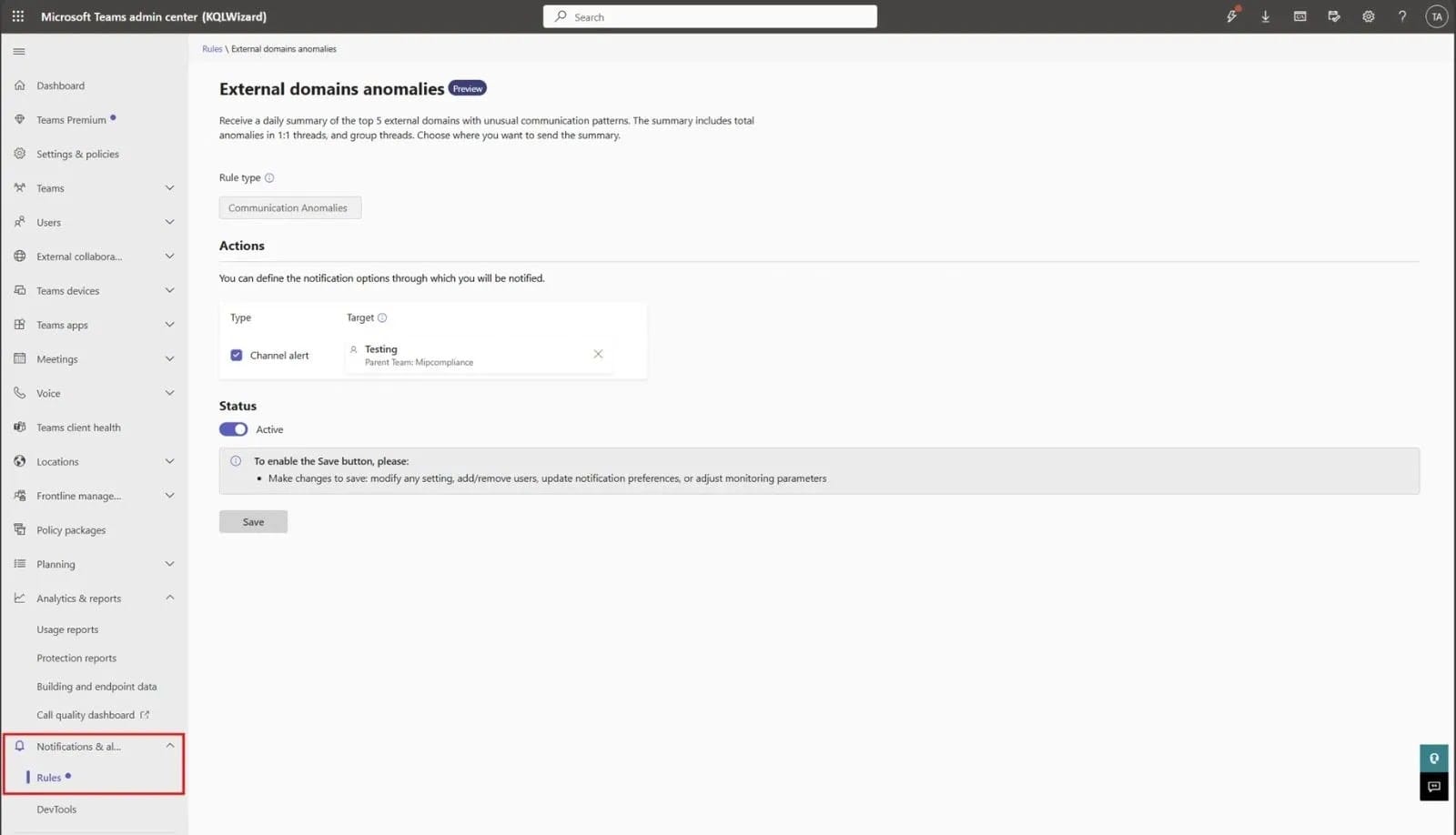
Organizations can enable the feature through the Teams admin center:
- Navigate to Notifications & alerts → Rules
- Select External domain anomalies
- Change status to Active
- Choose a Teams channel to receive alert notifications
This capability builds on earlier Teams security enhancements, including warnings for malicious URLs and blocking risky file types in chats.



