North Korean UNC1069 Deploys AI-Generated Deepfakes and Seven Malware Families to Target Crypto Sector

Google Mandiant has detailed a sophisticated North Korean intrusion campaign in which the threat group UNC1069 used AI-generated deepfake video calls, compromised Telegram accounts, and ClickFix social engineering to deploy seven unique malware families against cryptocurrency sector targets.
UNC1069 — also tracked as CryptoCore and MASAN — has been active since at least 2018 and has shifted its focus from traditional finance to Web3 targets including centralized exchanges, crypto startups, venture capital firms, and software developers at financial institutions.
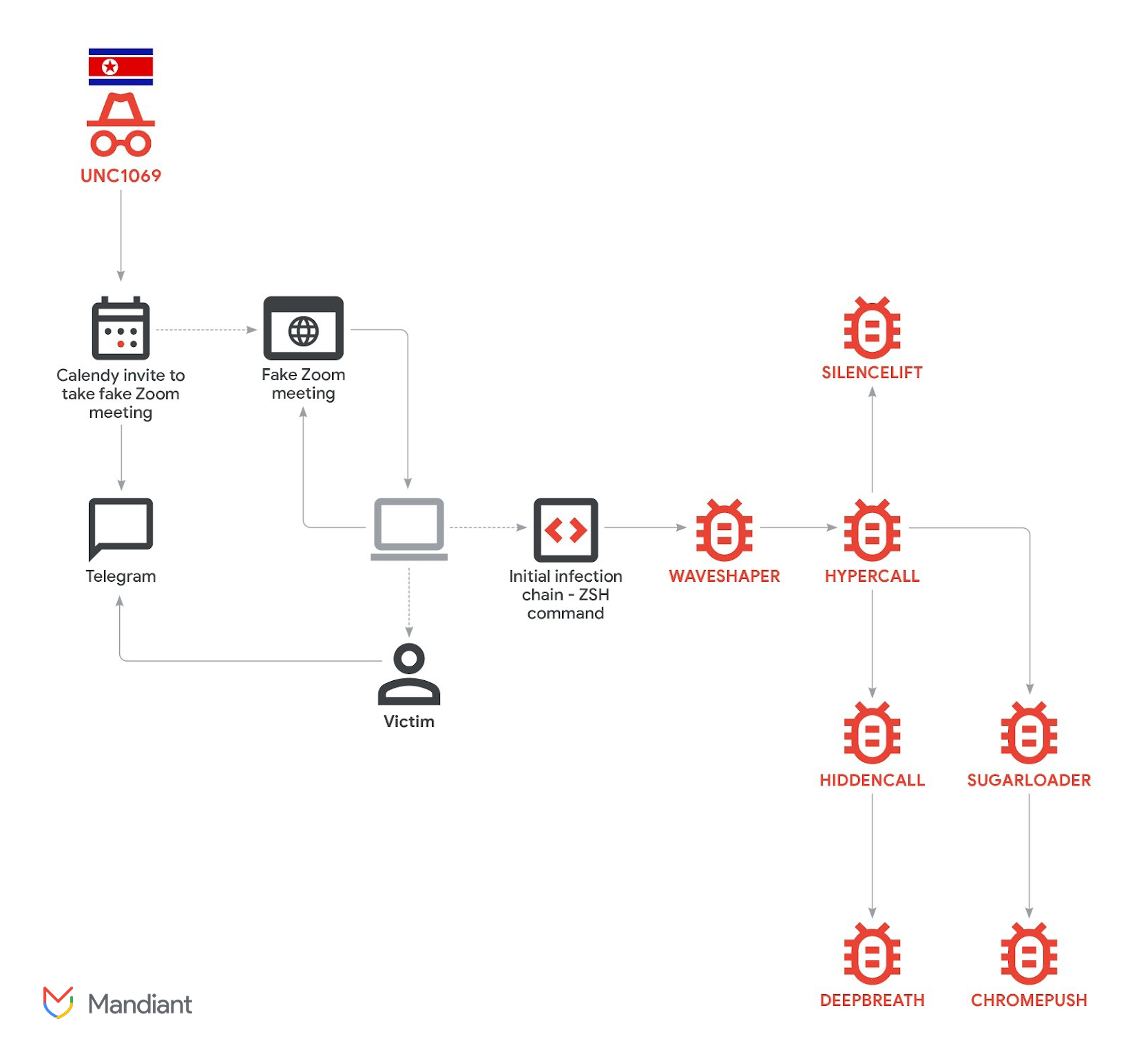
The Attack Chain
The intrusion begins on Telegram, where UNC1069 operators impersonate venture capitalists — in some cases using compromised accounts belonging to legitimate entrepreneurs and startup founders. After establishing contact, they schedule a 30-minute meeting via Calendly.
The meeting link redirects victims to a fake Zoom website (zoom.uswe05[.]us) that presents a convincing video call interface. Victims are prompted to enable their camera and enter their name. Once they "join," they see what appears to be a live meeting with other participants.
The video feeds are either AI-generated deepfakes or real recordings stolen from previous victims. Kaspersky, which tracks the same campaign as GhostCall, documented how victim webcam footage was unknowingly recorded, uploaded to attacker infrastructure, and replayed to deceive future targets. When the recording ends, the page transitions to displaying the participant's profile image to maintain the illusion.
The attack escalates when the victim is shown a fake audio error and prompted to run a ClickFix-style troubleshooting command. On macOS, this delivers an AppleScript that drops the initial payload.
Seven Malware Families
The documented intrusion deployed an unusually dense toolset on a single compromised host:
WAVESHAPER — A C++ executable that collects system information and delivers HYPERCALL, a Go-based downloader that serves as the staging platform for additional payloads.
HIDDENCALL — A Golang backdoor providing hands-on-keyboard access to the compromised system. Deploys DEEPBREATH for data theft.
DEEPBREATH — A Swift-based data miner that manipulates macOS's Transparency, Consent, and Control (TCC) database to bypass file system protections. Steals iCloud Keychain credentials, browser data from Chrome, Brave, and Edge, Telegram messages, and Apple Notes content.
SUGARLOADER — A known C++ downloader used to deploy CHROMEPUSH.
CHROMEPUSH — A C++ browser extension disguised as a Google Docs offline editing tool. Deployed to Chrome and Brave, it records keystrokes, captures credentials, and exfiltrates browser cookies.
SILENCELIFT — A minimalist C/C++ backdoor that exfiltrates system information to attacker C2 infrastructure.
HYPERCALL — The Go-based downloader that orchestrates delivery of the secondary payloads.
AI-Powered Social Engineering
UNC1069's use of AI tools extends beyond the deepfake video calls. Google Threat Intelligence Group previously documented the group using Gemini to generate cryptocurrency-themed lure content and attempting to develop cryptocurrency-stealing code. The group has also leveraged deepfake images mimicking real individuals in the crypto industry to distribute the BIGMACHO backdoor disguised as a Zoom SDK.
Recommendation
Cryptocurrency organizations and developers should treat unsolicited Telegram messages from investors with extreme suspicion — even from seemingly legitimate accounts. Verify meeting invitations through separate channels. Never execute troubleshooting commands from video conferencing prompts. macOS users should monitor for TCC database modifications and unexpected browser extensions. Implement hardware-based MFA and multi-signature wallets. The volume of tooling deployed indicates a highly determined adversary willing to invest significant resources in individual targets.



