New Osiris Ransomware Deployed by Attackers With Ties to Inc Ransomware Group
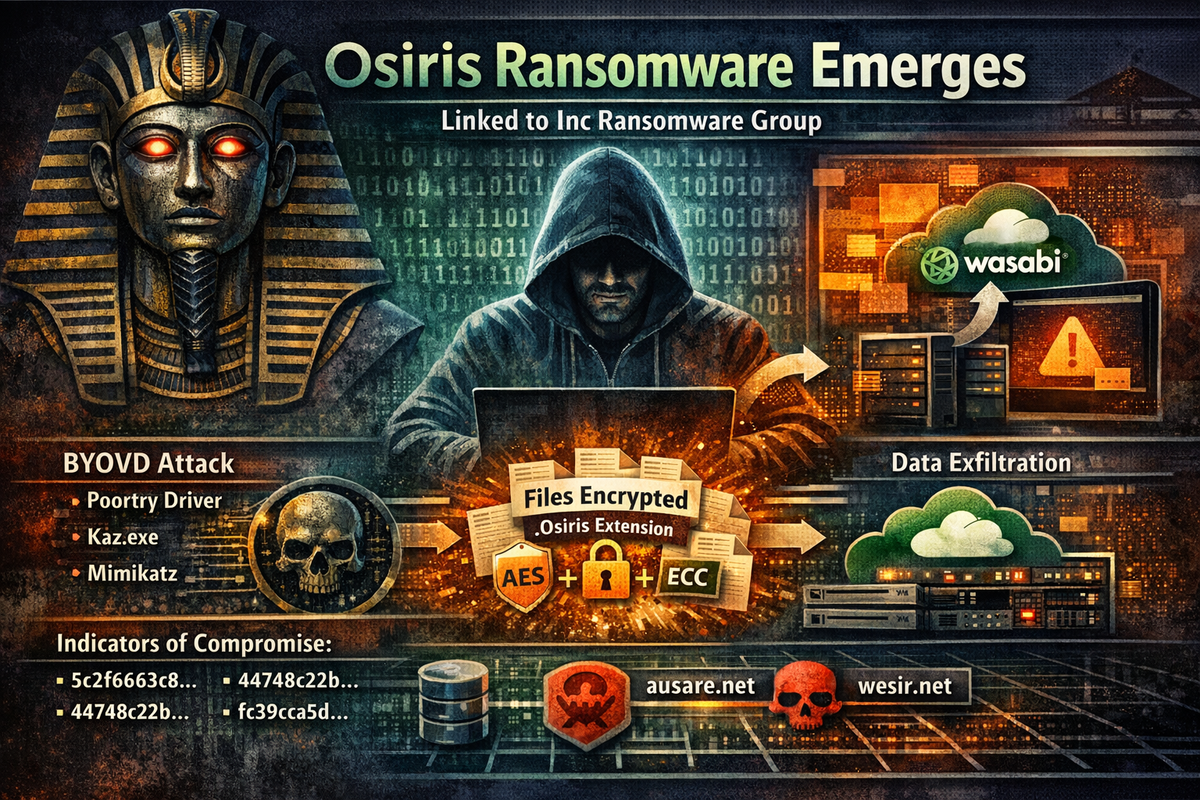
A previously undocumented ransomware family dubbed Osiris has emerged in attacks targeting enterprise environments, with technical evidence suggesting the operators may have ties to the Inc ransomware group.
Symantec's Threat Hunter Team identified the new strain during an investigation into an attack against a major food service franchisee operator in Southeast Asia in November 2025. Despite sharing a name with a 2016 Locky variant, researchers confirmed this is an entirely new ransomware family with no connection to the earlier threat.
Inc Ransomware Connections
Several operational indicators point to potential links with Inc ransomware actors. The attackers exfiltrated data to Wasabi cloud storage buckets—a tactic previously observed in Inc ransomware attacks from October 2025. More notably, they deployed a version of Mimikatz using the filename "kaz.exe," matching a tool previously used by Inc operators.
These overlaps could indicate that Inc tactics are being emulated, or that a former Inc affiliate has migrated to the new Osiris operation. Whether Osiris operates as a ransomware-as-a-service (RaaS) remains unknown.
BYOVD Attack Chain
The attackers employed a bring-your-own-vulnerable-driver (BYOVD) attack using the Poortry driver—also known as Abyssworker—to disable security software. The malicious driver masqueraded as a Malwarebytes anti-exploit component.
Poortry, first documented by Mandiant in 2022, is notable for apparently being a custom-developed driver that attackers successfully got signed, rather than exploiting a legitimate vulnerable driver. It was previously associated with Medusa ransomware attacks throughout 2024 and 2025.
The attackers also deployed KillAV, a tool for terminating security processes via vulnerable drivers, alongside a modified version of Rustdesk that masqueraded as "WinZip Remote Desktop" to evade detection.
Technical Capabilities
Osiris employs a hybrid encryption scheme combining ECC with AES-128-CTR, generating unique AES keys per file. The ransomware appends the .Osiris extension to encrypted files and deletes volume shadow copies to prevent recovery.
The payload targets SQL databases, backup services, and common business applications including Microsoft Office, Outlook, and Veeam backup solutions. It accepts command-line parameters for targeted encryption, including options to disable Hyper-V virtual machines and delete their configuration files.
Indicators of Compromise
Osiris ransomware: 5c2f663c8369af70f727cccf6e19248c50d7c157fe9e4db220fbe2b73f75c713
Poortry driver: 44748c22baec61a0a3bd68b5739736fa15c479a3b28c1a0f9324823fc4e3fe34
Mimikatz (kaz.exe): fc39cca5d71b1a9ed3c71cca6f1b86cfe03466624ad78cdb57580dba90847851
Network indicators: ausare[.]net, wesir[.]net
Full IOC list available in Symantec's research report.



