Multi-Stage Campaign Delivers Amnesia RAT and Ransomware Using Defendnot to Disable Microsoft Defender

A sophisticated multi-stage phishing campaign is targeting Russian users with Amnesia RAT and ransomware derived from the Hakuna Matata family, leveraging legitimate cloud infrastructure and a novel technique to disable Microsoft Defender.
The campaign, documented by Fortinet FortiGuard Labs, stands out for its abuse of defendnot—a tool that tricks Windows Security Center into believing another antivirus product is installed, causing Defender to disable itself to avoid conflicts.
Attack Chain
The infection begins with business-themed decoy documents delivered in compressed archives containing malicious Windows shortcut (LNK) files. The LNK files use double extensions with Russian-language filenames to masquerade as text files.
When executed, the shortcut runs a PowerShell command that retrieves a loader script from a GitHub repository. The attackers separate their infrastructure—hosting scripts on GitHub while staging binary payloads on Dropbox—to complicate takedown efforts.
The first-stage loader establishes a foothold, hides evidence of malicious activity, and notifies the operator via Telegram Bot API that execution was successful. After a deliberate 444-second delay, it retrieves a heavily obfuscated Visual Basic Script that assembles the next-stage payload directly in memory, avoiding disk artifacts.
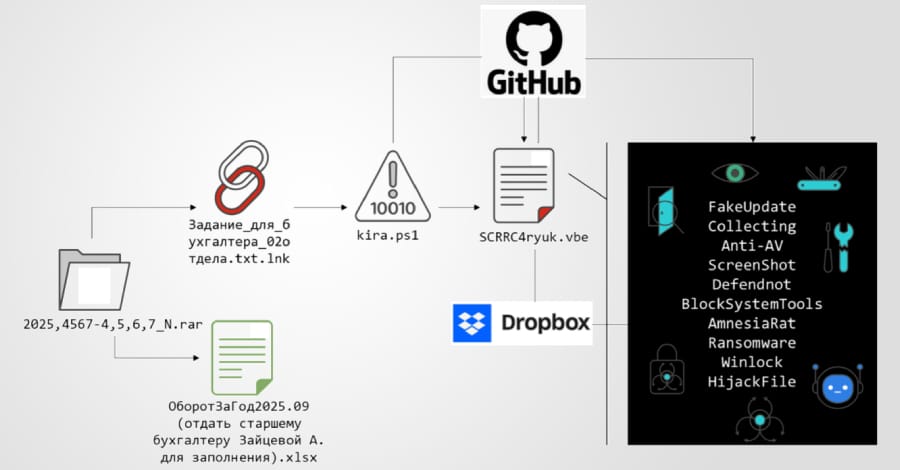
Disabling Defender
Before deploying final payloads, the malware systematically neutralizes endpoint protection:
- Configures Defender exclusions for ProgramData, Program Files, Desktop, Downloads, and temporary directories
- Uses PowerShell to disable additional Defender protection components
- Deploys defendnot to register a fake antivirus product, causing Defender to disable itself
- Disables Windows administrative and diagnostic tools via Registry manipulation
Amnesia RAT Capabilities
The primary payload, Amnesia RAT, is retrieved from Dropbox and provides comprehensive data theft and remote control capabilities:
- Steals credentials from browsers, cryptocurrency wallets, Discord, Steam, and Telegram
- Captures screenshots every 30 seconds, webcam images, and microphone audio
- Monitors clipboard and active window titles
- Enables full remote interaction including shell command execution and arbitrary payload deployment
- Exfiltrates data via Telegram Bot APIs, with larger datasets uploaded to third-party hosting services
Ransomware Component
The second payload is ransomware derived from the Hakuna Matata family, configured to encrypt documents, archives, images, media, source code, and application assets. Before encryption, it terminates processes that could interfere with its operation.
The ransomware also monitors clipboard contents and silently replaces cryptocurrency wallet addresses with attacker-controlled wallets to hijack transactions. The attack chain concludes with WinLocker deployment to restrict user interaction.
Related Activity
Fortinet notes connections to other campaigns targeting Russian organizations:
- Operation DupeHike: Threat actor UNG0902 targeting HR and payroll departments with the DUPERUNNER implant, loading AdaptixC2 framework
- Paper Werewolf: Using AI-generated decoys and Excel XLL add-ins to deliver the EchoGather backdoor
Mitigations
Microsoft recommends enabling Tamper Protection to prevent unauthorized changes to Defender settings and monitoring for suspicious API calls or Defender service changes.



